VC++进程注入
2014-10-19 11:06
155 查看
【2014/10/19 11:12】
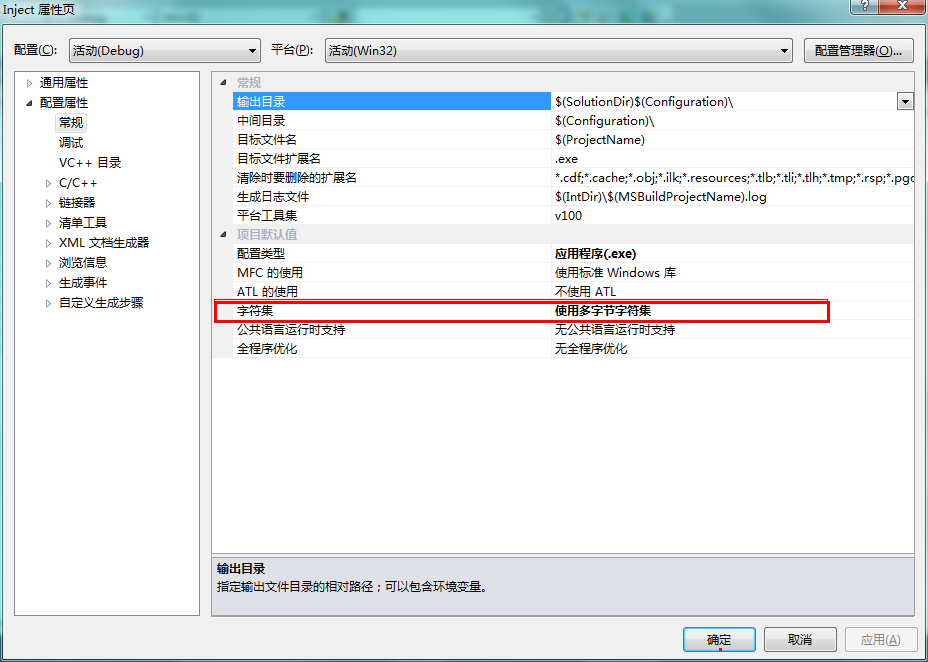
项目编码:
头文件:
// stdafx.h : 标准系统包含文件的包含文件, // 或是经常使用但不常更改的 // 特定于项目的包含文件 // #pragma once #include "targetver.h" #include <stdio.h> #include <tchar.h> //myself #include <Windows.h> #include <TlHelp32.h> #include <iostream> using namespace std; // TODO: 在此处引用程序需要的其他头文件
程序代码:
// Inject.cpp : 定义控制台应用程序的入口点。
//
#include "stdafx.h"
/*
* 提升进程的权限
*/
int EnableDebugePriv(const char * name){
HANDLE hToken;
/*
* 访问令牌特权结构体
* PrivilegeCount: the number of entries in the Privileges array
* Privileges[ANYSIZE_ARRAY]:
* LUID :特权属性的名字
* SE_PRIVILEGE_ENABLED :启用了特权
*/
TOKEN_PRIVILEGES tp;
/*
* locally unique identifier (LUID) is guaranteed only until the system is restarted.
* call the LookupPrivilegeName function, passing the address of the LUID as the value of the lpLuid parameter.
*/
LUID luid;
/*
* The OpenProcessToken function opens the access token associated with a process.(打开进程令牌环)
* ProcessHandle [in]: A handle to the process whose access token is opened.
* DesiredAccess [in]:Required to enable or disable the privileges in an access token.
* TokenHandle [out] :A pointer to a handle that identifies the newly opened access token when the function returns.
*/
OpenProcessToken(GetCurrentProcess(),TOKEN_ADJUST_PRIVILEGES | TOKEN_QUERY,&hToken);
/*
* [lpSystemName]- [in, optional] :If a null string is specified, the function attempts to find the privilege name on the local system.
* [lpName]-[in] : 可以指定为一个常量
* [lpLuid]-[out] : 返回一个指定的LUID
*/
LookupPrivilegeValue(NULL,name,&luid);
tp.PrivilegeCount=1;
tp.Privileges[0].Luid=luid;
tp.Privileges[0].Attributes=SE_PRIVILEGE_ENABLED;
/*
* Enabling or disabling privileges in an access token requires TOKEN_ADJUST_PRIVILEGES access.
* TokenHandle [in]: The handle must have TOKEN_ADJUST_PRIVILEGES access to the token. If the PreviousState parameter is not NULL,
* the handle must also have TOKEN_QUERY access.
