ingress-nginx 部署使用及原理简介
ingress:
可以简单理解为service的service,他通过独立的ingress对象来制定请求转发的规则,把请求路由到一个或多个service中。这样就把服务与请求规则解耦了,可以从业务维度统一考虑业务的暴露,而不用为每个service单独考虑。
举个例子,现在集群有api、文件存储、前端3个service,可以通过一个ingress对象来实现图中的请求转发。
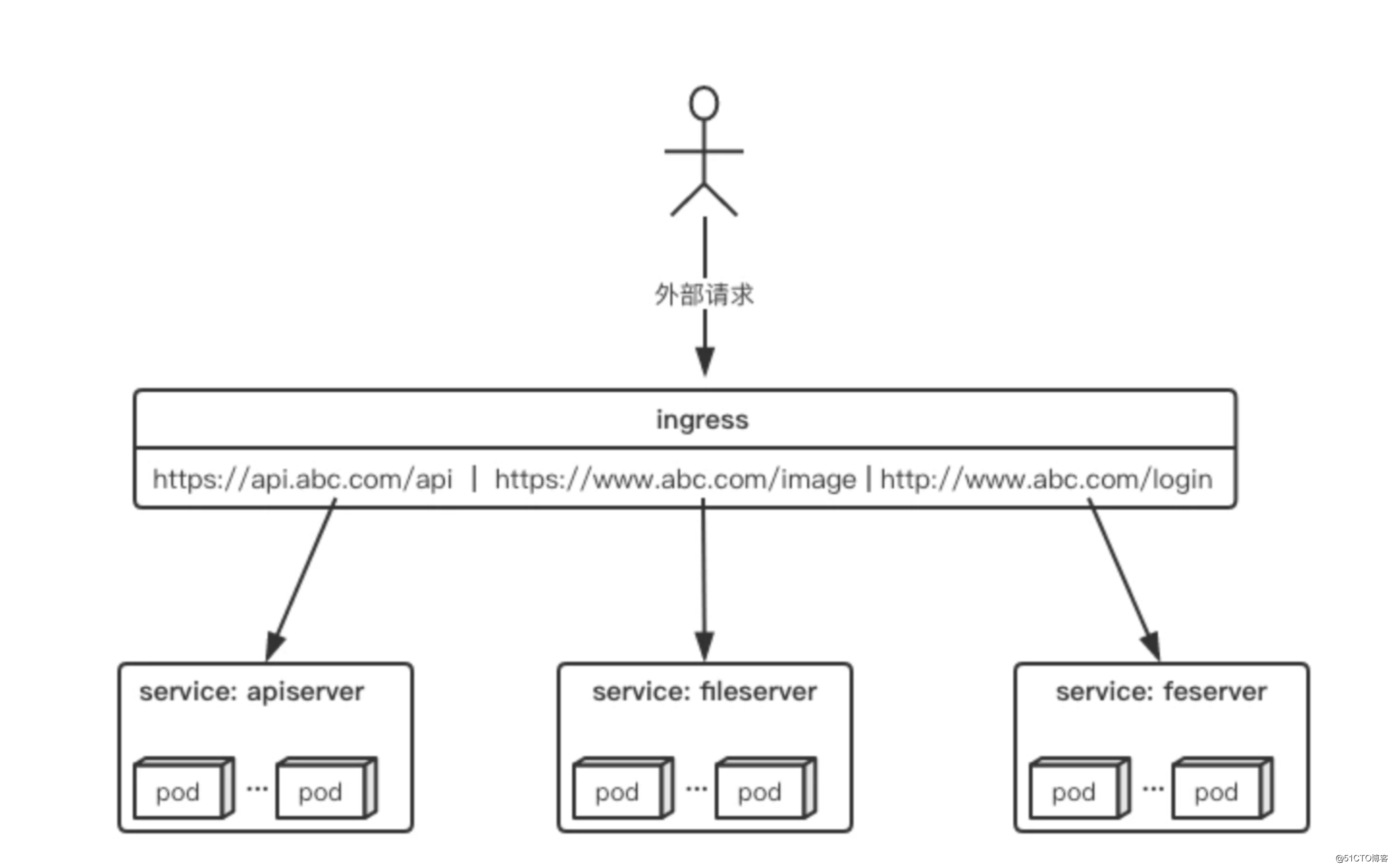
ingress规则是很灵活的,可以根据不同域名、不同path转发请求到不同的service,并且支持https/http。
ingress与ingress-controller
- ingress对象:指的是k8s中的一个api对象,一般用yaml配置。作用是定义请求如何转发到service的规则,可以理解为配置模板。
- ingress-controller:具体实现反向代理及负载均衡的程序,对ingress定义的规则进行解析,根据配置的规则来实现请求转发。
ingress-controller才是负责具体转发的组件,通过各种方式将它暴露在集群入口,外部对集群的请求流量会先到ingress-controller,而ingress对象是用来告诉ingress-controller该如何转发请求,比如哪些域名哪些path要转发到哪些服务等等
ingress-controller
ingress-controller并不是k8s自带的组件,实际上ingress-controller只是一个统称,用户可以选择不同的ingress-controller实现,目前,由k8s维护的ingress-controller只有google云的GCE与ingress-nginx两个,其他还有很多第三方维护的ingress-controller。一般来说,ingress-controller的形式都是一个pod,里面跑着daemon程序和反向代理程序。daemon负责不断监控集群的变化,根据ingress对象生成配置并应用新配置到反向代理,比如nginx-ingress就是动态生成nginx配置,动态更新upstream,并在需要的时候reload程序应用新配置。
ingress
ingress是一个API对象,和其他对象一样,通过yaml文件来配置。ingress通过http或https暴露集群内部service,给service提供外部URL、负载均衡、SSL/TLS能力以及基于host的方向代理。ingress要依靠ingress-controller来具体实现以上功能。
ngress-nginx解决了生产环境中哪些问题?
