IDF 逆向题 python ByteCode
2015-06-12 10:54
627 查看
网站地址:http://ctf.idf.cn/index.php?g=game&m=article&a=index&id=45
进入后会获得一个.pyc文件,扔到http://tool.lu/pyc这个网站,获得程序的源码:
发现一个坑爹的算法:
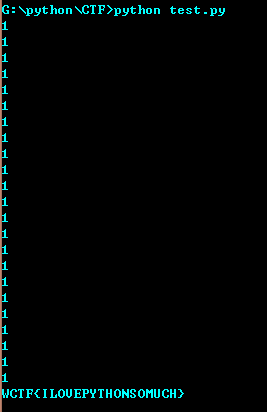
对余数求逆对我等小白来说,有点麻烦,索性代码不多,字节暴力猜解一下,代码如下:
结果为:WCTF{ILOVEPYTHONSOMUCH}
进入后会获得一个.pyc文件,扔到http://tool.lu/pyc这个网站,获得程序的源码:
#coding=utf-8
#!/usr/bin/env python
# encoding: utf-8
# 如果觉得不错,可以推荐给你的朋友!http://tool.lu/pyc
def encrypt(key, seed, string):
rst = []
for v in string:
rst.append((ord(v) + seed ^ ord(key[seed])) % 255)
seed = (seed + 1) % len(key)
return rst
if __name__ == '__main__':
print "Welcome to idf's python crackme"
flag = input('Enter the Flag: ')
KEY1 = 'Maybe you are good at decryptint Byte Code, have a try!'
KEY2 = [
124,
48,
52,
59,
164,
50,
37,
62,
67,
52,
48,
6,
1,
122,
3,
22,
72,
1,
1,
14,
46,
27,
232]
en_out = encrypt(KEY1, 5, flag)
if KEY2 == en_out:
print 'You Win'
else:
print 'Try Again !'发现一个坑爹的算法:
seed = (seed + 1) % len(key)
对余数求逆对我等小白来说,有点麻烦,索性代码不多,字节暴力猜解一下,代码如下:
#coding=utf-8
def encrypt(key, seed, v):
return (ord(v) + seed ^ ord(key[seed])) % 255
if __name__=='__main__':
s=['_','{','}'];
flag1='a';
flag2='A';
for i in range(26):
k=ord(flag1)+i;
k1=ord(flag2)+i
s.append(chr(k));
s.append(chr(k1));
KEY2 = [
124,
48,
52,
59,
164,
50,
37,
62,
67,
52,
48,
6,
1,
122,
3,
22,
72,
1,
1,
14,
46,
27,
232]
answer=[]
seed=5;
key= 'Maybe you are good at decryptint Byte Code, have a try!'
for i in range(23):
t=0;
for j in s:
if encrypt(key,seed,j)==KEY2[i]:
t=1; #判断是否匹配到了,若没有加大字符库即可啦
answer.append(j);
print t;
seed = (seed + 1) % len(key)
print ''.join(answer);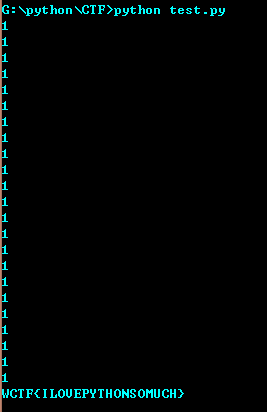
结果为:WCTF{ILOVEPYTHONSOMUCH}
相关文章推荐
- Python动态类型的学习---引用的理解
- Python3写爬虫(四)多线程实现数据爬取
- 垃圾邮件过滤器 python简单实现
- 下载并遍历 names.txt 文件,输出长度最长的回文人名。
- install and upgrade scrapy
- Scrapy的架构介绍
- Centos6 编译安装Python
- 使用Python生成Excel格式的图片
- 让Python文件也可以当bat文件运行
- [Python]推算数独
- Python中zip()函数用法举例
- Python中map()函数浅析
- Python在CAM软件Genesis2000中的应用
- 使用Shiboken为C++和Qt库创建Python绑定
- FREEBASIC 编译可被python调用的dll函数示例
- Python 七步捉虫法
- Python实现的基于ADB的Android远程工具