* DisableAllPrivileges [in]: Specifies whether the function disables all of the token's privileges.If it is FALSE, the function
* modifies privileges based on the information pointed to by the NewState parameter.
* NewState [in, optional]: the DisableAllPrivileges parameter is FALSE, the AdjustTokenPrivileges function enables,
* disables, or removes these privileges for the token.
* BufferLength [in]: Specifies the size, in bytes, of the buffer pointed to by the PreviousState parameter.
* PreviousState [out, optional]: If the PrivilegeCount member of TOKEN_PRIVILEGES is zero,
* then no privileges have been changed by this function. This parameter can be NULL.
* ReturnLength [out, optional]: pointer to a variable that receives the required size, in bytes, of the buffer pointed to
* by the PreviousState parameter. This parameter can be NULL if PreviousState is NULL.
*
*/
AdjustTokenPrivileges(hToken,0,&tp,sizeof(TOKEN_PRIVILEGES),NULL,NULL);
return 0;
}
BOOL InjectDLL(const char * DllFullPath, const DWORD dwRemoteProcessId){
HANDLE hRemoteProcess;
/*
*
*/
EnableDebugePriv(SE_DEBUG_NAME);
//打开远程线程
/*
* Opens an existing local process object.
* dwDesiredAccess [in] : 对进程的访问类型
* bInheritHandle [in] :
* dwProcessId [in] : The identifier of the local process to be opened.
*/
hRemoteProcess=OpenProcess(PROCESS_ALL_ACCESS,FALSE,dwRemoteProcessId);
char * pszLibFileRemote;
//使用VirtualAllocEx函数在远程进程的内存地址空间分配DLL文件名空间
/*
* Reserves or commits a region of memory within the virtual address space of a specified process.
* The function initializes the memory it allocates to zero
* hProcess [in] : The handle to a process. The function allocates memory within the virtual address space of this process.
* lpAddress [in, optional] : If lpAddress is NULL, the function determines where to allocate the region.
* dwSize [in] : The size of the region of memory to allocate, in bytes.
* flAllocationType [in] : The type of memory allocation.
* flProtect [in] :The memory protection for the region of pages to be allocated.
*/
pszLibFileRemote=(char *)VirtualAllocEx(hRemoteProcess,NULL,lstrlen(DllFullPath)+1,MEM_COMMIT,PAGE_READWRITE);
//使用WriteProcessMemory函数将DLL的路径名写入到远程进程的内存空间
/*
* Writes data to an area of memory in a specified process.
* hProcess [in]: A handle to the process memory to be modified.
* lpBaseAddress [in] :A pointer to the base address in the specified process to which data is written.
* lpBuffer [in] :A pointer to the buffer that contains data to be written in the address space of the specified process.
* nSize [in] :The number of bytes to be written to the specified process.
* lpNumberOfBytesWritten [out] : If lpNumberOfBytesWritten is NULL, the parameter is ignored.
*
*/
WriteProcessMemory(hRemoteProcess,pszLibFileRemote,(void *)DllFullPath,lstrlen(DllFullPath)+1,NULL);
//在宿主中启用新的线程使用LoadLibraryA()函数加载的
//计算LoadLibraryA的入口地址
/*
* Retrieves(检索) the address of an exported function or variable from the specified dynamic-link library (DLL).
* hModule [in] : A handle to the DLL module that contains the function or variable.
* The LoadLibrary, LoadLibraryEx, LoadPackagedLibrary, or GetModuleHandle function returns this handle.
* lpProcName [in] : The function or variable name, or the function's ordinal value. If this parameter is an ordinal value,
* it must be in the low-order word; the high-order word must be zero.
*/
//计算LoadLibraryA的入口地址
PTHREAD_START_ROUTINE pfnStartAddr=(PTHREAD_START_ROUTINE)GetProcAddress(GetModuleHandle(TEXT("Kernel32.dll")),"LoadLibraryA");
//启动远程线程LoadLibraryA,通过远程线程调用创建新的线程
HANDLE hRemoteThread;
/*
* Creates a thread that runs in the virtual address space of another process.
* hProcess [in] : A handle to the process in which the thread is to be created.
* lpThreadAttributes [in] : A pointer to a SECURITY_ATTRIBUTES structure that specifies a security descriptor
* for the new thread and determines whether child processes can inherit the returned handle.
* If lpThreadAttributes is NULL, the thread gets a default security descriptor and the handle
* cannot be inherited.
* dwStackSize [in] : The initial size of the stack, in bytes.If this parameter is 0 (zero),
* the new thread uses the default size for the executable.