1)动态配置服务:
如果按照传统方式,当新增加一个服务时,我们可能需要在流量入口加一个反向代理指向我们新的服务,而使用ingress,只需要配置好ingress,当服务启动时,会自动注册到ingress当中,不需要额外的操作。
2)减少不必要的Port暴露(安全,端口容易管理)
我们知道部署k8s时,是需要关闭防火墙的,主要原因是k8s的很多服务会以nodeport方式映射出去,这样对于宿主机来说是非常的不安全的,而ingress可以避免这个问题,只需要将ingress自身服务映射出去,就可代理后端所有的服务,则后端服务不需要映射出去
部署ingress-nginx
1、配置ingress-nginx yaml部署文件
vim mandatory.yaml apiVersion: v1 kind: Namespace metadata: name: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx --- kind: ConfigMap apiVersion: v1 metadata: name: nginx-configuration namespace: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx --- kind: ConfigMap apiVersion: v1 metadata: name: tcp-services namespace: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx --- kind: ConfigMap apiVersion: v1 metadata: name: udp-services namespace: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx --- apiVersion: apps/v1 kind: Deployment metadata: name: default-http-backend labels: app: default-http-backend namespace: ingress-nginx spec: replicas: 1 selector: matchLabels: app: default-http-backend template: metadata: labels: app: default-http-backend spec: terminationGracePeriodSeconds: 60 containers: - name: default-http-backend image: registry.cn-qingdao.aliyuncs.com/kubernetes_xingej/defaultbackend-amd64:1.5 #建议提前在node节点下载镜像; livenessProbe: httpGet: path: /healthz port: 8080 scheme: HTTP initialDelaySeconds: 30 timeoutSeconds: 5 ports: - containerPort: 8080 resources: # 这里调整了cpu和memory的大小,可能不同集群限制的最小值不同,看部署失败的原因就清楚 limits: cpu: 100m memory: 100Mi requests: cpu: 100m memory: 100Mi --- apiVersion: v1 kind: Service metadata: name: default-http-backend # namespace: ingress-nginx namespace: ingress-nginx labels: app: default-http-backend spec: ports: - port: 80 targetPort: 8080 selector: app: default-http-backend --- apiVersion: v1 kind: ServiceAccount metadata: name: nginx-ingress-serviceaccount namespace: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx --- apiVersion: rbac.authorization.k8s.io/v1beta1 kind: ClusterRole metadata: name: nginx-ingress-clusterrole labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx rules: - apiGroups: - "" resources: - configmaps - endpoints - nodes - pods - secrets verbs: - list - watch - apiGroups: - "" resources: - nodes