对haproxy代理流程的数据进行抓包分析
2013-01-26 22:46
369 查看
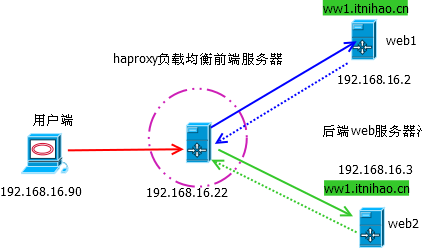
对haproxy代理流程的数据进行抓包分析
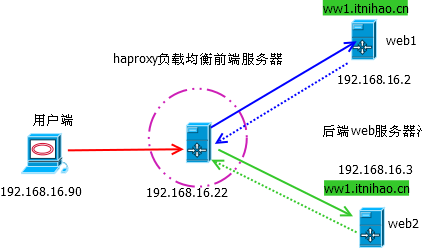
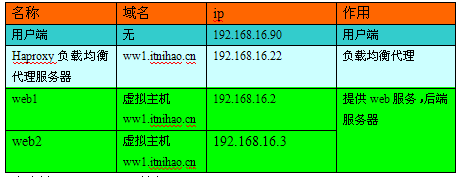
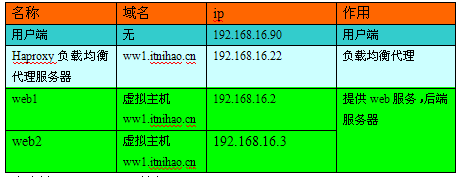
各模块名称以及作用
客户端192.168.16.90访问http://ww1.itnihao.cn
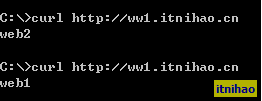
Haproxy的日志如下,可以看到,负载均衡到web2和web1上面去了
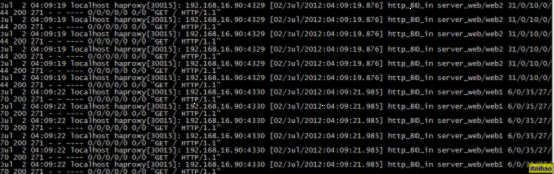
详细日志如下所示
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
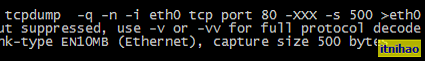
在haproxy 192.168.16.22上面抓包【勘误】
(2012-07-31修改此处,原文是“在web2上面抓包”,其实下面的数据是在3台机器上面的,即haproxy,web1,web2上面抓包的结果分析)
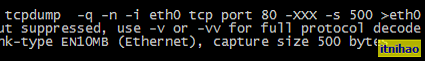
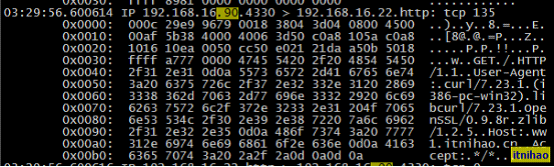
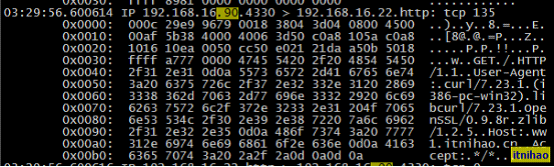
查看抓包数据如下
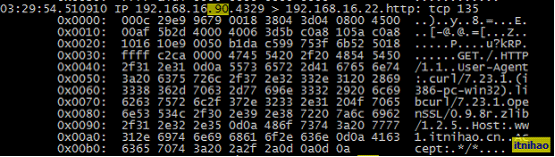
客户端192.168.16.90首先向ww1.itnihao.cn(192.168.16.22)发送请求,haproxy代理服务器192.168.16.22收到请求,根据以下的配置文件的则,将请求用调度算法roundrobin转发给后端web2,即192.168.16.3
frontend http_80_in
bind 0.0.0.0:80
mode http
log global
option httplog
option httpclose
option forwardfor
acl itnihao_web hdr_reg(host) -i ^(www.itnihao.cn|ww1.itnihao.cn)$
