某些TP-Link路由器可以被远程获取密码
2014-01-19 17:59
579 查看
HOW I SAVED YOUR A** FROM THE ZYNOS (ROM-0) ATTACK !! ( FULL DISCLOSURE )
Hello everyone, I just wanted to discuss some vulnerability I found and exploited for GOODNESS .. just so that SCRIPT KIDIES won’t attack your home/business network .Well, in Algeria the main ISP ( Algerie Telecom ) provide you with a router when you pay for an internet plan. So you can conclude that every subscriber is using that router . TD-W8951ND is one of them, I did some ip scanning and I found that every router is using ZYXEL embedded firmware.
Analysis :
Let’s download an update and take a look at it and try to find some vulnerabilities. ( http://www.tp-link.com/Resources/software/TD-W8951ND_V3.0_110729_FI.rar )
The ras file is in LIF format !! …
Hmmm let’s put that file for Binwalk test for God’s sake ! ( check :http://code.google.com/p/binwalk/wiki/Installation for more informations on how to install it ).
This is what Binwalk told me about that file :
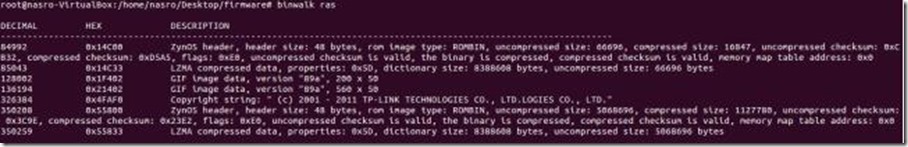
You can clearly see and confirm that the router is using zynos firmware. We can also see that there is two blocks of LZMA compressed data … let’s extract them and have a look.
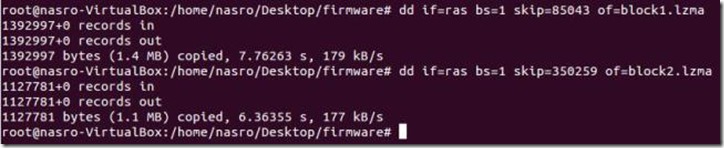
The problem is that when I tried to decompress the two blocks I get an error : ” Compressed data is corrupt “
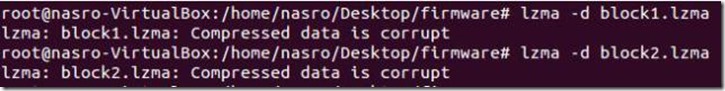
Hmm, first the “ras” file was in LIF format .. and now the lzma compress blocks are corrupted !!
I googled this and tried to find a solution for this, FOUND NOTHING . How am I going to solve this ??
One idea came in my mind .. “Strings” command and here is what I got :

Aaaah ! so the blocks aren’t compressed with LZMA or anything ! and the whole “ras” firmware file is just big chunk of data in clear text.
Ok, let’s try and find some useful STRINGS …
After some time searching “I” didn’t find the useful thing that will help us find vulnerabilities on the firmware !!
I didn’t give up …
I just was thinking and questioning :
Me: What do you want from this firmware file !
Me: I want to find remote vulnerabilities that will help me extract the “admin” password.
Me: Does the web interface let you save the current configuration ?
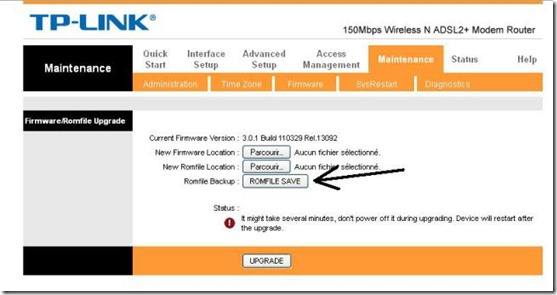
Me: yes !!
Me: Is the page password protected ?

