Crypto-RSA-1
2018-12-02 17:21
351 查看
i春秋第二届春秋欢乐赛RSA256 WP
题目链接:RSA256
0x00 查看题目内容
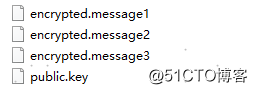
下载文件并解压,发现压缩包里有三段密文以及一个公钥
0x01 使用openssl查看公钥
看到public.key以后用kali linux里的openssl查看
查看一下openssl 中rsa的相关命令
root@kali:~/Desktop# openssl rsa -help Usage: rsa [options] Valid options are: -help Display this summary -inform format Input format, one of DER NET PEM -outform format Output format, one of DER NET PEM PVK -in val Input file -out outfile Output file -pubin Expect a public key in input file -pubout Output a public key -passout val Output file pass phrase source -passin val Input file pass phrase source -RSAPublicKey_in Input is an RSAPublicKey -RSAPublicKey_out Output is an RSAPublicKey -noout Don't print key out -text Print the key in text -modulus Print the RSA key modulus -check Verify key consistency -* Any supported cipher -pvk-strong Enable 'Strong' PVK encoding level (default) -pvk-weak Enable 'Weak' PVK encoding level -pvk-none Don't enforce PVK encoding -engine val Use engine, possibly a hardware device
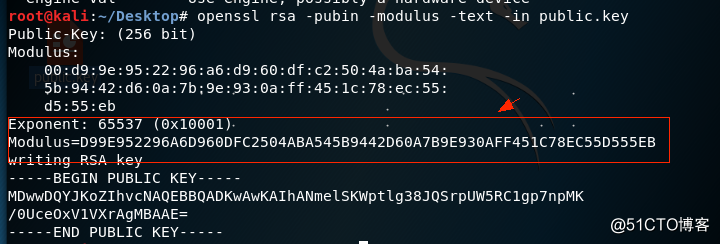
0x02 把N转成十进制
因为N是十六进制数 所以得把N转换成十进制才能用在线分解网站将其分解
root@kali:~/Desktop# python Python 2.7.15 (default, Jul 28 2018, 11:29:29) [GCC 8.1.0] on linux2 Type "help", "copyright", "credits" or "license" for more information. >>> Modulus=0xD99E952296A6D960DFC2504ABA545B9442D60A7B9E930AFF451C78EC55D555EB >>> Modulus 98432079271513130981267919056149161631892822707167177858831841699521774310891L
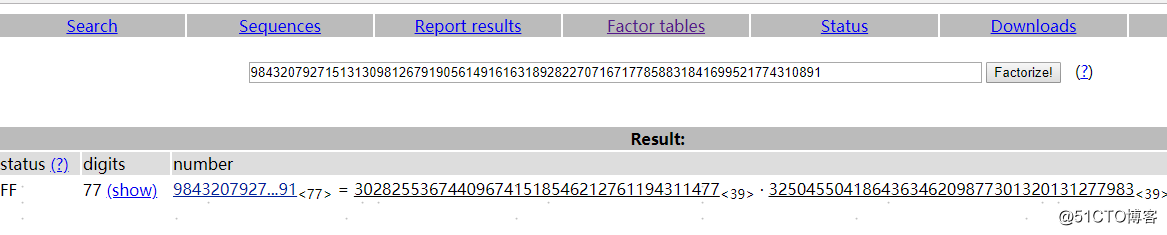
0x03因式分解
将n进行因式分解来得到我们的p和q (推荐使用http://factordb.com/)
0x04 生成私钥解密
import gmpy2
import rsa
p = 302825536744096741518546212761194311477
q = 325045504186436346209877301320131277983
n =9843207927151313098126791905614916163189282270716717785883184169952177431089
e = 65537
d = int(gmpy2.invert(e , (p-1) * (q-1)))
privatekey = rsa.PrivateKey(n , e , d , p , q)
with open("encrypted.message1" , "rb") as f:
print(rsa.decrypt(f.read(), privatekey).decode())
with open("encrypted.message2" , "rb") as f:
print(rsa.decrypt(f.read(), privatekey).decode())
with open("encrypted.message3" , "rb") as f:
print(rsa.decrypt(f.read(), privatekey).decode())
相关文章推荐
- C++利用Crypto++,vs2005环境下的RSA应用
- 基于Crypto++/Cryptopp的rsa密钥生成,rsa加密、解密,rsa签名、验签
- RSA解密时javax.crypto.BadPaddingException: Data must start with zero
- 《ASCE1885的信息安全》のCrypto++用户手册のrsa.h
- 关于使用Crypto++进行RSA加密
- 基于Crypto++/Cryptopp的rsa密钥生成,rsa加密、解密,rsa签名、验签
- 增加单测 java.lang.ClassCastException: com.sun.crypto.provider.RSACiphe
- 《ASCE1885的信息安全》のCrypto++用户手册のrsa.h
- 基于Crypto++/Cryptopp的rsa密钥生成,rsa加密、解密,rsa签名、验签12
- RSA (cryptosystem)
- SM2第二十一篇:OpenSSL中关于RSA_new和RSA_free的内存泄漏(CRYPTO_cleanup_all_ex_data)
- 基于Crypto++/Cryptopp的rsa密钥生成,rsa加密、解密,rsa签名、验签
- Crypto++入门学习笔记(DES、AES、RSA、SHA-256)
- 利用openssl crypto进行RSA非对称加密签名
- 关于解决RSA非对称加密时,将密文存入数据库取出后,再对密文解密的时候抛出javax.crypto.BadPaddingException: Data must start with zero
- 使用Crypto++5.5.2完成RSA加解密,真正的把公钥放在字符串内,而不是放在文件内
- 密码学原理_Crypto++实现RSA加密
- Poco::Crypto--加解密(RSA)
- Vc6.0下配置 Crypto++ ------用Crypto Library 实现简单的RSA加密
- Python开发【模块】:M2Crypto RSA加密、解密