use_backend server_web if itnihao_web
backend server_web
mode http
balance roundrobin
cookie SERVERID
option httpchk GET /index.html
server web1 192.168.16.2:80 cookie web1 check inter 1500 rise 3 fall 3 weight 1
server web2 192.168.16.3:80 cookie web2 check inter 1500 rise 3 fall 3 weight 2
可以看到,haproxy会将请求的www.itnihao.cn转发给192.168.16.3,且标记客户端的ip,如192.168.16.3有多个基于域名的虚拟主机,可以通过请求的域名来正确的识别到虚拟主机,这点无需担心
ip转发的选项是option forwardfor 转发过来的ip,如此,则端服务器可以获取到真实的客户端ip,
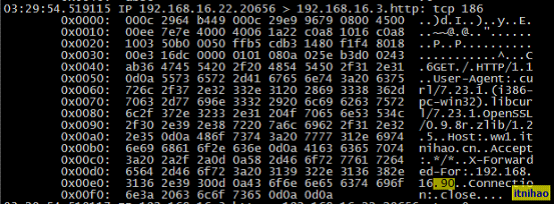
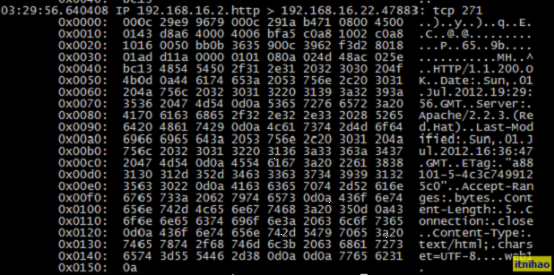
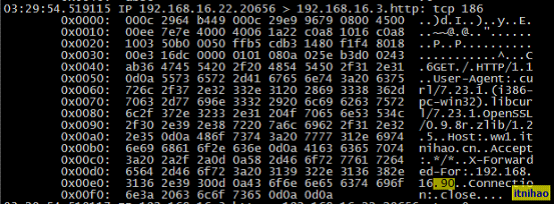
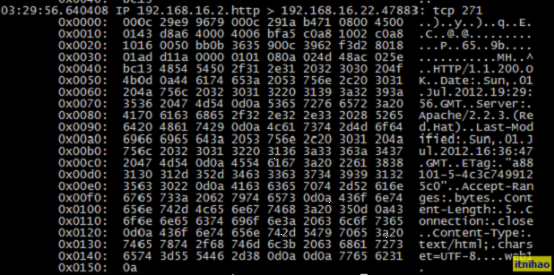
192.168.16.3响应haproxy的请求,将数据index.html提供给haproxy192.168.16.22
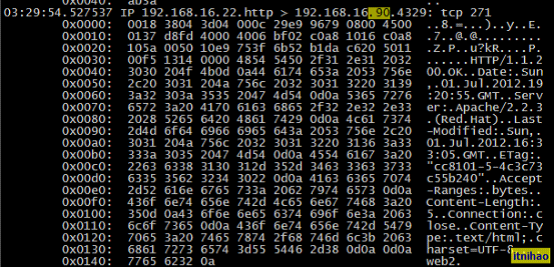
代理过程完成,192.168.16.22将index.html数据发送给用户端,用户端192.168.16.90完成此次的服务器请求,对用户来说是完全透明的。
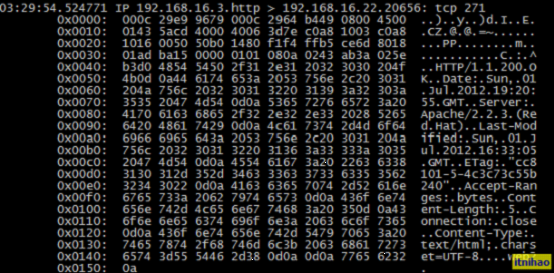
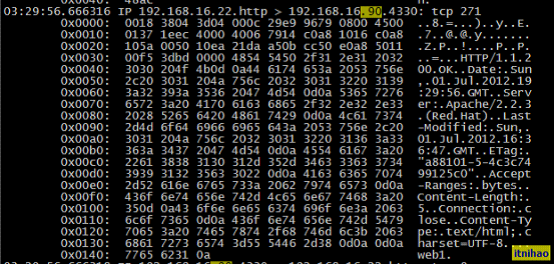
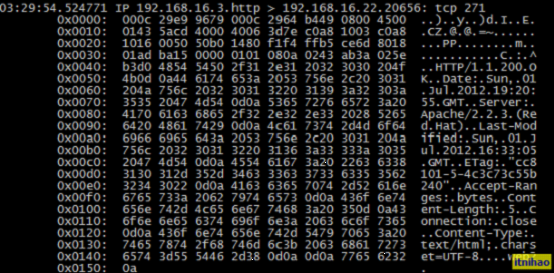
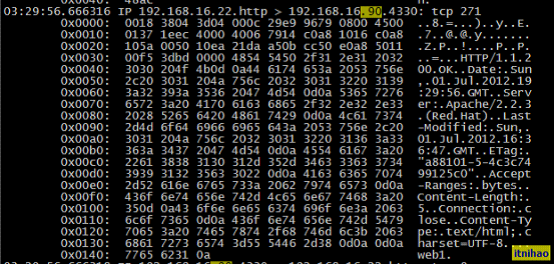
同理,代理将请求转发给192.168.16.2,叙述过程不再重复,从抓包数据的结果可以看到

以上内容为本人对haproxy的一些理解,如有误差,欢迎各位指正!