verbs: - get - apiGroups: - "" resources: - services verbs: - get - list - watch - apiGroups: - "" resources: - events verbs: - create - patch - apiGroups: - "extensions" - "networking.k8s.io" resources: - ingresses verbs: - get - list - watch - apiGroups: - "extensions" - "networking.k8s.io" resources: - ingresses/status verbs: - update --- apiVersion: rbac.authorization.k8s.io/v1beta1 kind: Role metadata: name: nginx-ingress-role namespace: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx rules: - apiGroups: - "" resources: - configmaps - pods - secrets - namespaces verbs: - get - apiGroups: - "" resources: - configmaps resourceNames: # Defaults to "<election-id>-<ingress-class>" # Here: "<ingress-controller-leader>-<nginx>" # This has to be adapted if you change either parameter # when launching the nginx-ingress-controller. - "ingress-controller-leader-nginx" verbs: - get - update - apiGroups: - "" resources: - configmaps verbs: - create - apiGroups: - "" resources: - endpoints verbs: - get --- apiVersion: rbac.authorization.k8s.io/v1beta1 kind: RoleBinding metadata: name: nginx-ingress-role-nisa-binding namespace: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx roleRef: apiGroup: rbac.authorization.k8s.io kind: Role name: nginx-ingress-role subjects: - kind: ServiceAccount name: nginx-ingress-serviceaccount namespace: ingress-nginx --- apiVersion: rbac.authorization.k8s.io/v1beta1 kind: ClusterRoleBinding metadata: name: nginx-ingress-clusterrole-nisa-binding labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx roleRef: apiGroup: rbac.authorization.k8s.io kind: ClusterRole name: nginx-ingress-clusterrole subjects: - kind: ServiceAccount name: nginx-ingress-serviceaccount namespace: ingress-nginx --- apiVersion: apps/v1 kind: Deployment metadata: name: nginx-ingress-controller namespace: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx spec: replicas: 2 selector: matchLabels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx template: metadata: labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx annotations: prometheus.io/port: "10254" prometheus.io/scrape: "true" spec: # wait up to five minutes for the drain of connections terminationGracePeriodSeconds: 