华为实验2
2015-06-08 00:00
190 查看
大家好
今天的实验是配置
primary VLAN
和
secondary VLAN
主附
vlan
一般用于一个网络段的情况,主
vlan
和子
vlan
间可以访问,
而子
vlan
之间是不能访问的。就比如说
总经理所在的
vlan
可以访问任何部门的
vlan
而部门之间却不能互相访问。
具体实验步骤如下:
SW1
:
<Quidway>sys
Enter system view, return to user view with Ctrl+Z.
[Quidway]sysname dongli
[dongli]super password dongli
[dongli]user int vty 0 4
[dongli-ui-vty0-4]authentication-mode password
[dongli-ui-vty0-4]set authentication-mode password sim 222
[dongli-ui-vty0-4]user privilege 3
[dongli-ui-vty0-4]quit
[dongli]vlan 2
[dongli-vlan2]port e0/3
[dongli-vlan2]vlan 3
[dongli-vlan3]port e0/6
[dongli-vlan3]vlan 4
[dongli-vlan4]port e0/8
[dongli-vlan4]quit
[dongli]vlan 4
[dongli-vlan4]vlan 2
[dongli-vlan2]isolate-user-vlan enable
―――――――设为主
vlan
[dongli-vlan2]
[dongli-vlan2]quit
[dongli]isolate-user-vlan 2 secondary 3,4
――――――――――设
vlan3
,
4
为辅
vlan
[dongli]int e0/1
[dongli-Ethernet0/1]port link-type trunk
[dongli-Ethernet0/1]port trunk permit vlan all
[dongli-Ethernet0/1]quit
[dongli]
SW2
:
<Quidway>sys
Enter system view, return to user view with Ctrl+Z.
[Quidway]vlan 2
[Quidway-vlan2]port e0/3
[Quidway-vlan2]vlan 3
[Quidway-vlan3]port e0/6
[Quidway-vlan3]vlan 4
[Quidway-vlan4]port e0/8
[Quidway-vlan4]quit
[Quidway]vlan 2
[Quidway-vlan2]isolate-user-vlan enable
[Quidway-vlan2]quit
[Quidway]isolate-user-vlan 2 secondary 3,4
[Quidway]quit
<Quidway>sys
Enter system view, return to user view with Ctrl+Z.
[Quidway]int e0/1
[Quidway-Ethernet0/1]port link-type trunk
[Quidway-Ethernet0/1]port trunk permit vlan all
[Quidway-Ethernet0/1]quit
[Quidway]
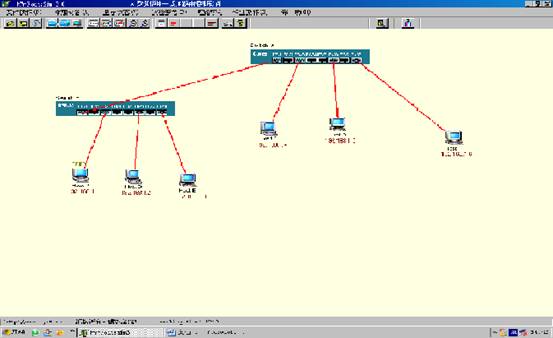
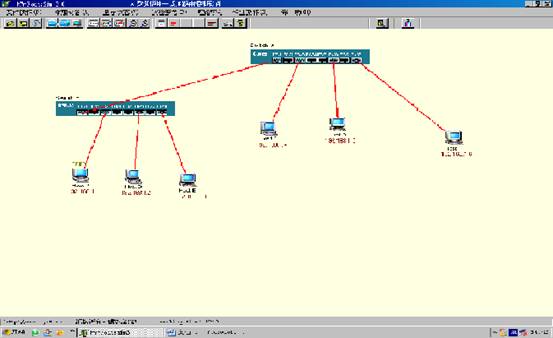
PC1 192.168.1.1 PC2 192.168.1.2 PC3 192.168.1.3 PC4 192.168.1.4 PC5 192.168.1.5 PC6 192.168.1.6
实验结果:
PC1
:
root@PCA root]# ifconfig eth0 192.168.1.1 netmask 255.255.255.0
[root@PCA root]# ping 192.168.1.2
64 bytes from 192.168.1.1: icmp_seq=1 ttl=128 time=0.207 ms
64 bytes from 192.168.1.1: icmp_seq=1 ttl=128 time=0.100 ms
64 bytes from 192.168.1.1: icmp_seq=1 ttl=128 time=0.96 ms
64 bytes from 192.168.1.1: icmp_seq=1 ttl=128 time=0.96 ms
4packets transmitted, 4 received, 0% loss, time 2000ms
PC2
:
root@PCB root]# ifconfig eth0 192.168.1.2 netmask 255.255.255.0
[root@PCB root]# ping 192.168.1.1
64 bytes from 192.168.1.2: icmp_seq=1 ttl=128 time=0.207 ms
64 bytes from 192.168.1.2: icmp_seq=1 ttl=128 time=0.100 ms
64 bytes from 192.168.1.2: icmp_seq=1 ttl=128 time=0.96 ms
64 bytes from 192.168.1.2: icmp_seq=1 ttl=128 time=0.96 ms
4packets transmitted, 4 received, 0% loss, time 2000ms
[root@PCB root]# ping 192.168.1.3
From 192.168.1.2 icmp_seq=1 Destination Host Unreachable
From 192.168.1.2 icmp_seq=1 Destination Host Unreachable
From 192.168.1.2 icmp_seq=1 Destination Host Unreachable
From 192.168.1.2 icmp_seq=1 Destination Host Unreachable
4packets transmitted, 0 received, 100% loss, time 2000ms
[root@PCB root]#
实验成功
今天就讲到着
有不明白的请加
768865545
飘云
支持华为
!!!!!!!!!!!!!!!!!!!!!!!