另外附录两篇对haproxy代码的分析链接
本文出自 “itnihao的运维技术博客” 博客,请务必保留此出处/article/4292623.html 骨灰盒 www.dynymd.com 骨灰盒 www.dyqkgy.com
各模块名称以及作用
haproxy.cfg文件配置如下
global maxconn 20480 log 127.0.0.1 local3 chroot /var/haproxy uid 99 gid 99 daemon nbproc 1 pidfile /var/run/haproxy.pid ulimit-n 65535 defaults log global mode http maxconn 20480 option httplog option httpclose option dontlognull option forwardfor option redispatch option abortonclose stats refresh 30 retries 3 balance roundrobin contimeout 5000 clitimeout 50000 srvtimeout 50000 timeout check 2000 listen admin_status bind 0.0.0.0:65532 mode http log 127.0.0.1 local3 err stats refresh 5s stats uri /admin?stats stats realm itnihao\ itnihao stats auth admin:admin stats auth admin1:admin1 stats hide-version stats admin if TRUE errorfile 403 /etc/haproxy/errorfiles/403.http errorfile 500 /etc/haproxy/errorfiles/500.http errorfile 502 /etc/haproxy/errorfiles/502.http errorfile 503 /etc/haproxy/errorfiles/503.http errorfile 504 /etc/haproxy/errorfiles/504.http capture request header Host len 40 capture request header Content-Length len 10 capture request header Referer len 200 capture response header Server len 40 capture response header Content-Length len 10 capture response header Cache-Control len 8 listen site_status bind 0.0.0.0:1081 mode http log 127.0.0.1 local3 err monitor-uri /site_status acl site_dead nbsrv(server_web) lt 2 monitor fail if site_dead frontend http_80_in bind 0.0.0.0:80 mode http log global option httplog option httpclose option forwardfor acl itnihao_web hdr_reg(host) -i ^(www.itnihao.cn|ww1.itnihao.cn)$ acl itnihao_blog hdr_dom(host) -i blog.itnihao.cn use_backend server_web if itnihao_web use_backend server_blog if itnihao_blog default_backend server_bbs backend server_web mode http balance roundrobin cookie SERVERID option httpchk GET /index.html server web1 192.168.16.2:80 cookie web1 check inter 1500 rise 3 fall 3 weight 1 server web2 192.168.16.3:80 cookie web2 check inter 1500 rise 3 fall 3 weight 2 backend server_bbs mode http balance roundrobin cookie SERVERID option httpchk GET /index.html server bbs1 192.168.16.2:80 cookie bbs1 check inter 1500 rise 3 fall 3 weight 1 server bbs2 192.168.16.3:80 cookie bbs2 check inter 1500 rise 3 fall 3 weight 2
客户端192.168.16.90访问http://ww1.itnihao.cn
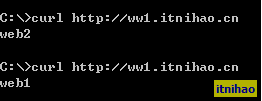
Haproxy的日志如下,可以看到,负载均衡到web2和web1上面去了
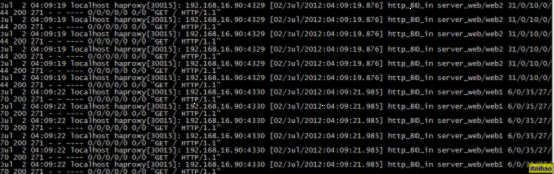
详细日志如下所示