300 serviceAccountName: nginx-ingress-serviceaccount nodeSelector: kubernetes.io/os: linux containers: - name: nginx-ingress-controller image: suisrc/ingress-nginx:0.30.0 #建议提前在node节点下载镜像; args: - /nginx-ingress-controller - --default-backend-service=$(POD_NAMESPACE)/default-http-backend - --configmap=$(POD_NAMESPACE)/nginx-configuration - --tcp-services-configmap=$(POD_NAMESPACE)/tcp-services - --udp-services-configmap=$(POD_NAMESPACE)/udp-services - --publish-service=$(POD_NAMESPACE)/ingress-nginx - --annotations-prefix=nginx.ingress.kubernetes.io securityContext: allowPrivilegeEscalation: true capabilities: drop: - ALL add: - NET_BIND_SERVICE # www-data -> 101 runAsUser: 101 env: - name: POD_NAME valueFrom: fieldRef: fieldPath: metadata.name - name: POD_NAMESPACE valueFrom: fieldRef: fieldPath: metadata.namespace ports: - name: http containerPort: 80 protocol: TCP - name: https containerPort: 443 protocol: TCP livenessProbe: failureThreshold: 3 httpGet: path: /healthz port: 10254 scheme: HTTP initialDelaySeconds: 10 periodSeconds: 10 successThreshold: 1 timeoutSeconds: 10 readinessProbe: failureThreshold: 3 httpGet: path: /healthz port: 10254 scheme: HTTP periodSeconds: 10 successThreshold: 1 timeoutSeconds: 10 lifecycle: preStop: exec: command: - /wait-shutdown --- apiVersion: v1 kind: LimitRange metadata: name: ingress-nginx namespace: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx spec: limits: - min: memory: 90Mi cpu: 100m type: Container --- apiVersion: v1 kind: Service metadata: name: ingress-nginx namespace: ingress-nginx labels: app.kubernetes.io/name: ingress-nginx app.kubernetes.io/part-of: ingress-nginx spec: type: NodePort ports: - name: http port: 80 targetPort: 80 protocol: TCP # HTTP nodePort: 32080 - name: https port: 443 targetPort: 443 protocol: TCP # HTTPS nodePort: 32443 selector: app.kubernetes.io/name: ingress-nginx 8000 app.kubernetes.io/part-of: ingress-nginx
2、运行Yaml文件
kubectl apply -f mandatory.yaml
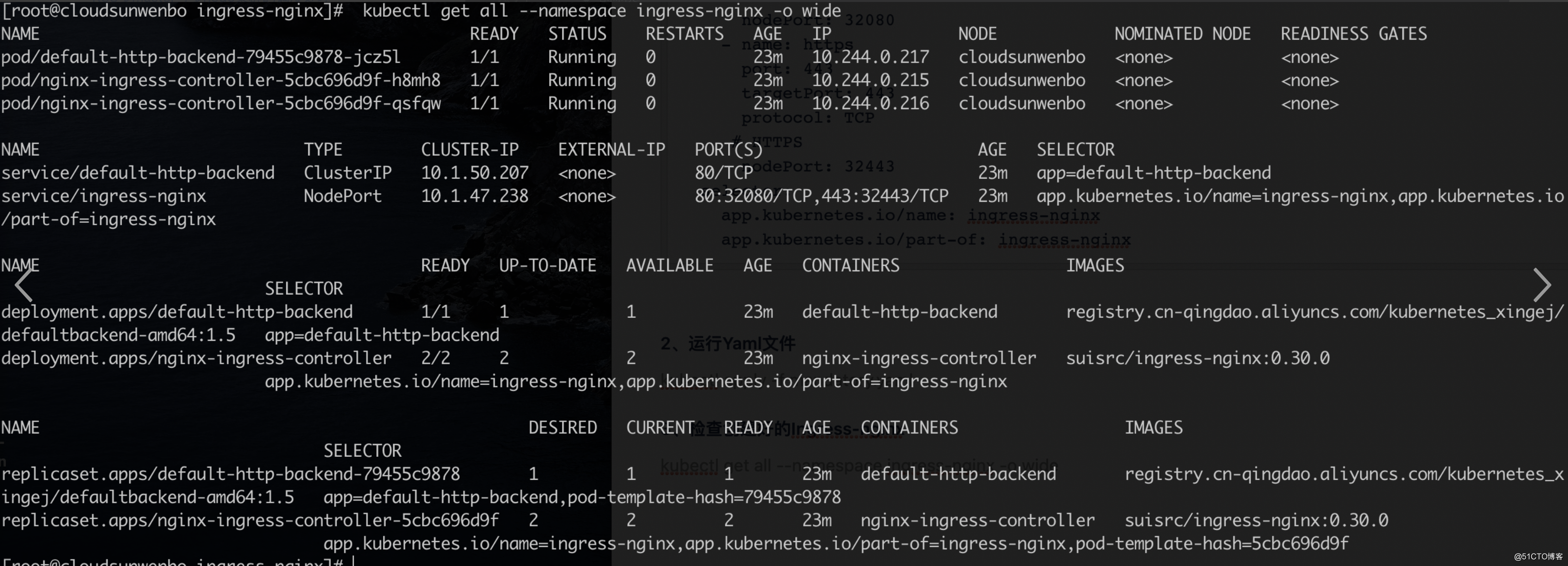
3、检查创建好的Ingress-nginx
kubectl get all --namespace ingress-nginx -o wide
4、 访问ingress-nginx服务,查看是否配置成功
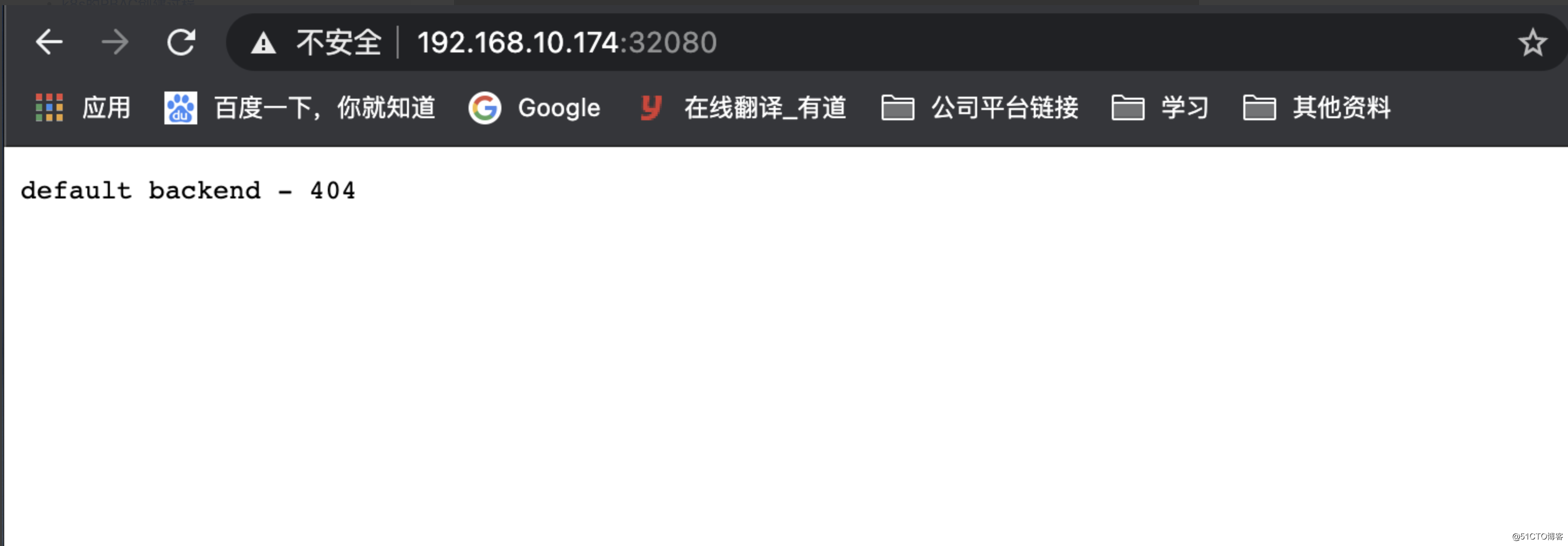
提示404,这个因为当前ingress-nginx服务现在还没有后端服务,这是正常的,到此Ingress控制器部署成功!!!