* lpStartAddress [in] : A pointer to the application-defined function of type LPTHREAD_START_ROUTINE to be executed by the thread
* and represents the starting address of the thread in the remote process.
* lpParameter [in] : A pointer to a variable to be passed to the thread function.
* dwCreationFlags [in] : The flags that control the creation of the thread.
* lpThreadId [out] :
*/
if((hRemoteThread=CreateRemoteThread(hRemoteProcess,NULL,0,pfnStartAddr,pszLibFileRemote,0,NULL))==NULL){
cout<<"线程注入失败!"<<endl;
return FALSE;
}
//释放句柄
CloseHandle(hRemoteThread);
CloseHandle(hRemoteProcess);
return TRUE;
}
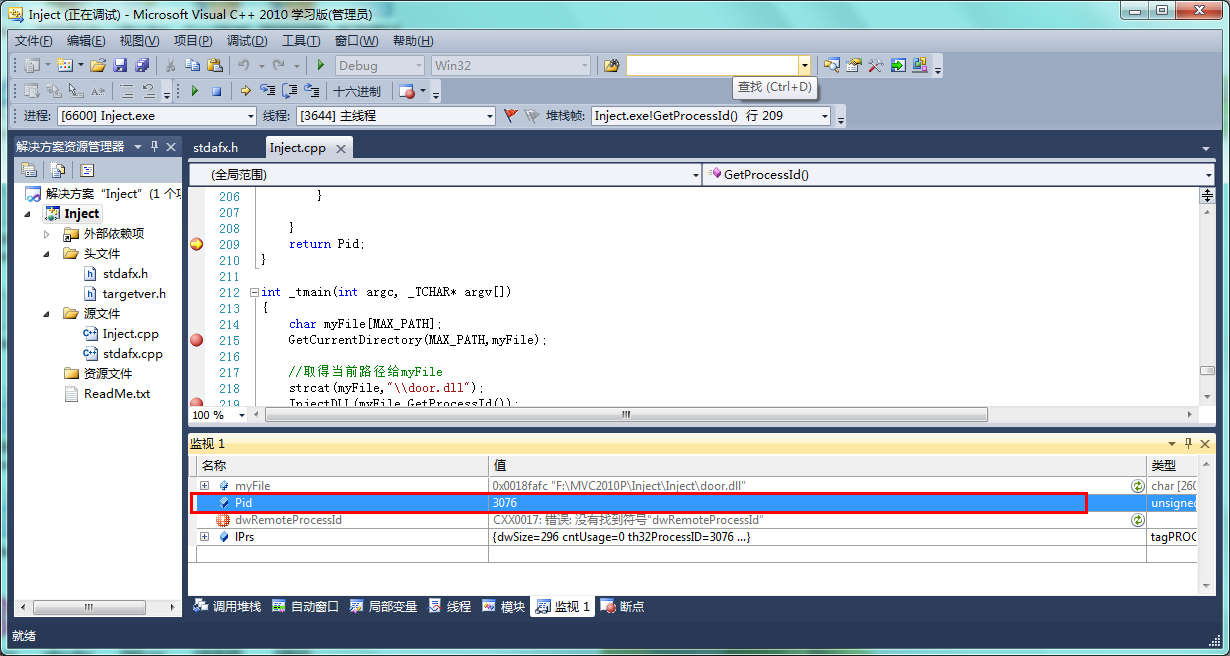
DWORD GetProcessId(){
DWORD Pid=-1;
/*
* Takes a snapshot of the specified processes
* dwFlags [in]: TH32CS_SNAPPROCESS-Includes all processes in the system in the snapshot.
* th32ProcessID [in]: The process identifier of the process to be included in the snapshot.
* This parameter can be zero to indicate the current process. This parameter is used when the TH32CS_SNAPHEAPLIST,
* TH32CS_SNAPMODULE, TH32CS_SNAPMODULE32, or TH32CS_SNAPALL value is specified.
* Otherwise, it is ignored and all processes are included in the snapshot.
*/
HANDLE hSnap=CreateToolhelp32Snapshot(TH32CS_SNAPPROCESS,0);
//创建系统快照
/*
* Describes an entry from a list of the processes residing in the system address space when a snapshot was taken.
* th32ProcessID: The process identifier.
* szExeFile : The name of the executable file for the process.
