poj2635--The Embarrassed Cryptographer(数论篇1,大数取模)
2015-01-22 17:07
579 查看
The Embarrassed Cryptographer
Description
The young and very promising cryptographer Odd Even has implemented the security module of a large system with thousands of users, which is now in use in his company.
The cryptographic keys are created from the product of two primes, and are believed to be secure because there is no known method for factoring such a product effectively.
What Odd Even did not think of, was that both factors in a key should be large, not just their product. It is now possible that some of the users of the system have weak keys. In a desperate attempt not to be fired, Odd Even secretly goes through all the users
keys, to check if they are strong enough. He uses his very poweful Atari, and is especially careful when checking his boss' key.
Input
The input consists of no more than 20 test cases. Each test case is a line with the integers 4 <= K <= 10100 and 2 <= L <= 106. K is the key itself, a product of two primes. L is the wanted minimum size of
the factors in the key. The input set is terminated by a case where K = 0 and L = 0.
Output
For each number K, if one of its factors are strictly less than the required L, your program should output "BAD p", where p is the smallest factor in K. Otherwise, it should output "GOOD". Cases should be separated by a line-break.
Sample Input
Sample Output
Source
Nordic 2005
题目要求:给出两个数k和l,k是由两个素数相乘得到,如果素数小于l,输出BAD 和那个素数,否则输出GOOD。
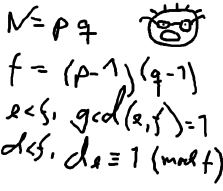
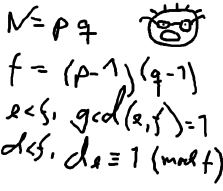
先打出素数表,其中一定要有大于100万的素数,把在l内的素数与k去模,其中k是10^100用到大数取余,将k分为三位数的段a[0] a[1],在计算
temp = a[0]%phi[i]
temp = (a[1]*1000+temp)%phi[i]
| Time Limit: 2000MS | Memory Limit: 65536K | |
| Total Submissions: 12496 | Accepted: 3330 |
The young and very promising cryptographer Odd Even has implemented the security module of a large system with thousands of users, which is now in use in his company.
The cryptographic keys are created from the product of two primes, and are believed to be secure because there is no known method for factoring such a product effectively.
What Odd Even did not think of, was that both factors in a key should be large, not just their product. It is now possible that some of the users of the system have weak keys. In a desperate attempt not to be fired, Odd Even secretly goes through all the users
keys, to check if they are strong enough. He uses his very poweful Atari, and is especially careful when checking his boss' key.
Input
The input consists of no more than 20 test cases. Each test case is a line with the integers 4 <= K <= 10100 and 2 <= L <= 106. K is the key itself, a product of two primes. L is the wanted minimum size of
the factors in the key. The input set is terminated by a case where K = 0 and L = 0.
Output
For each number K, if one of its factors are strictly less than the required L, your program should output "BAD p", where p is the smallest factor in K. Otherwise, it should output "GOOD". Cases should be separated by a line-break.
Sample Input
143 10 143 20 667 20 667 30 2573 30 2573 40 0 0
Sample Output
GOOD BAD 11 GOOD BAD 23 GOOD BAD 31
Source
Nordic 2005
题目要求:给出两个数k和l,k是由两个素数相乘得到,如果素数小于l,输出BAD 和那个素数,否则输出GOOD。
先打出素数表,其中一定要有大于100万的素数,把在l内的素数与k去模,其中k是10^100用到大数取余,将k分为三位数的段a[0] a[1],在计算
temp = a[0]%phi[i]
temp = (a[1]*1000+temp)%phi[i]
#include <cstdio>
#include <cstring>
#include <algorithm>
using namespace std ;
#define LL __int64
char str[200] ;
int n , a[100] , num ;
int vis[2100000] , phi[1100000] , cnt ;
void init()
{
int i , j ;
cnt = 0 ;
memset(vis,0,sizeof(vis)) ;
for(i = 2 ; i <= 2000000 ; i++)
{
if( !vis[i] ) phi[cnt++] = i ;
for(j = 0 ; j < cnt ; j++)
{
if( i*phi[j] >= 2000000 )
break ;
vis[i*phi[j]] = 1 ;
if( i%phi[j] == 0 )
break ;
}
}
}
int f(int k)
{
LL sum = 0 , i , l ;
for(i = num-1 ; i >= 0 ; i--)
{
sum = sum*1000 + a[i] ;
sum %= k ;
}
if( sum == 0 )
return 1 ;
return 0;
}
int main()
{
int i , j , l , flag , s ;
init() ;
while( scanf("%s %d", str, &n) != EOF )
{
if( strlen(str) == 1 && str[0] == '0' && n == 0 ) break ;
l = strlen(str) ;
memset(a,0,sizeof(a)) ;
num = 0 ;
flag = 0 ;
for(i = l-1 ; i >= 0 ; i--)
{
flag++ ;
if( flag == 3 )
{
a[num] = (str[i]-'0')*100 + (str[i+1]-'0')*10 + ( str[i+2] -'0' ) ;
num++ ;
flag = 0 ;
}
}
if( flag == 1 )
a[num++] = str[0] - '0' ;
else if( flag == 2 )
a[num++] = (str[0] - '0') * 10 + str[1] - '0' ;
for(i = 0 ; i < cnt ; i++)
{
if( phi[i] >= n ) break ;
if( f(phi[i]) )
break ;
}
if( phi[i] >= n || i == cnt )
printf("GOOD\n") ;
else
printf("BAD %d\n", phi[i]);
}
return 0;
}
相关文章推荐
- poj 2635 The Embarrassed Cryptographer(数论)
- POJ 2635 The Embarrassed Cryptographer【数论,千进制,高精度求模+同余模定理】
- POJ 2635 The Embarrassed Cryptographer 高精度取模 + 线性筛
- POJ 2635 The Embarrassed Cryptographer [高精度求余+同余模定理]【数论】
- POJ2635 The Embarrassed Cryptographer 简单数论
- 【数论】POJ_2635_The Embarrassed Cryptographer
- (大数取模)POJ2635-The Embarrassed Cryptographer
- poj2635——The Embarrassed Cryptographer(高精度取模)
- POJ The Embarrassed Cryptographer 2635 (数论)
- poj 2635 The Embarrassed Cryptographer ——高精度取模
- POJ -2635-The Embarrassed Cryptographer-数论
- POJ 2635 The Embarrassed Cryptographer 线性筛+高精度取模
- The Embarrassed Cryptographer POJ 2635 数论之高精度求模(同余模定理+千进制)
- POJ 2635 The Embarrassed Cryptographer
- POJ 2635 The Embarrassed Cryptographer(JAVA)
- poj-2635-The Embarrassed Cryptographer
- poj2635 The Embarrassed Cryptographer
- POJ-2635 The Embarrassed Cryptographer 大数取模
- POJ 2635 The Embarrassed Cryptographer
- poj 2635 The Embarrassed Cryptographer