二、部署Tomcat后端服务来验证Ingress
1、创建tomcat部署文件
vim tomcat-deploy.yaml apiVersion: v1 kind: Service metadata: name: tomcat namespace: default #使用默认的名称空间即可 spec: selector: app: tomcat release: canary ports: - name: http port: 8080 targetPort: 8080 - name: ajp port: 8009 targetPort: 8009 --- apiVersion: apps/v1 kind: Deployment metadata: name: tomcat-deploy spec: replicas: 3 selector: matchLabels: app: tomcat release: canary template: metadata: labels: app: tomcat release: canary spec: containers: - name: tomcat image: tomcat:7-alpine ports: - name: httpd containerPort: 8080 - name: ajp containerPort: 8009 kubectl apply -f tomcat-deploy.yaml #运行Yaml文件 kubectl get pod |grep tomcat-deploy #检查pod是否部署成功
- 将tomcat添加至ingress-nginx中
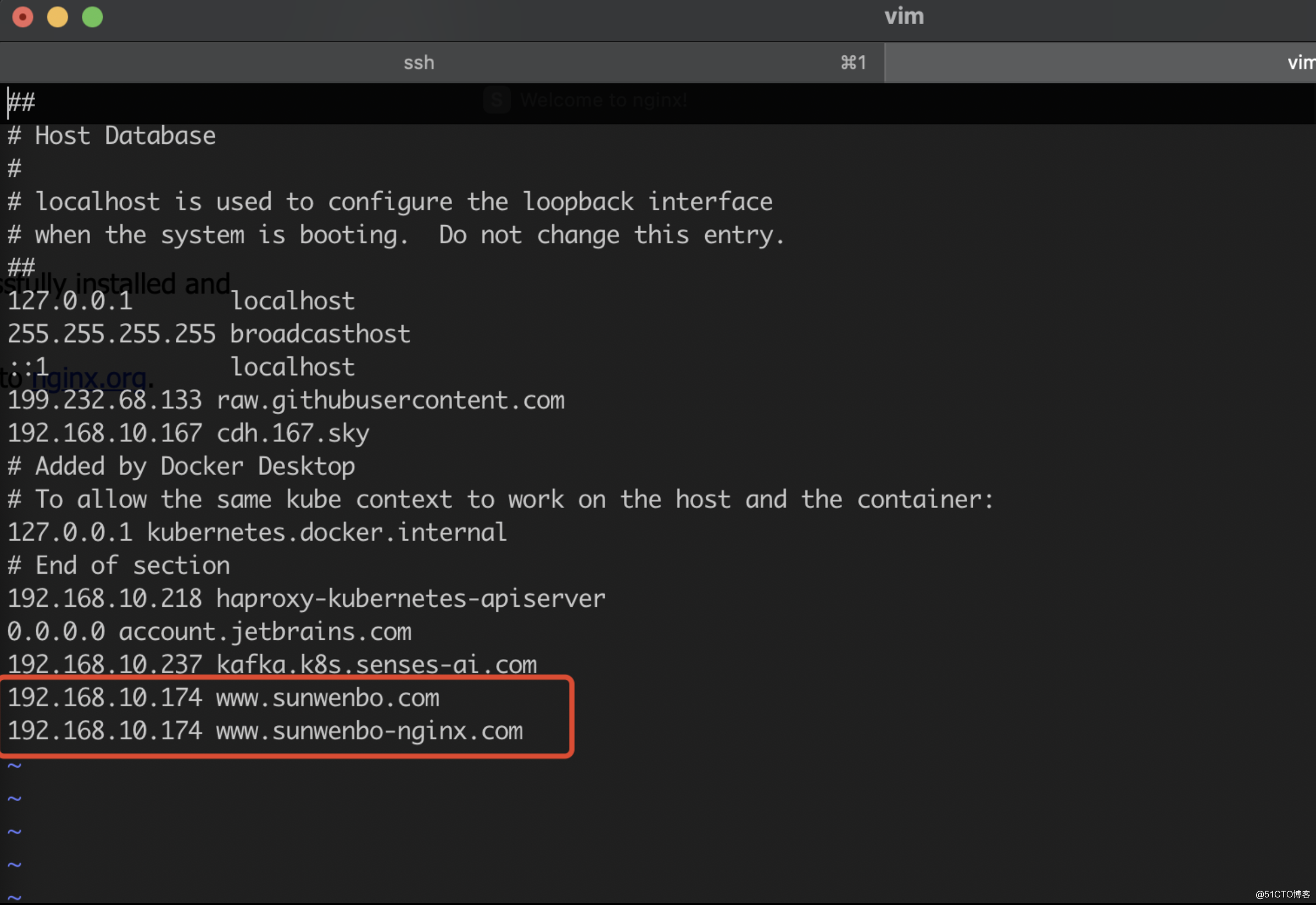