*/
PROCESSENTRY32 lPrs;
ZeroMemory(&lPrs,sizeof(PROCESSENTRY32));
lPrs.dwSize=sizeof(lPrs);
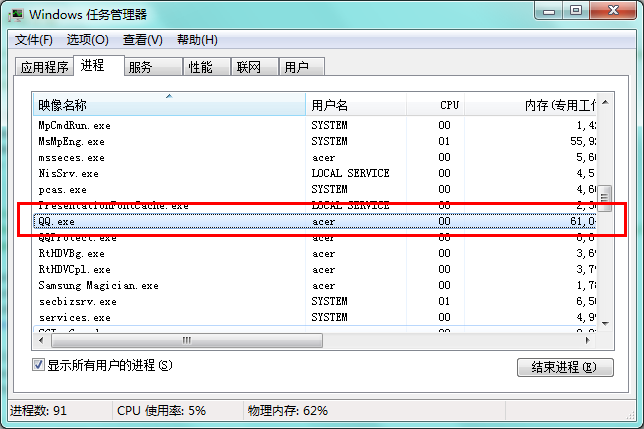
char * TargetFile="QQ.exe";
/*
* Retrieves information about the first process encountered in a system snapshot.
* hSnapshot [in] : A handle to the snapshot returned from a previous call to the CreateToolhelp32Snapshot function.
* lppe [in, out] : A pointer to a PROCESSENTRY32 structure.
*/
Process32First(hSnap,&lPrs);
if(strstr(TargetFile,lPrs.szExeFile)!=NULL){
Pid=lPrs.th32ProcessID;
return Pid;
}
while(1){
ZeroMemory(&lPrs,sizeof(PROCESSENTRY32));
lPrs.dwSize=sizeof(lPrs);
/*
* Returns TRUE if the next entry of the process list has been copied to the buffer or FALSE otherwise.
* The comparison is case-sensitive.
*/
if(!Process32Next(hSnap,&lPrs)){
Pid=-1;
break;
}
/*
* Returns the address of the first occurrence of the matching substring if successful, or NULL otherwise.
*/
if(strstr(TargetFile,lPrs.szExeFile)!=NULL){
Pid=lPrs.th32ProcessID;
break;
}
}
return Pid;
}
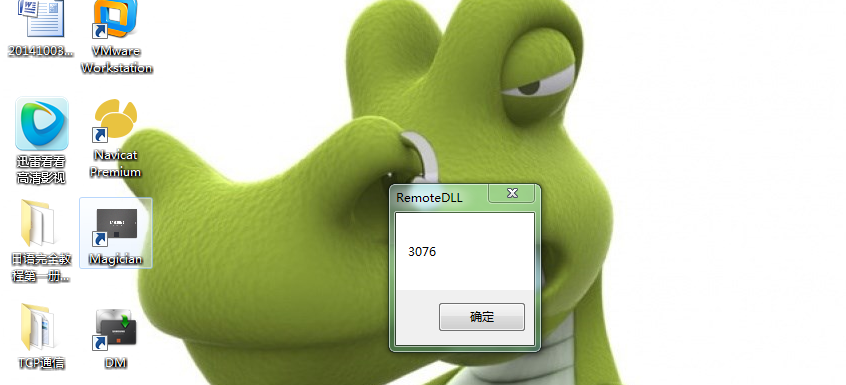
int _tmain(int argc, _TCHAR* argv[])
{
char myFile[MAX_PATH];
GetCurrentDirectory(MAX_PATH,myFile);
//取得当前路径给myFile
strcat(myFile,"\\door.dll");
InjectDLL(myFile,GetProcessId());
return 0;
}程序运行的过程:
ALL代码在资源中可以下载
相关文章推荐
- vc++ 向其他进程注入代码的三种方法
- vc++进程注入钩子DLL通用模块开源
- vc++进程注入钩子DLL通用模块开源
- VC下提前注入进程的一些方法1——远线程不带参数
- VC下提前注入进程的一些方法3——修改程序入口点
- VC下提前注入进程的一些方法1——远线程不带参数
- vc++ 向其他进程注入代码的三种方法
- VC下提前注入进程的一些方法2——远线程带参数
- VC下提前注入进程的一些方法2——远线程带参数
- VC下提前注入进程的一些方法3——修改程序入口点
- VC DLL远程进程注入
- 【VC++积累】之五、进程注入技术
- 【VC++积累】之五、进程注入技术
- vc++进程注入钩子DLL通用模块
- 在VC++应用程序中彻底清除进程
- VC 中进程与多进程管理的方法
- VC 共享内存实现进程间大数据的交换
- 反向进程注入及隐藏--动手做一个最简单的PELoader
- VC++ 实现dll远程注入代码示例
- 向其他进程注入代码的三种方法