Me: No !!! I tired to access that page on a different IP and it didn’t require a passowrd !
Ok, enough questions haha ..
Now, when I activated TamperData and clicked “ROMFILE SAVE” I’ve found out that the rom-0 file is located on “IP/rom-0″ and the directory isn’t password protected or anything.
So we are able to download the configuration file which contains the “admin” password. I took a look at rom-0 file and couldn’t figure out how to reverse-engineer it, and when you don’t know something it’s not a shame to ask for help .. and that’s what I did !
I contacted “Craig” from devttys0.com, he is an expect when it comes to hacking embdded devices . He’s a great guy and he replied to my email and pointed me to http://50.57.229.26/zynos.phpwhich is a free rom-0 file decompressor .

When you upload and submit the rom-0 file there, the php page replies back with the configuration in clear text ( INCLUDING THE PASSWORD ) .
So what i need to do now is to automate the process of :
Download rom-0 file.
Upload it to http://50.57.229.26/zynos.php
get the repy back and extract the admin password from it.
loop this process to a range of ip addresses.
And that’s exactly what I did, I opened an OLD OLD poc python script of mine that accessed routers via telnet using the default passwords. So what I just need to do now is to add some functionality to it.
Well I thought about this, and I’m posting this script online ONLY FOR EDUCATIONAL PURPOSES.
You can find the scripts here : https://github.com/MrNasro/zynos-attacker/
Demo :

PS : I OWN ALL THE IP RANGE I WAS SCANNING ” FOR SURE

“
Prevention :
Now ! how do you prevent attackers from downloading your rom-0 configuration file and manipulating your router ? This is pretty simple if you think about it ..You just have to forward port 80 on the router to and inused IP address on your network :

THATS ALL, or if you want to play a little with attackers that are using scripts too .. just forward port 80 to you local http server and put a LARGE file in the root directory and name it rom-0 .. just let them download like 1GB rom-0 file haha haha .. I have also automated the process of port forwarding and I’m running the scripts daily just to prevent hackers from attacking weak users …
In the next post I’ll demonstrate how would a malicious hacker exploit this to hack TONS of networks and get a meterpreter/reverse_shell on every PC on the target network ..
Hope you enjoyed this analysis, if you have anything to add or any questions to ask don’t hesitate to contact me ! BE THEIR HERO, HAPPY HACKING

相关文章推荐
- TP-LINK路由器设置内网的一台电脑在外网可以远程操控
- TP-LINK telnet远程 重启路由器
- [置顶] 路由器密码和上网账号密码都忘记了怎么办,可以通过模拟PPPoE协议从路由器获取
- XP无线网络链接不上TP_LINK的路由器,WIN7却可以连上。(同一个计算机和路由器)
- TPLink路由器登陆密码怎么破解
- 获取tp-link中的拨号密码
- TP-LINK telnet远程 重启路由器(转)
- TP-LINK多款路由器被曝存漏洞 或泄露网银密码
- 查看路由器内宽带账号密码(D-link,TP-Link)
- fast路由器初始密码 TP-Link、D-Link、ipTIME、Tenda/、Fast水星等路由器恢复出厂设置
- Telnet远程重启路由器TP-LINK
- 花生壳 远程管理 + 路由器设置(Tp-link)
- TP-LINK 路由器WAN端口状态一直无法获取IP地址 "dns server isn't responding"
- fast路由器初始密码 TP-Link、D-Link、ipTIME、Tenda/、Fast水星等路由器恢复出厂设置
- 【tp-link路由器默认用户名与密码 】
- 进入TP-Link路由器之后利用快捷键F12查看星号路由密码的方法
- 自动登录TP-LINK路由器,获取所有信息,重启等等,实用方法 推荐
- 通过TP-Link路由器WAN口嗅探PPPoE拨号密码-路由器拨号密码破解方法
- 进入TP-Link路由器之后利用快捷键F12查看星号路由密码的方法
- hg211g破解获取管理员密码,可以连接路由器。默认光猫来拨号。
