防xss攻击,需要对请求参数进行escape吗?
2016-04-08 23:28
183 查看
防xss攻击,需要对请求参数进行escape吗?
先看一个测试:请求:
http://localhost:8080/testapi/testapi?apiPath=http%3A%2F%2Fhbjltv.com%2Finfo%2Frequest%3Fusername%3Dhuang%26password%3Dadmin
解码之后就是:
http://localhost:8080/testapi/testapi?apiPath=http://hbjltv.com/info/request?username=huang&password=admin
该接口用于测试协作方接口的应答状态码.
为了防止xss攻击,所以对所有参数都进行html escape:
@RequestMapping("/testapi")
@ResponseBody
public String test(String apiPath, String requestMethod) throws IOException {
apiPath = HtmlUtils.htmlEscape(apiPath);
URL url = new URL(apiPath);
URLConnection urlConnection = url.openConnection();
HttpURLConnection httpUrlConnection = (HttpURLConnection) urlConnection;
httpUrlConnection.setDoInput(true);
httpUrlConnection.setUseCaches(false);
if (!ValueWidget.isNullOrEmpty(requestMethod)) {
httpUrlConnection.setRequestMethod(requestMethod);
}
httpUrlConnection.connect();
int responseStatusCode = httpUrlConnection.getResponseCode();
httpUrlConnection.disconnect();
System.out.println("responseStatusCode:" + responseStatusCode);
Map<String, Object> map = new HashMap<String, Object>();
map.put("responseCode", responseStatusCode);
map.put("apiPath", apiPath);
return HWJacksonUtils.getJsonP(map);
}看看协作方接口收到的参数:
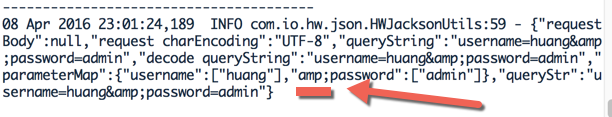
我传递的参数名称明明是password,但是现在怎么变成了amp;password ?
因为:
apiPath = HtmlUtils.htmlEscape(apiPath);
所以对参数进行HTML escape时应该不处理&
修改HTML escape 的函数如下:
相关文章推荐
- 正则表达式的组成规则
- 【LeetCode】69. Sqrt(x)解法及注释
- MySQL系列(1)--面试常用的
- iOS之UIColloctionView
- POJ 2914 Minimum Cut 全局最小割
- android的一道面试题
- 解决问题的细微方法
- javascript中replace与正则表达式
- 搭建公司内部的NuGet Server
- 在阿里云中编译Linux4.5.0内核 - Ubuntu内核编译教程
- 刚刚注册的博客
- forward和redirect 的区别
- hdu 1078 FatMouse and Cheese(dfs)
- arpack编译64位版本的记录
- JAVA 对象引用,以及对象赋值(转载)
- 互联网产品各阶段的标准流程文档
- Java笔记
- 2010上交:计算表达式
- Python3爬虫之爬取某一路径的所有html文件
- web框架--flask