本文出自 “nfs_dongli的博客” 博客,请务必保留此出处http://hackerdl.blog.51cto.com/867412/236155
今天的实验是配置
primary VLAN
和
secondary VLAN
主附
vlan
一般用于一个网络段的情况,主
vlan
和子
vlan
间可以访问,
而子
vlan
之间是不能访问的。就比如说
总经理所在的
vlan
可以访问任何部门的
vlan
而部门之间却不能互相访问。
具体实验步骤如下:
SW1
:
<Quidway>sys
Enter system view, return to user view with Ctrl+Z.
[Quidway]sysname dongli
[dongli]super password dongli
[dongli]user int vty 0 4
[dongli-ui-vty0-4]authentication-mode password
[dongli-ui-vty0-4]set authentication-mode password sim 222
[dongli-ui-vty0-4]user privilege 3
[dongli-ui-vty0-4]quit
[dongli]vlan 2
[dongli-vlan2]port e0/3
[dongli-vlan2]vlan 3
[dongli-vlan3]port e0/6
[dongli-vlan3]vlan 4
[dongli-vlan4]port e0/8
[dongli-vlan4]quit
[dongli]vlan 4
[dongli-vlan4]vlan 2
[dongli-vlan2]isolate-user-vlan enable
―――――――设为主
vlan
[dongli-vlan2]
[dongli-vlan2]quit
[dongli]isolate-user-vlan 2 secondary 3,4
――――――――――设
vlan3
,
4
为辅
vlan
[dongli]int e0/1
[dongli-Ethernet0/1]port link-type trunk
[dongli-Ethernet0/1]port trunk permit vlan all
[dongli-Ethernet0/1]quit
[dongli]
SW2
:
<Quidway>sys
Enter system view, return to user view with Ctrl+Z.
[Quidway]vlan 2
[Quidway-vlan2]port e0/3
[Quidway-vlan2]vlan 3
[Quidway-vlan3]port e0/6
[Quidway-vlan3]vlan 4
[Quidway-vlan4]port e0/8
[Quidway-vlan4]quit
[Quidway]vlan 2
[Quidway-vlan2]isolate-user-vlan enable
[Quidway-vlan2]quit
[Quidway]isolate-user-vlan 2 secondary 3,4
[Quidway]quit
<Quidway>sys
Enter system view, return to user view with Ctrl+Z.
[Quidway]int e0/1
[Quidway-Ethernet0/1]port link-type trunk
[Quidway-Ethernet0/1]port trunk permit vlan all
[Quidway-Ethernet0/1]quit
[Quidway]
PC1 192.168.1.1 PC2 192.168.1.2 PC3 192.168.1.3 PC4 192.168.1.4 PC5 192.168.1.5 PC6 192.168.1.6
实验结果:
PC1
:
root@PCA root]# ifconfig eth0 192.168.1.1 netmask 255.255.255.0
[root@PCA root]# ping 192.168.1.2
64 bytes from 192.168.1.1: icmp_seq=1 ttl=128 time=0.207 ms
64 bytes from 192.168.1.1: icmp_seq=1 ttl=128 time=0.100 ms
64 bytes from 192.168.1.1: icmp_seq=1 ttl=128 time=0.96 ms
64 bytes from 192.168.1.1: icmp_seq=1 ttl=128 time=0.96 ms
4packets transmitted, 4 received, 0% loss, time 2000ms
PC2
:
root@PCB root]# ifconfig eth0 192.168.1.2 netmask 255.255.255.0
[root@PCB root]# ping 192.168.1.1
64 bytes from 192.168.1.2: icmp_seq=1 ttl=128 time=0.207 ms
64 bytes from 192.168.1.2: icmp_seq=1 ttl=128 time=0.100 ms
64 bytes from 192.168.1.2: icmp_seq=1 ttl=128 time=0.96 ms
64 bytes from 192.168.1.2: icmp_seq=1 ttl=128 time=0.96 ms
4packets transmitted, 4 received, 0% loss, time 2000ms
[root@PCB root]# ping 192.168.1.3
From 192.168.1.2 icmp_seq=1 Destination Host Unreachable
From 192.168.1.2 icmp_seq=1 Destination Host Unreachable
From 192.168.1.2 icmp_seq=1 Destination Host Unreachable
From 192.168.1.2 icmp_seq=1 Destination Host Unreachable
4packets transmitted, 0 received, 100% loss, time 2000ms
[root@PCB root]#
实验成功
今天就讲到着
有不明白的请加
768865545
飘云
支持华为
!!!!!!!!!!!!!!!!!!!!!!!
本文出自 “nfs_dongli的博客” 博客,请务必保留此出处http://hackerdl.blog.51cto.com/867412/236155
相关文章推荐
- 职场中越皮实的员工,越招领导喜欢!
- 最近发现一款超牛的记单词软件,分享一下
- 启动Agent 报错,-4 错误
- 桌面虚拟化技术:旧风潮再次来袭
- 0403-027 The parameter list is too long
- 公司的网络为何如此缓慢
- 高效访问Internet-启用ISA Server的缓存
- IDC机房实战MRTG
- 匹配也惹祸
- IP 防盗有法
- 封Q进行时
- 用vsftp快速搭建ftp服务器
- 快速部署远程同步服务Rsync
- 某虚拟化项目中思科与华为交换机链路聚合互连案例
- 第四章 交换机划分Vlan配置
- 第一章 认识Packet Tracer软件
- 远程登录华为防火墙以及用户权限的修改
- 华为防火墙基础配置