apiVersion: extensions/v1beta1 kind: Ingress metadata: name: ingress-tomcat namespace: default annotations: kubernets.io/ingress.class: "nginx" spec: rules: - host: www.sunwenbo.com #将域名与node IP 绑定写入访问节点hosts文件 http: paths: - path: backend: serviceName: tomcat #service名称 servicePort: 8080 #cluster 端口号 - host: www.sunwenbo-nginx.com http: paths: - path: backend: serviceName: nginx-deployment servicePort: 80 kubectl apply -f ingress-tomcat.yaml #运行Yaml文件 kubectl get ingress #检查生成的ingress信息
2.2、将域名解析写入访问节点hosts文件
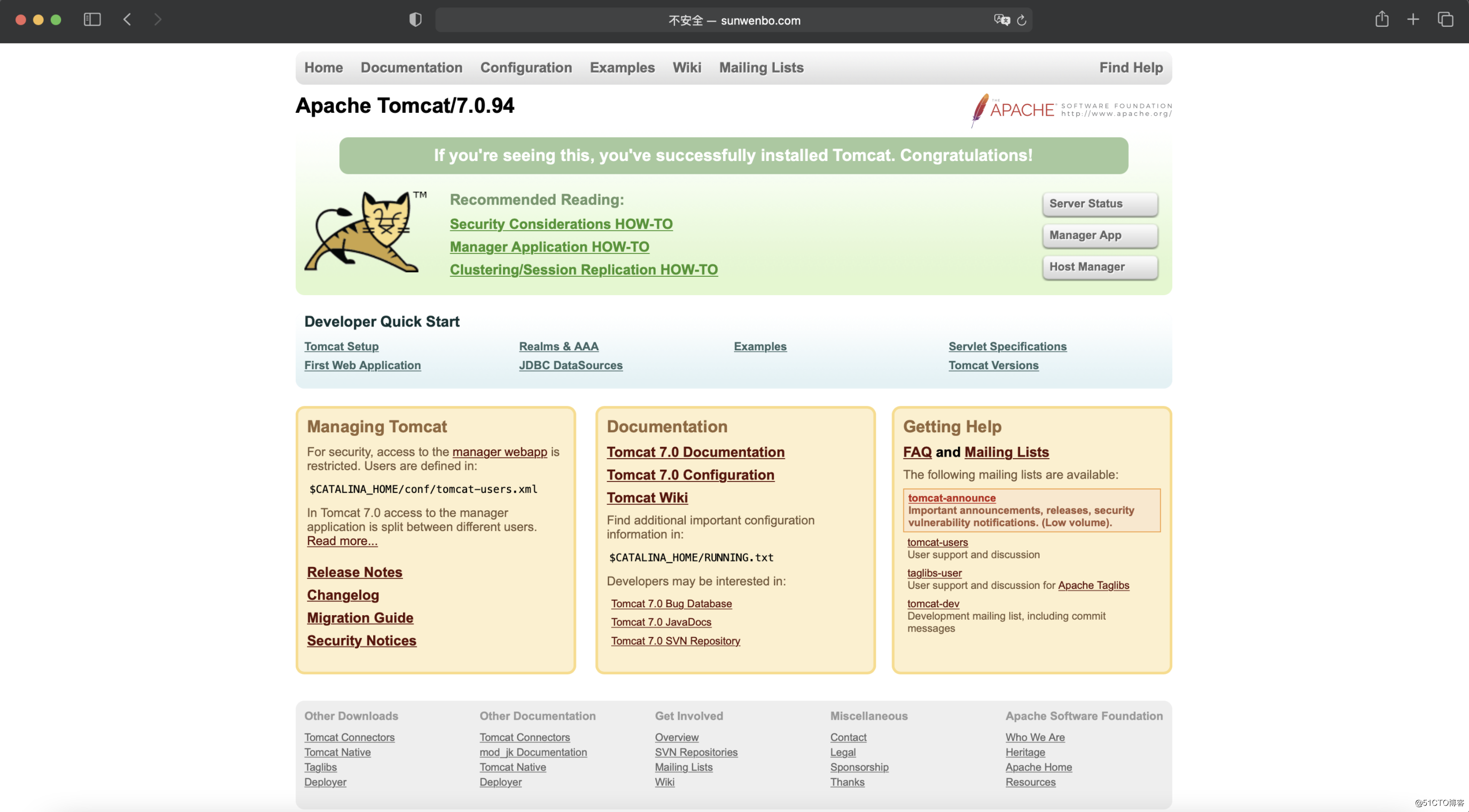
2.3、验证tomcat服务
http://www.sunwenbo.com:32080
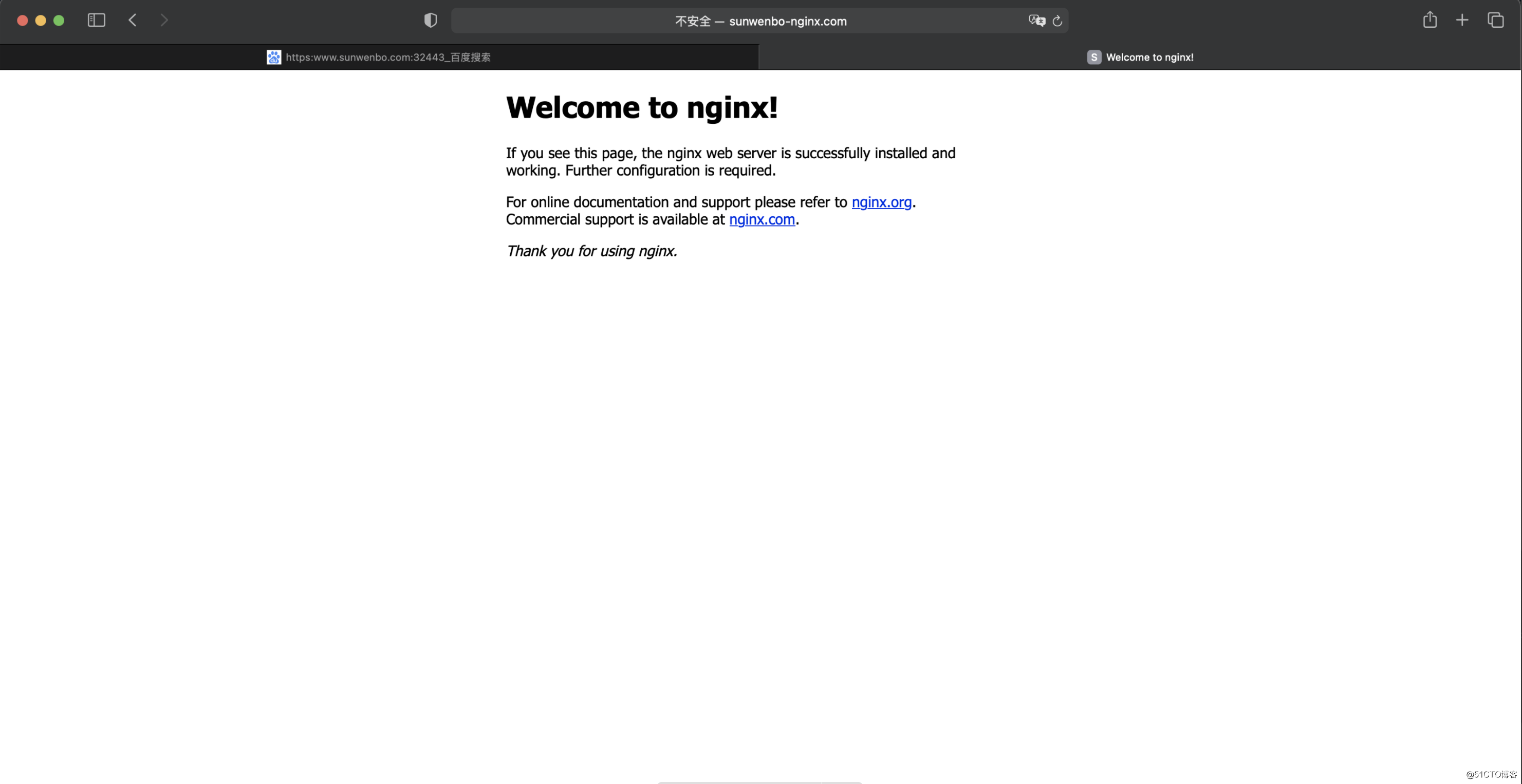
http://www.sunwenbo-nginx.com:32080
3、Https访问验证,创建私有证书及secret