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:19 localhost haproxy[30015]: 192.168.16.90:4329 [02/Jul/2012:04:09:19.876] http_80_in server_web/web2 31/0/10/0/44 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
Jul 2 04:09:22 localhost haproxy[30015]: 192.168.16.90:4330 [02/Jul/2012:04:09:21.985] http_80_in server_web/web1 6/0/35/27/70 200 271 - - ---- 0/0/0/0/0 0/0 "GET / HTTP/1.1"
在haproxy 192.168.16.22上面抓包【勘误】
(2012-07-31修改此处,原文是“在web2上面抓包”,其实下面的数据是在3台机器上面的,即haproxy,web1,web2上面抓包的结果分析)
查看抓包数据如下
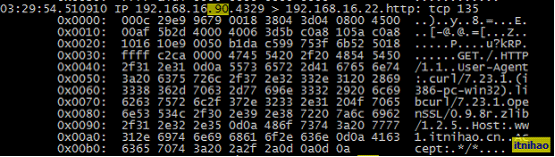
客户端192.168.16.90首先向ww1.itnihao.cn(192.168.16.22)发送请求,haproxy代理服务器192.168.16.22收到请求,根据以下的配置文件的则,将请求用调度算法roundrobin转发给后端web2,即192.168.16.3
frontend http_80_in
bind 0.0.0.0:80
mode http
log global
option httplog
option httpclose
option forwardfor
acl itnihao_web hdr_reg(host) -i ^(www.itnihao.cn|ww1.itnihao.cn)$
use_backend server_web if itnihao_web
backend server_web
mode http
balance roundrobin
cookie SERVERID
option httpchk GET /index.html
server web1 192.168.16.2:80 cookie web1 check inter 1500 rise 3 fall 3 weight 1
server web2 192.168.16.3:80 cookie web2 check inter 1500 rise 3 fall 3 weight 2
可以看到,haproxy会将请求的www.itnihao.cn转发给192.168.16.3,且标记客户端的ip,如192.168.16.3有多个基于域名的虚拟主机,可以通过请求的域名来正确的识别到虚拟主机,这点无需担心
ip转发的选项是option forwardfor 转发过来的ip,如此,则端服务器可以获取到真实的客户端ip,
192.168.16.3响应haproxy的请求,将数据index.html提供给haproxy192.168.16.22
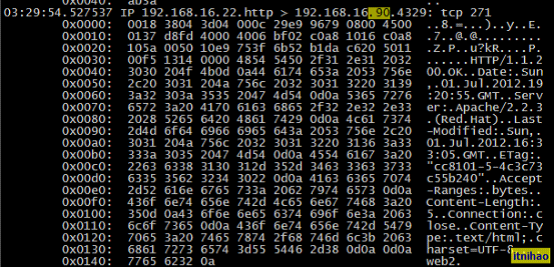
代理过程完成,192.168.16.22将index.html数据发送给用户端,用户端192.168.16.90完成此次的服务器请求,对用户来说是完全透明的。
同理,代理将请求转发给192.168.16.2,叙述过程不再重复,从抓包数据的结果可以看到

以上内容为本人对haproxy的一些理解,如有误差,欢迎各位指正!
另外附录两篇对haproxy代码的分析链接
http://blog.csdn.net/chen_jianjian/article/details/7303909 haproxy工作流程分析 http://blog.csdn.net/chen_jianjian/article/details/7317758 haproxy初始化函数分析
本文出自 “itnihao的运维技术博客” 博客,请务必保留此出处/article/4292623.html 骨灰盒 www.dynymd.com 骨灰盒 www.dyqkgy.com
相关文章推荐
- haproxy代理流程的数据进行抓包分析
- 对haproxy代理流程的数据进行抓包分析
- 对haproxy代理流程的数据进行抓包分析
- QPBOC交易流程详解--POS与卡片的数据交互进行分析
- Fiddler怎么对IPhone手机的数据进行抓包分析
- QPBOC交易流程详解--POS与卡片的数据交互进行分析
- PBOC/EMV-交易流程详解--POS与卡片的数据交互进行分析
- 使用Fiddler对Android手机的应用数据进行抓包分析
- QPBOC交易流程详解--POS与卡片的数据交互进行分析
- QPBOC交易流程详解--POS与卡片的数据交互进行分析
- 使用Fiddler对iPhone苹果手机进行数据抓包分析
- PBOC/EMV-交易流程详解--POS与卡片的数据交互进行分析
- PBOC/EMV-交易流程详解--POS与卡片的数据交互进行分析
- Fiddler怎么对IPhone手机的数据进行抓包分析
- Fiddler怎么对IPhone手机的数据进行抓包分析
- QPBOC交易流程详解--POS与卡片的数据交互进行分析
- QPBOC交易流程详解--POS与卡片的数据交互进行分析
- Fiddler怎么对IPhone手机的数据进行抓包分析
- Fiddler怎么对IPhone手机的数据进行抓包分析
- QPBOC交易流程详解--POS与卡片的数据交互进行分析