openssl genrsa -out tls.key 2048 #执行成功后,该目录下会生成tls.key文件 openssl req -new -x509 -key tls.key -out tls.crt -subj /C=CN/ST=GD/L=SZ/O=FSI/CN=www.sunwenbo.com #域名必须为提供服务的域名, 执行成功后,该目录下会生成 tls.crt文件 kubectl create secret tls tomcat-secret --cert=tls.crt --key=tls.key #创建名称为tomcat-secret的secret文件 kubectl get secrets #检查创建的secret文件:
3.2、将证书应用至tomcat服务中
apiVersion: extensions/v1beta1 kind: Ingress metadata: name: ingress-tomcat-tls namespace: default annotations: kubernets.io/ingress.class: "nginx" spec: tls: - hosts: - www.sunwenbo.com #与secret证书的域名需要保持一致 secretName: tomcat-secret #secret证书的名称 rules: - host: www.sunwenbo.com http: paths: - path: backend: serviceName: tomcat servicePort: 8080 kubectl apply -f ingress-tomcat-tls.yaml #运行该文件 kubectl get ingress #检查生成的ingress信息
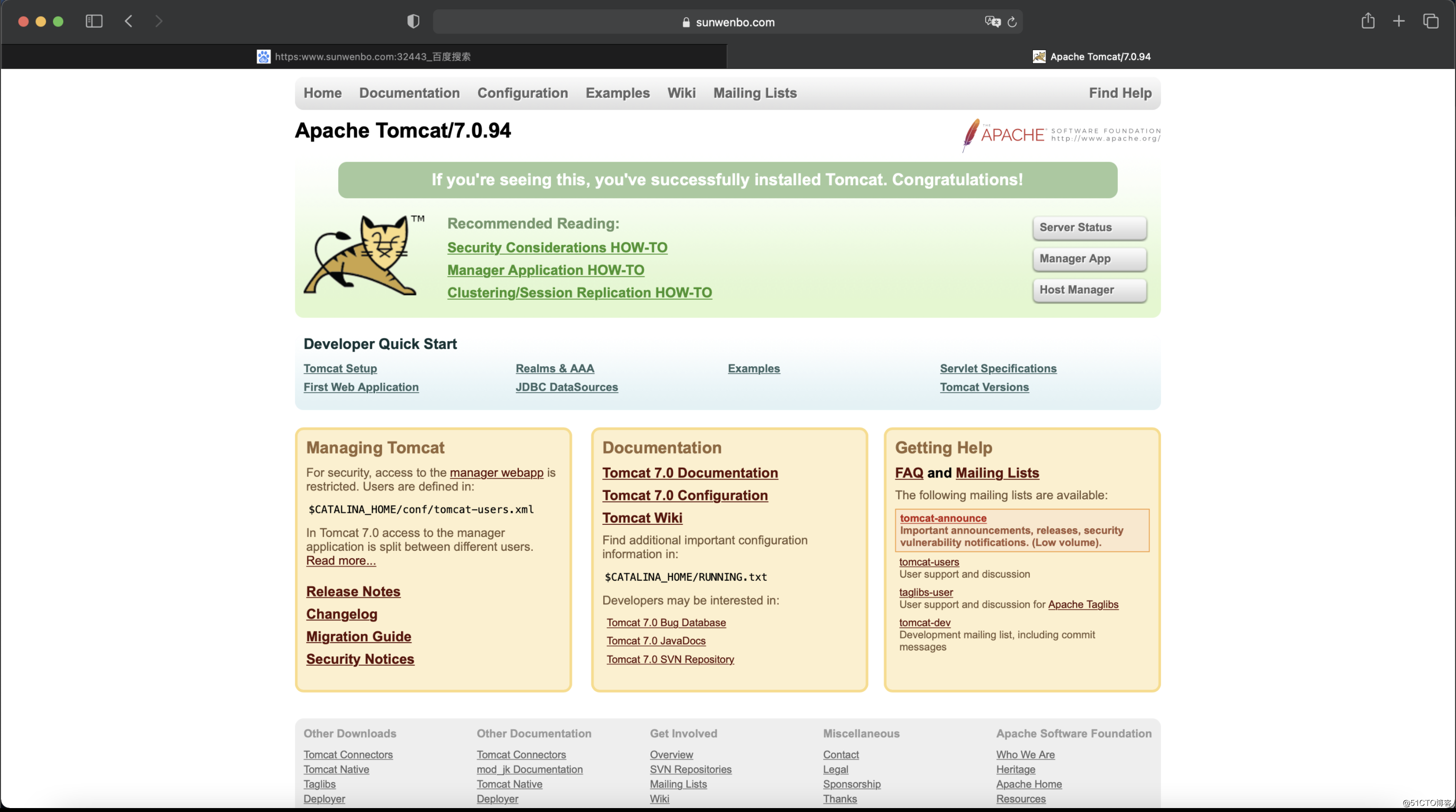
3.3、Https访问tomcat服务
https://www.sunwenbo.com:32443
- Nginx简介及使用Nginx实现负载均衡的原理
- Nginx简介及使用Nginx实现负载均衡的原理【通俗易懂,言简意赅】
- Nginx简介及使用Nginx实现负载均衡的原理【通俗易懂,言简意赅】
- Nginx简介及使用Nginx实现负载均衡的原理【通俗易懂,言简意赅】
- Nginx简介及使用Nginx实现负载均衡的原理【通俗易懂,言简意赅】【转】
- Nginx简介及使用Nginx实现负载均衡的原理
- Nginx简介及使用Nginx实现负载均衡的原理【通俗易懂,言简意赅】
- Nginx简介及使用Nginx实现负载均衡的原理
- Ingress-nginx 部署使用
- Nginx简介及使用Nginx实现负载均衡的原理【通俗易懂,言简意赅】
- 【Nginx】Nginx简介及使用Nginx实现负载均衡的原理【通俗易懂,言简意赅】
- 【转载】Nginx简介及使用Nginx实现负载均衡的原理
- MVC框架之—Struts原理简介与简单开发流程部署
- kafka入门:简介、使用场景、设计原理、主要配置及集群搭建--转载
- 使用Nginx Upstream 部署 OpenERP
- ubuntu下使用nginx部署Laravel
- android源码中ccache使用及原理简介
- 高性能Web服务器Nginx的配置与部署研究(1)Nginx简介及入门示例
- 使用nginx反向代理后,获取用户ip及原理解释
- Android平台APK分析工具包androguard的部署使用和原理分析
